

Rocheston Certified SOC Analyst
The course goes beyond theory, offering a blend of practical exercises and real-world simulations. You'll learn by doing, putting your newfound knowledge to the test in scenarios that mimic the fast-paced environment of a real SOC.
The program covers all aspects of SOC operations, including security incident detection and response (SIEDR), threat analysis, log management, and incident reporting. You'll explore the latest cybersecurity tools and technologies used in today's SOCs, learning to leverage them efficiently to identify, analyze, and respond to security threats.
By the end of the course, you'll be a confident and capable SOC Analyst, equipped to protect your organization from today's ever-evolving cyber threats. The course also prepares you for the Rocheston Certified SOC Analyst (RSOC) exam, a valuable credential demonstrating your proficiency in SOC operations.


Target Audience
- IT security professionals seeking a career in SOC operations
- Network security analysts looking to expand their skillset
- Security professionals transitioning to a SOC analyst role
- Anyone interested in gaining a comprehensive understanding of SOC operations
Their expertise is in high demand for a confluence of reasons. The battlefield of cyber threats is a constantly shifting landscape, demanding analysts with the keen eye to identify and neutralize these evolving attack methods. Secondly, a talent shortage plagues the cybersecurity industry, creating a competitive job market where skilled SOC analysts are highly sought-after assets.
Beyond acting as reactive firefighters, SOC analysts play a crucial, proactive role. They become digital hunters, actively seeking out potential threats, meticulously analyzing vulnerabilities, and taking preventative measures to thwart attacks before they can wreak havoc. This proactive approach minimizes downtime and safeguards the crown jewels – our critical data.
The skills honed as a SOC analyst are highly versatile, translating seamlessly across various cybersecurity domains. This adaptability empowers you to explore and potentially specialize in areas like threat hunting, digital forensics, or security engineering, opening doors for a rewarding career trajectory within the ever-evolving landscape of cybersecurity.


Duration
- Duration: 3 days
- Delivery options:
- Instructor-led classroom training (traditional or virtual)
- Blended learning (combination of classroom sessions and online modules)
- Self-paced online learning (optional)
Rocheston Certified SOC Analyst Certification Exam
- Exam Structure:
- Number of Questions: 100
- Format: Multiple Choice, True/False, Short Answer
- Duration: 2 Hours
- Passing Score: 70%
Course Outline for (SOC) Analyst
- Need for SOC and its Role in Cybersecurity
- Definition and purpose of a Security Operations Center
- How SOC fits into the larger cybersecurity landscape
- Evolution of Cyber Threats and Attacks
- Historical overview of significant cyber threats and attacks
- How cyber threats have evolved over time
- Importance of Proactive Security Monitoring
- The concept of proactive vs. reactive security
- Benefits of continuous monitoring for potential security threats
- Benefits of a Centralized SOC
- Centralized data collection and analysis
- Improved incident response times and coordination
- Enhanced visibility across the entire IT environment
- SOC Operations and Analyst Responsibilities
- Key objectives and daily tasks of a SOC Analyst
- Tools and techniques used in daily operations
- Security Event Monitoring and Analysis
- Methods and technologies for monitoring security events
- Techniques for effective event analysis
- Incident Detection, Investigation, and Response (IR)
- Overview of the incident lifecycle
- Roles involved in detection, investigation, and response
- Threat Intelligence Integration and Utilization
- Sources of threat intelligence
- How to integrate and apply threat intelligence in SOC operations
- SOC Team Structure and Collaboration
- Organizational structure of a SOC team
- Roles within a SOC team (e.g., Security Analyst, Incident Responder, Threat Hunter)
- Importance of effective communication and collaboration
- Escalation procedures for critical security incidents
Module 2: Security Information and Event Management (SIEM)
- Introduction to SIEM and Its Functionalities
- Definition, purpose, and key features of SIEM
- Overview of popular SIEM solutions in the market
- Log Collection, Aggregation, and Normalization
- The process of collecting logs from various sources
- Techniques for aggregating and normalizing log data
- Event Correlation and Threat Detection Rules
- Concept of event correlation and its importance
- Creation and fine-tuning of threat detection rules
- Security Dashboards and Reporting
- Utilization of dashboards for monitoring and reporting
- Best practices for creating and interpreting security reports
- Configuring SIEM for log collection from various sources
- Utilizing SIEM for log analysis and threat hunting
- Creating and customizing event correlation rules
- Generating security reports and visualizations
Module 3: Incident Detection and Analysis
- Incident Detection Methodologies
- Signature-Based Detection
- Definition, benefits, and limitations
- Tools and techniques for implementation
- Anomaly-Based Detection
- Definition, benefits, and limitations
- Tools and techniques for implementation
- Threat Intelligence-Driven Detection
- Role of threat intelligence in identifying incidents
- Best practices for integrating threat intelligence
- Incident Analysis Tools and Techniques:
- Network Traffic Analysis (NTA) Tools
- Key tools and techniques for analyzing network traffic
- Endpoint Detection and Response (EDR) Solutions
- Overview of EDR solutions and their importance
- Security Orchestration, Automation, and Response (SOAR) Platforms
- Benefits of using SOAR for incident analysis and response
- Packet Capture and Forensic Analysis
- Techniques for capturing and analyzing network packets
- Forensic analysis methods for identifying incidents
- Simulating security incidents through scenarios
- Analyzing logs and network traffic to identify root cause
- Utilizing security tools for further investigation and evidence collection
- Documenting findings and preparing initial incident reports
Module 4: Incident Response (IR) Process
- NIST Cybersecurity Framework and IR Framework
- Overview of NIST Cybersecurity Framework
- Key components of an Incident Response Framework
- Understanding the Different Phases of Incident Response
- Preparation: Developing and maintaining an IR plan
- Detection: Identifying and reporting incidents
- Containment: Limiting the impact of the incident
- Eradication: Eliminating the root cause of the incident
- Recovery: Restoring systems and operations to normal
- Post-Incident Review: Analyzing the incident and improving future response
- Aligning SOC Operations with Industry Best Practices
- Best practices for aligning SOC operations with established frameworks
- Incident Response Procedures and Best Practices
- Detailed procedures for each phase of incident response
- Best practices for effective and efficient incident handling
- Incident Response Playbooks and Communication Strategies
- Developing and documenting incident response playbooks for different scenarios
- Effective communication with stakeholders during a security incident
Module 5: Network Security Fundamentals
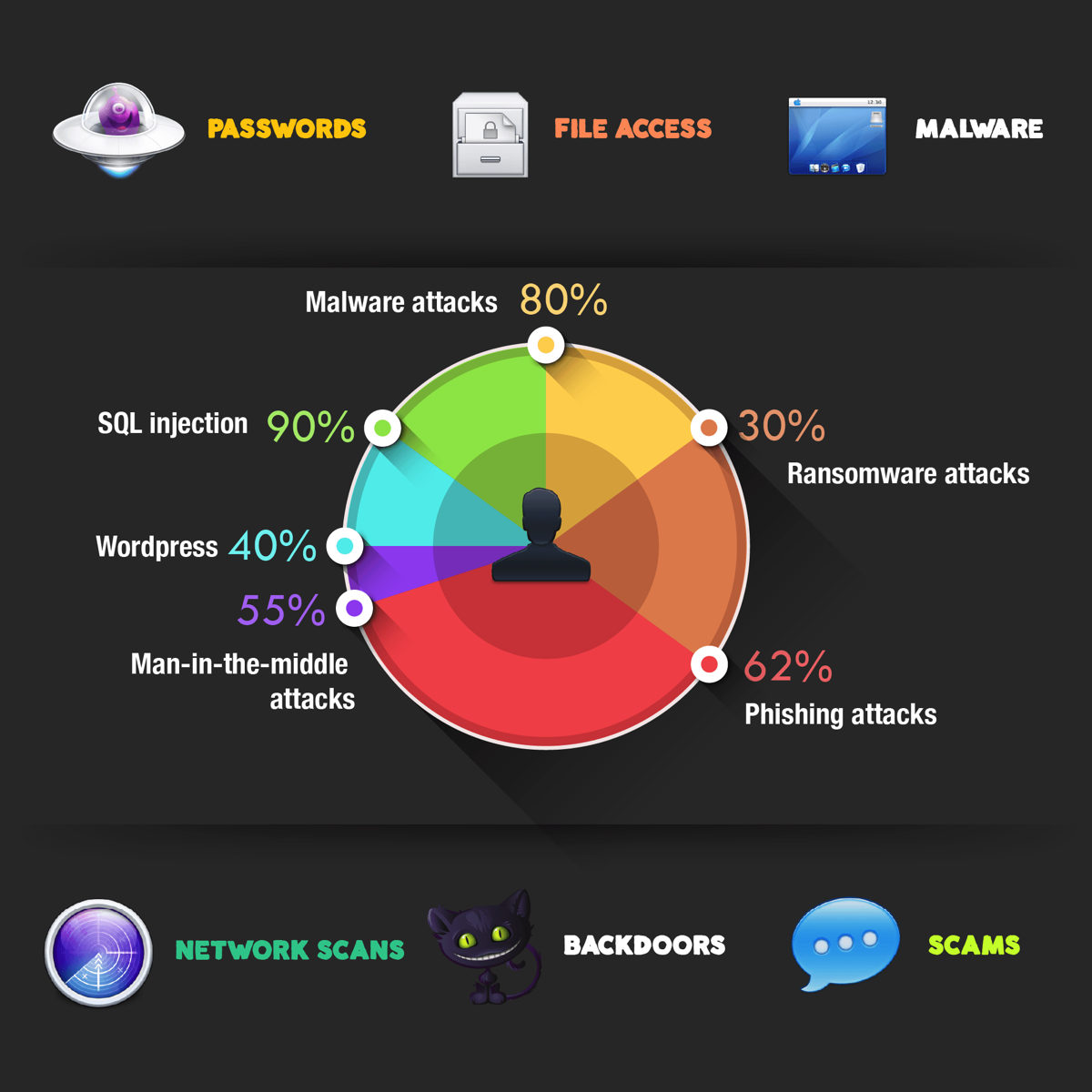
- Network Security Threats and Vulnerabilities
- Overview of common network attacks (e.g., Denial-of-Service (DoS), Man-in-the-Middle (MitM), SQL Injection)
- Understanding network vulnerabilities and exploits
- Network Security Controls and Tools
- Firewalls: Types, configurations, and management
- Intrusion Detection Systems (IDS)/Intrusion Prevention Systems (IPS): Functions and deployment
- Network Segmentation and Access Control: Best practices and implementation
- Vulnerability Scanning and Patching: Tools and techniques
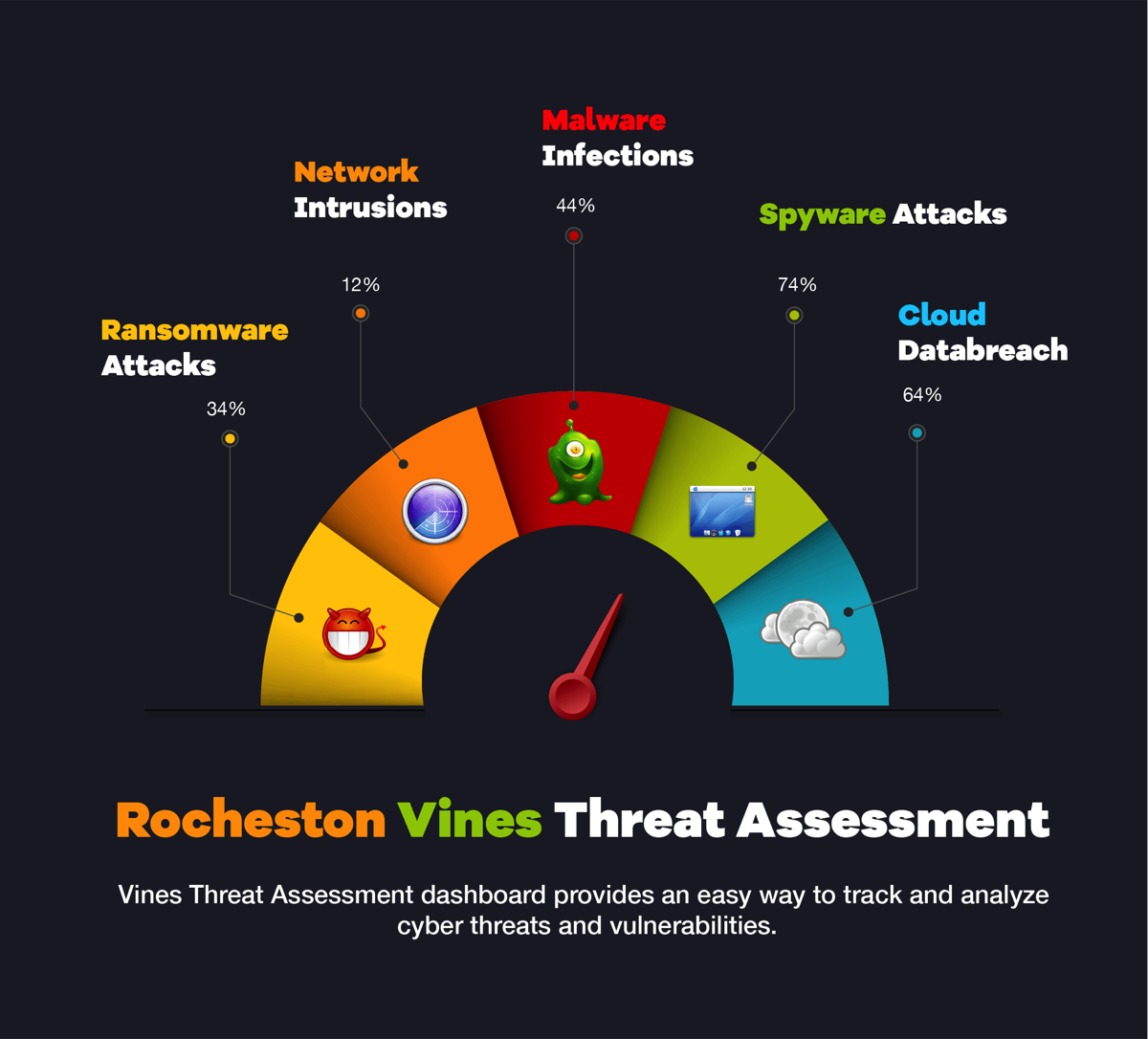
Module 6: Threat Analysis
- Understanding the Threat Landscape
- Identifying different types of cyber threats (e.g., ransomware, phishing, APTs)
- Current trends and emerging threats
- Threat Modeling and Analysis
- Techniques for building and utilizing threat models
- Assessing the potential impact and likelihood of threats
- Risk Assessment and Mitigation
- Understanding risk management frameworks (e.g., FAIR, OCTAVE)
- Techniques for assessing and mitigating cyber risks
- Threat Intelligence Gathering and Utilization
- Sources of threat intelligence (e.g., open-source, commercial, ISACs)
- Methods for integrating threat intelligence into SOC operations
- Hands-On Threat Analysis Exercises
- Conducting threat assessments using real-world scenarios
- Utilizing threat models to analyze specific threats
- Developing mitigation strategies based on threat analysis
Module 7: Threat Hunting
- Introduction to Threat Hunting
- Definition and importance of threat hunting in a SOC
- Differences between threat hunting and traditional detection methods
- Threat Hunting Methodologies
- Hypothesis-driven threat hunting
- Data-driven threat hunting
- Techniques-driven threat hunting
- Tools and Techniques for Threat Hunting
- Using SIEM, EDR, and other security tools in threat hunting
- Developing and utilizing custom scripts and analytics
- Automating Threat Hunting
- Leveraging automation tools and platforms for threat hunting
- Benefits and challenges of automated threat hunting
- Hands-on Threat Hunting Exercises
- Developing hypotheses and hunting for threats in simulated environments
- Utilizing various tools and techniques for effective threat hunting
- Documenting findings and reporting on threat hunting activities
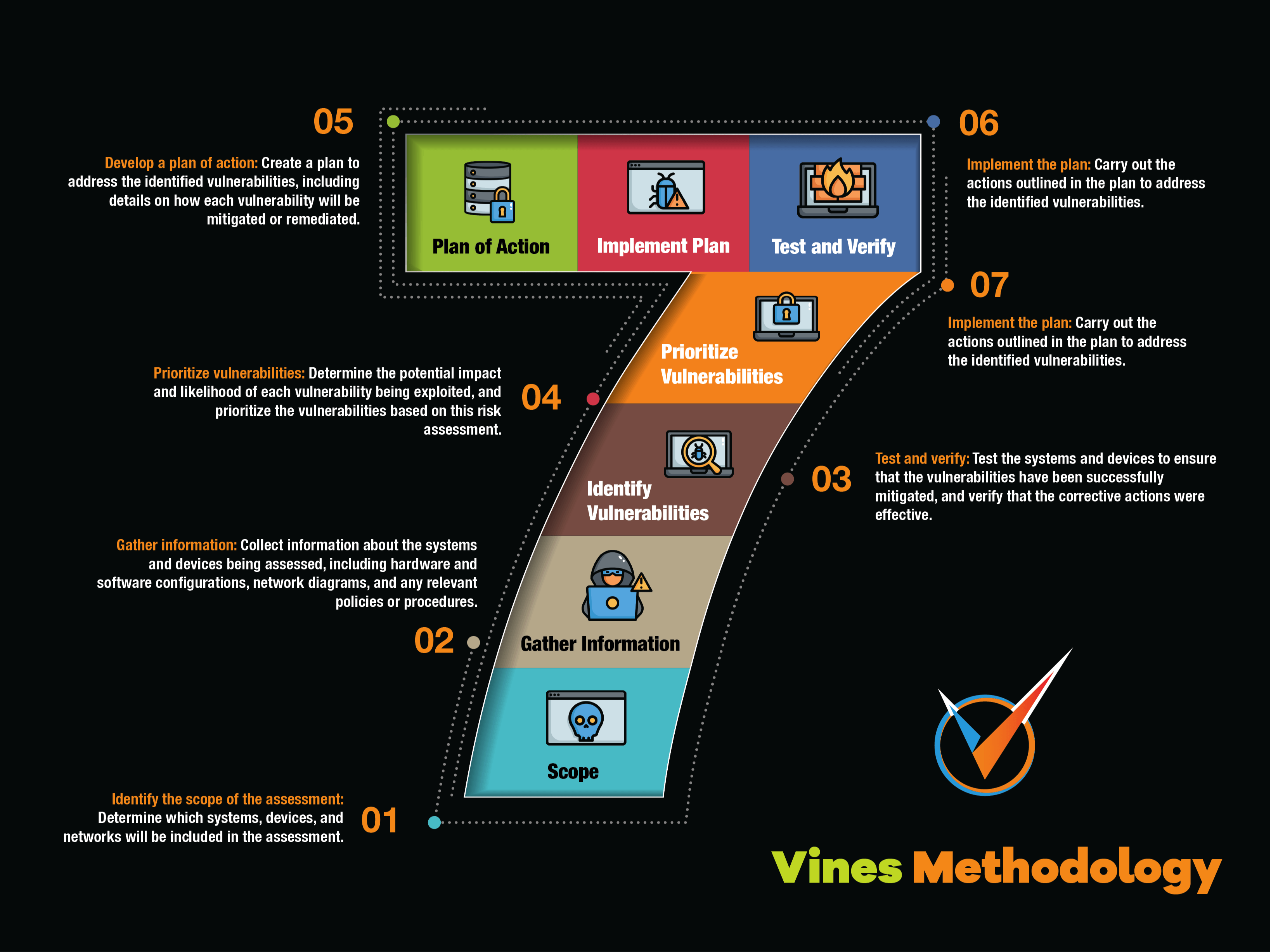
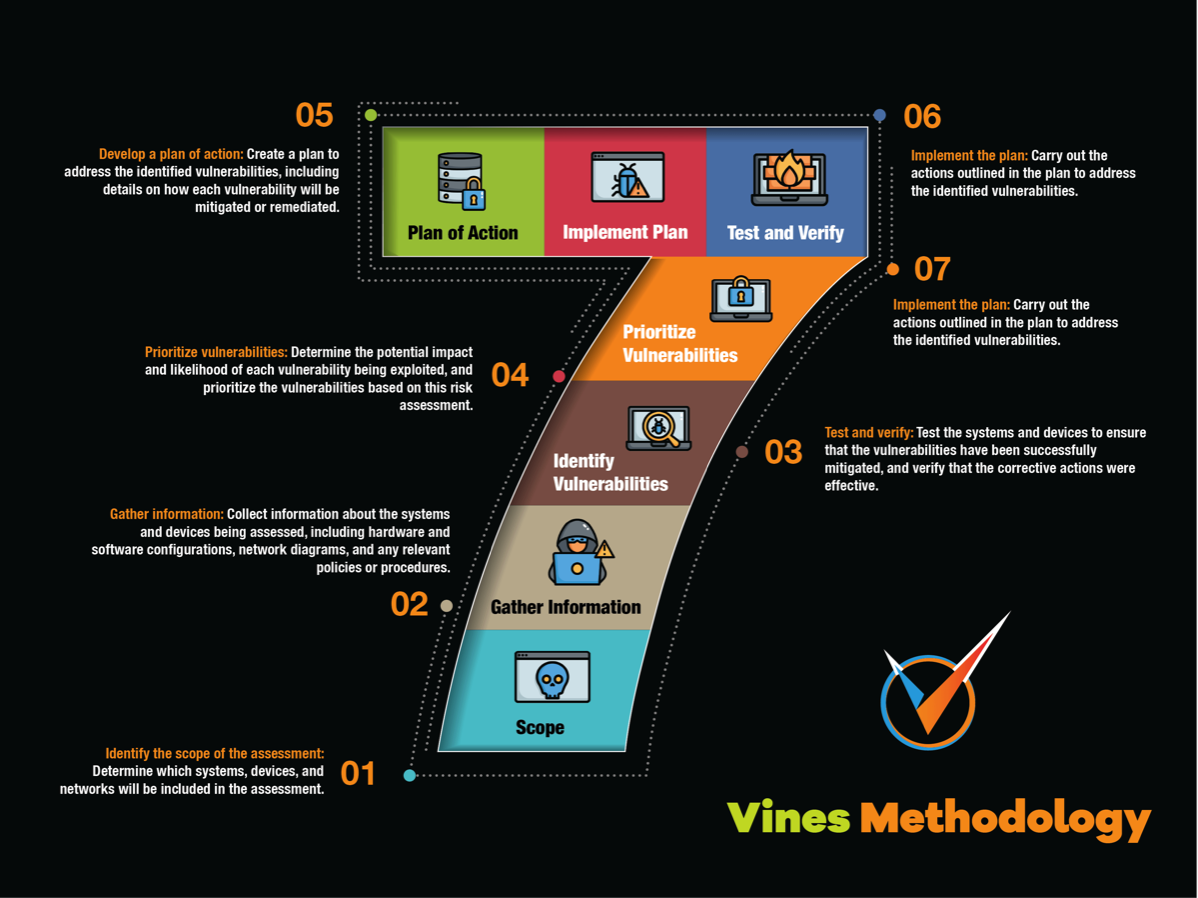
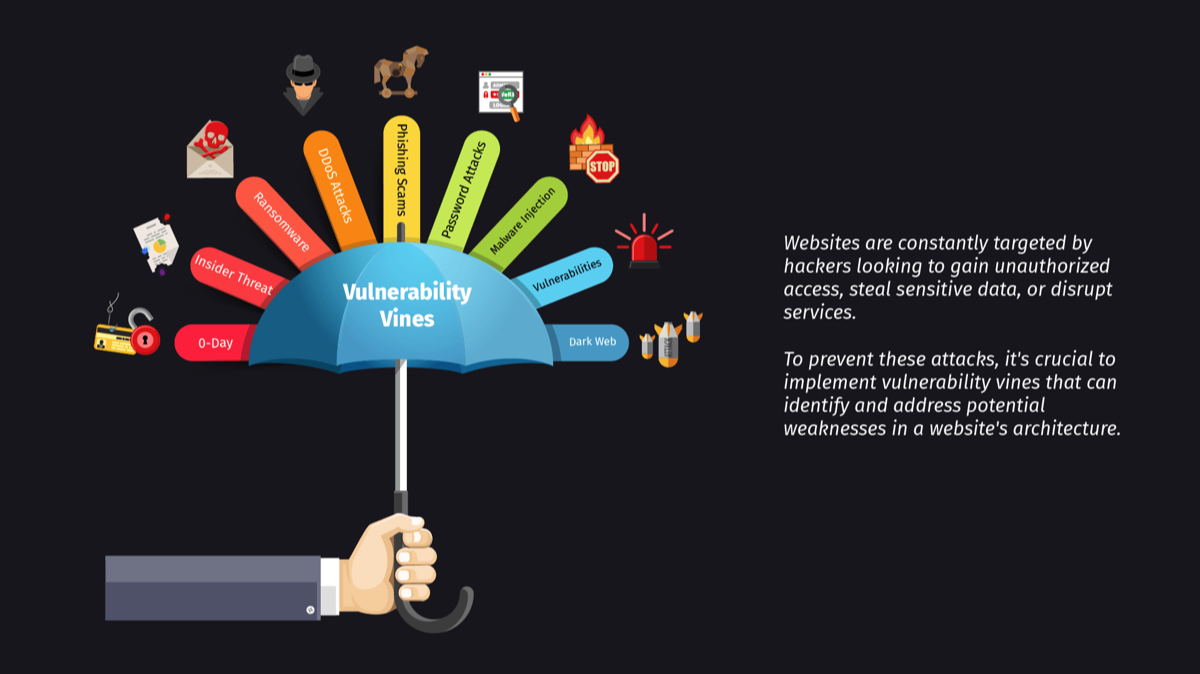
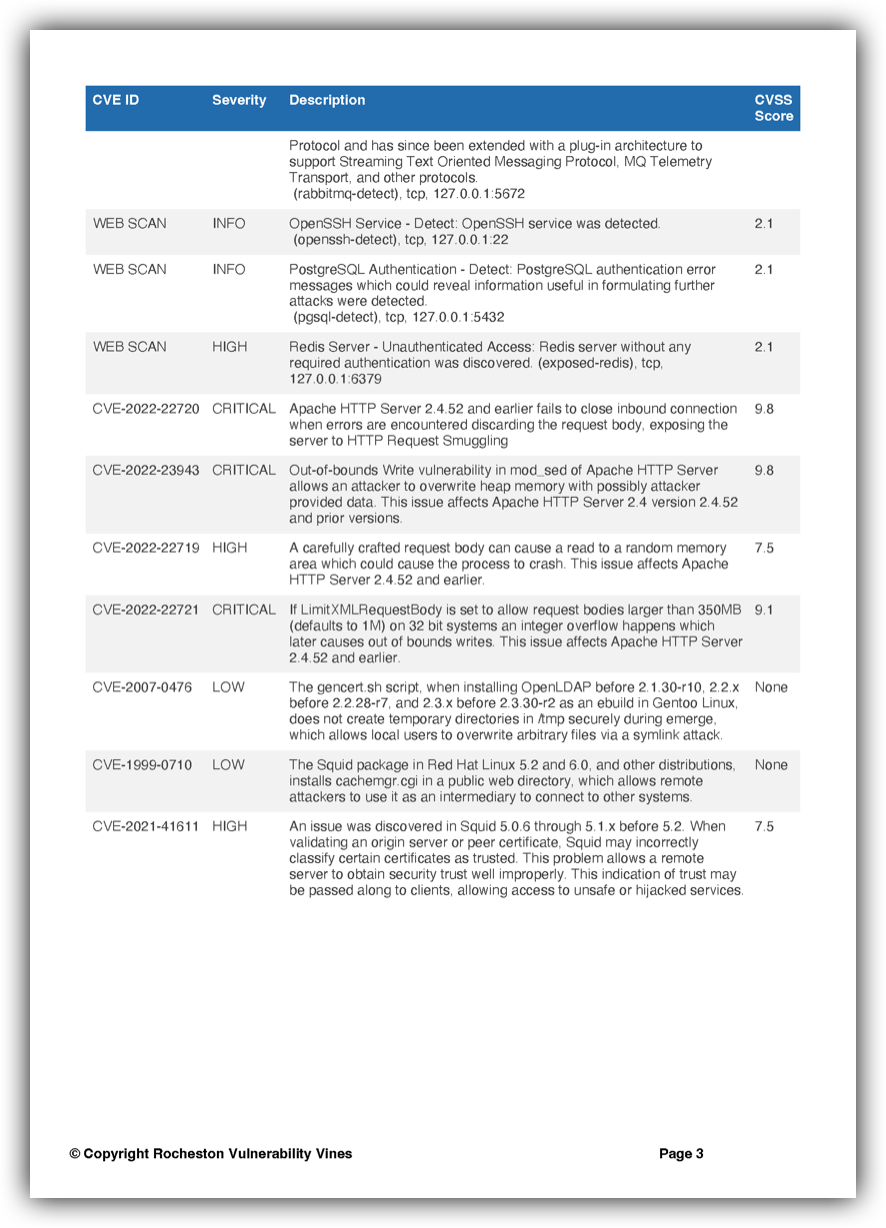
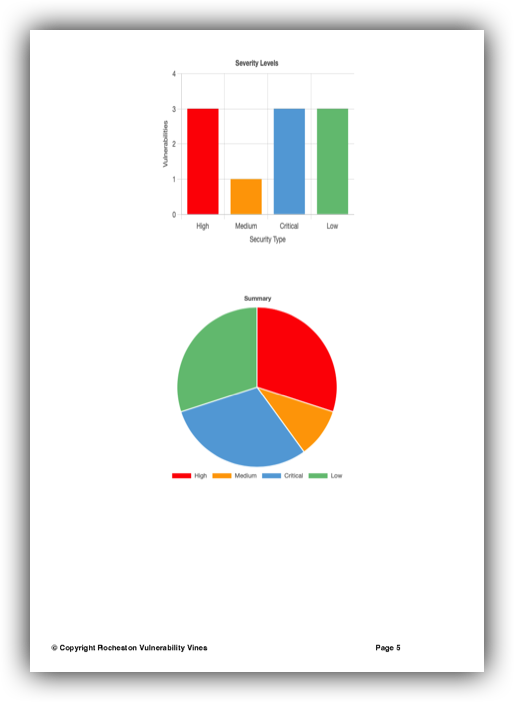
Module 8: Rocheston Vulnerability Vines
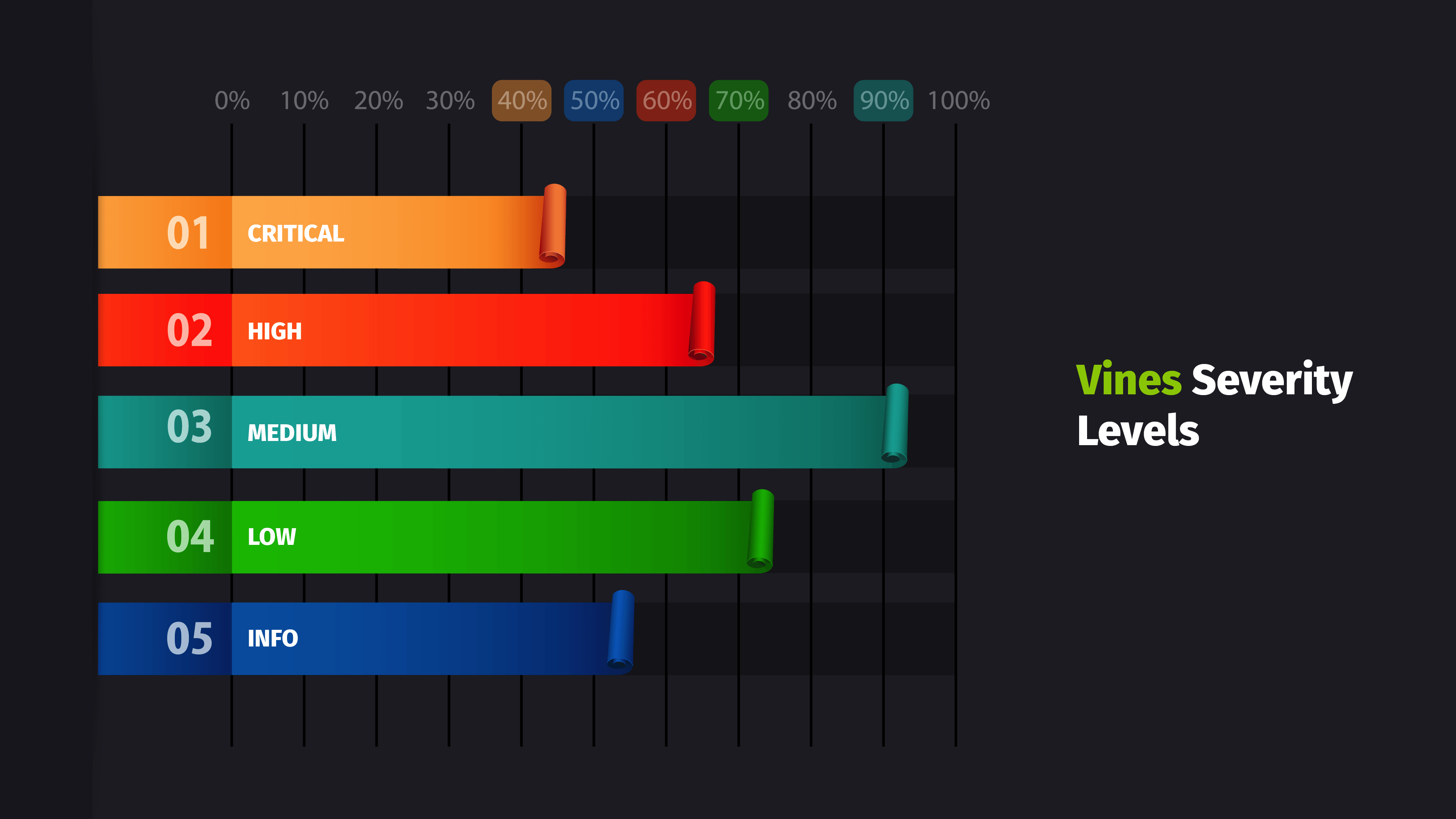
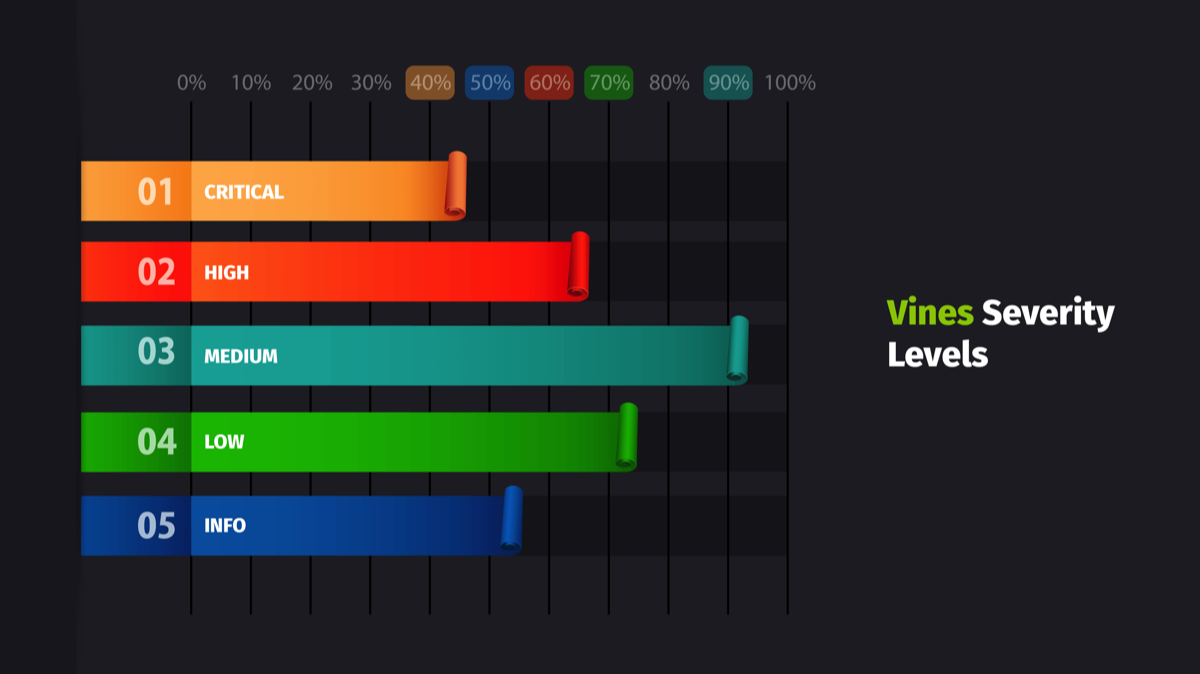
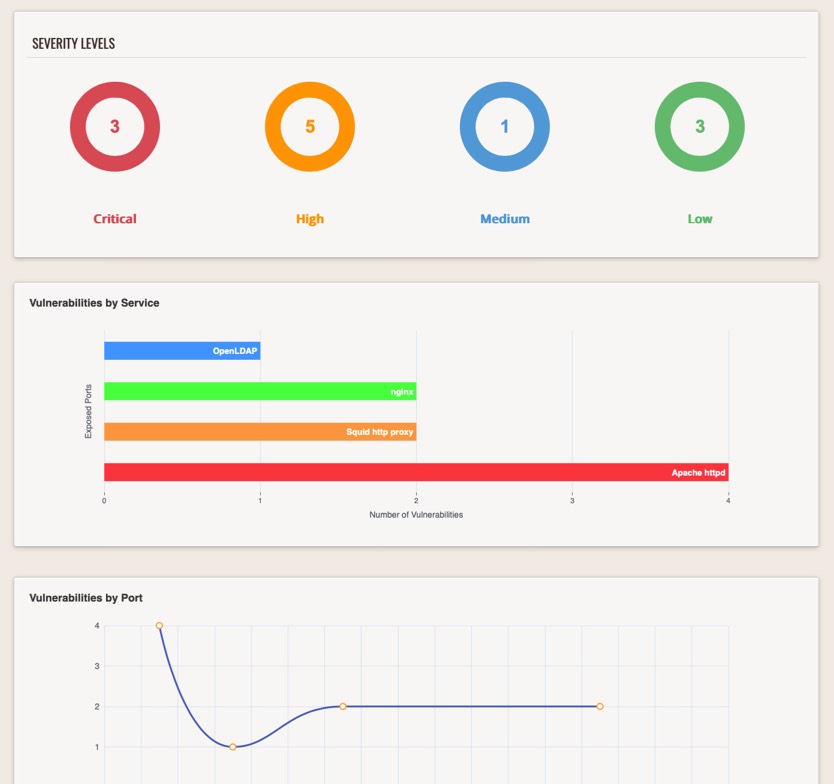
- Identifying and Prioritizing Vulnerabilities
- Techniques for identifying vulnerabilities in systems
- Methods for prioritizing vulnerabilities based on risk
- Vulnerability Management Processes
- Establishing a vulnerability management workflow
- Tools and best practices for vulnerability assessment
- Remediation and Mitigation Strategies
- Approaches for remediating identified vulnerabilities
- Methods for mitigating the impact of vulnerabilities
Module 9: Rocheston Cybersecurity Framework
- Introduction to Rocheston Cybersecurity Framework
- Overview and key components
- Importance in modern cybersecurity landscape
- Implementation of Rocheston Framework
- Step-by-step guide to implementing the framework in an organization
- Assessment and Maturity Models
- Techniques for assessing the current state of cybersecurity
- Maturity models to measure and improve cybersecurity posture
- Case Studies and Best Practices
- Real-world examples of successful implementation of Rocheston Framework
- Best practices and lessons learned from various industries
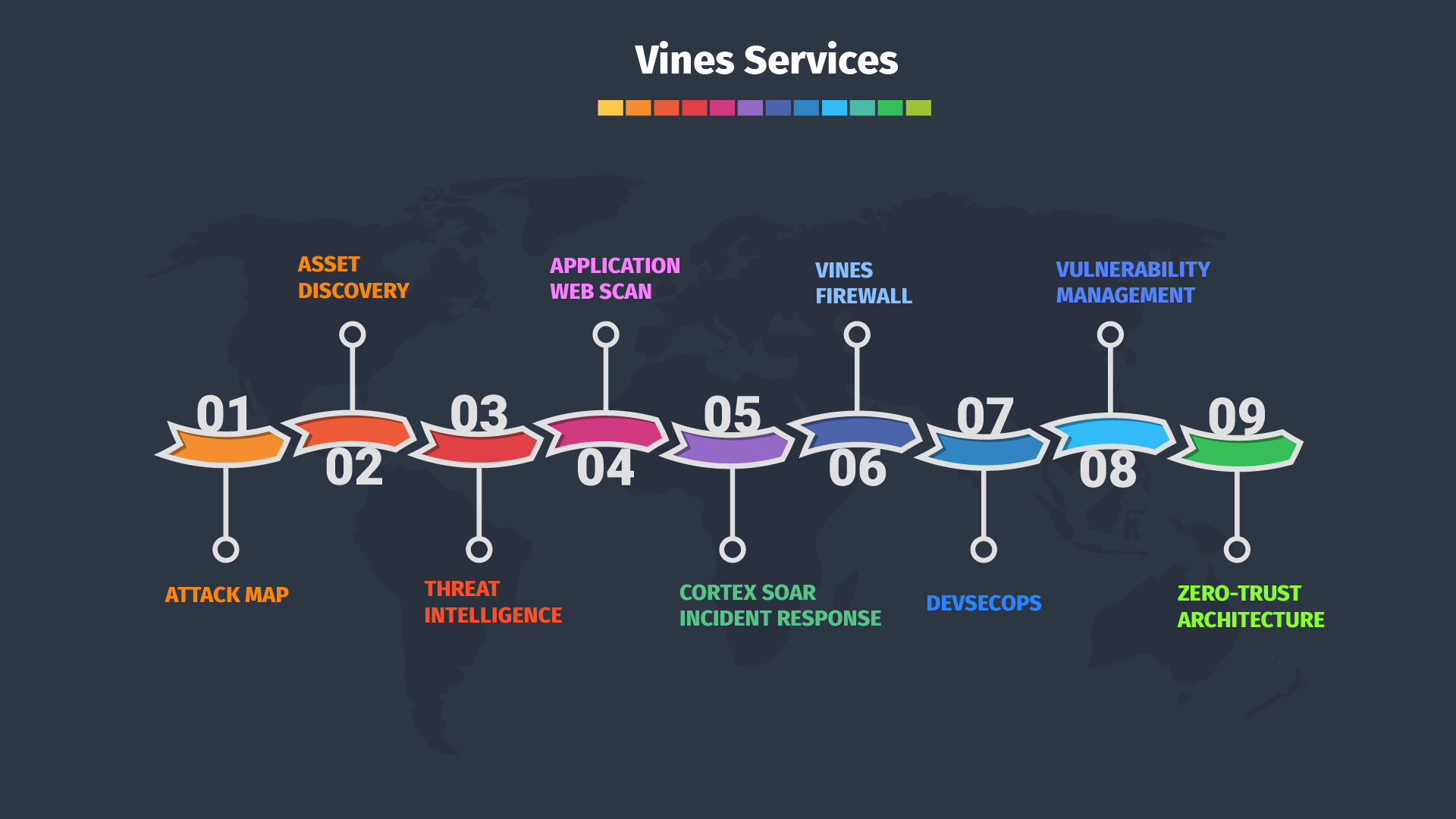
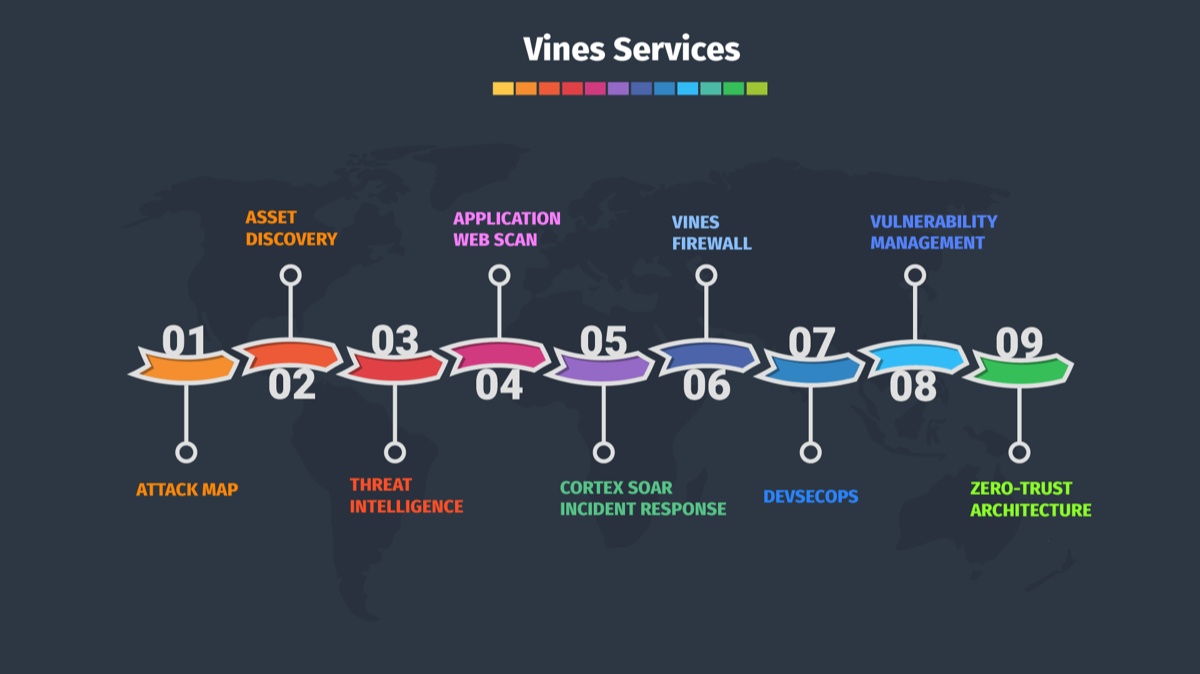
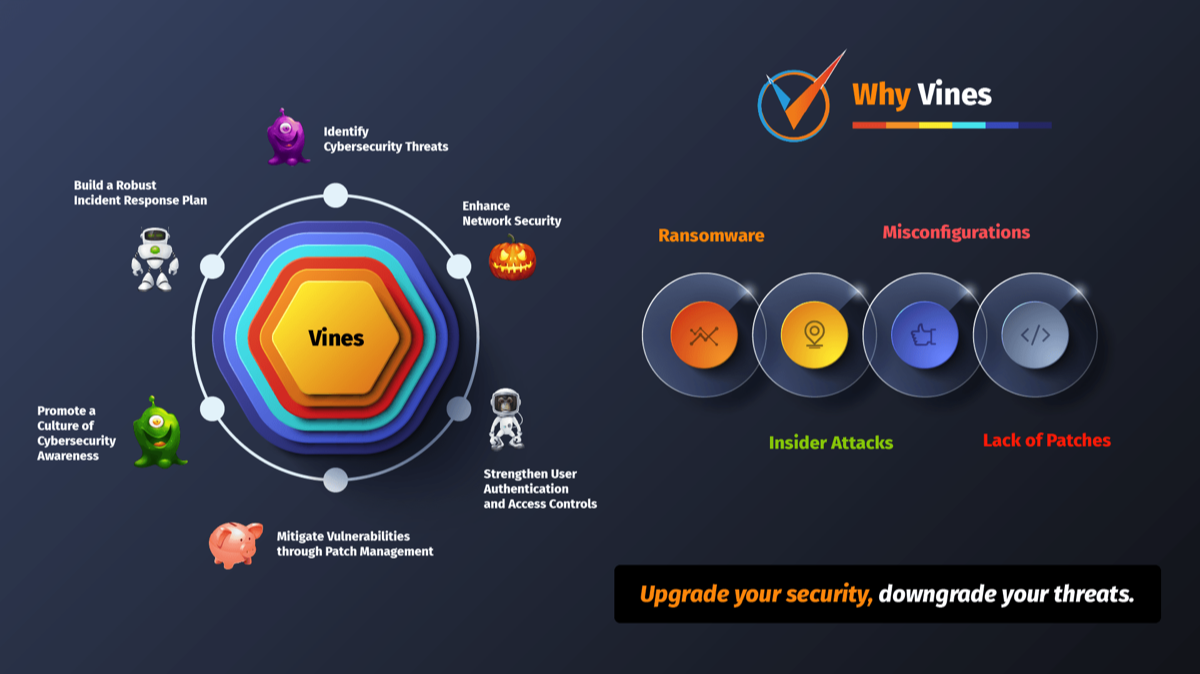
Vines The Comprehensive Solution for SOC Operations


SOC Vulnerability Vines
Vulnerability Vines serves as an indispensable resource for organizations aiming to strengthen their cybersecurity measures and safeguard their networks and systems against potential threats.
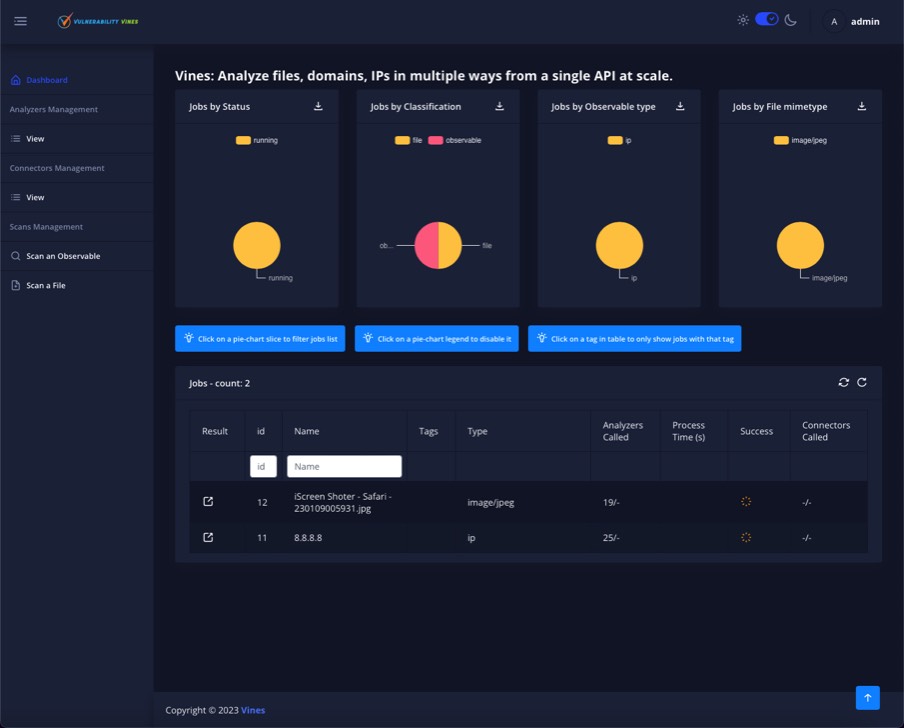
Vulnerability Vines



Vines
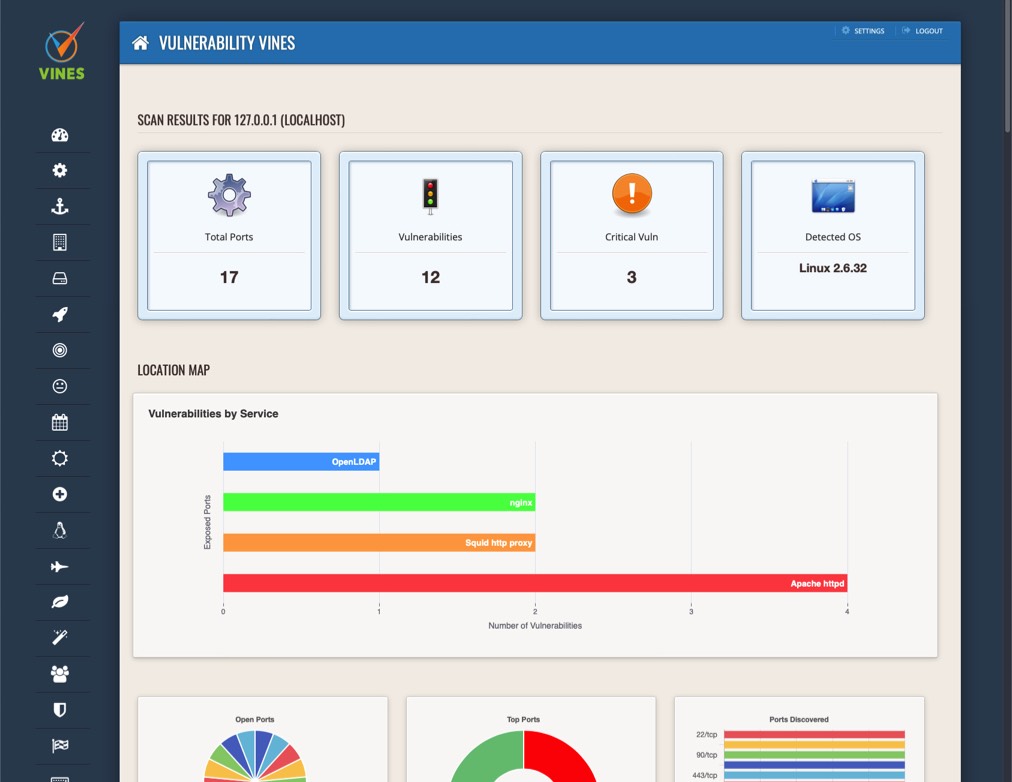
The Most Comprehensive Solution


Endpoint Security & XDR
With its extended detection and response (XDR) capabilities, Vines's Endpoint Security can identify, analyze, and remediate threats across various security layers, ensuring a proactive and robust defense against sophisticated attacks. Stay ahead of cybercriminals and safeguard your organization with Vines's Endpoint Security & XDR.
Vines


Vines

Intuitive Threat Intelligence
Empower your security teams with the knowledge they need to make informed decisions and protect your digital ecosystem with Vulnerability Vines' Intuitive Threat Intelligence.
Defend Your Digital Identity with Vines IAM
As the digital landscape evolves and cybercriminals become more sophisticated, the need for robust identity protection has never been greater. Vulnerability Vines understands this need and delivers a multi-layered defense system, guarding your sensitive data from potential harm. Our Identity Protection feature not only keeps your personal information secure but also alerts you to any suspicious activity, enabling you to take control and mitigate risks promptly.
Experience peace of mind knowing that your online presence is shielded from cyber-attacks and that your personal data remains confidential. With Vulnerability Vines' Identity Protection, you can navigate the digital world confidently, knowing that your identity is in safe hands. Don't compromise on security – choose the reliable and advanced protection you deserve.
Vines

Vines
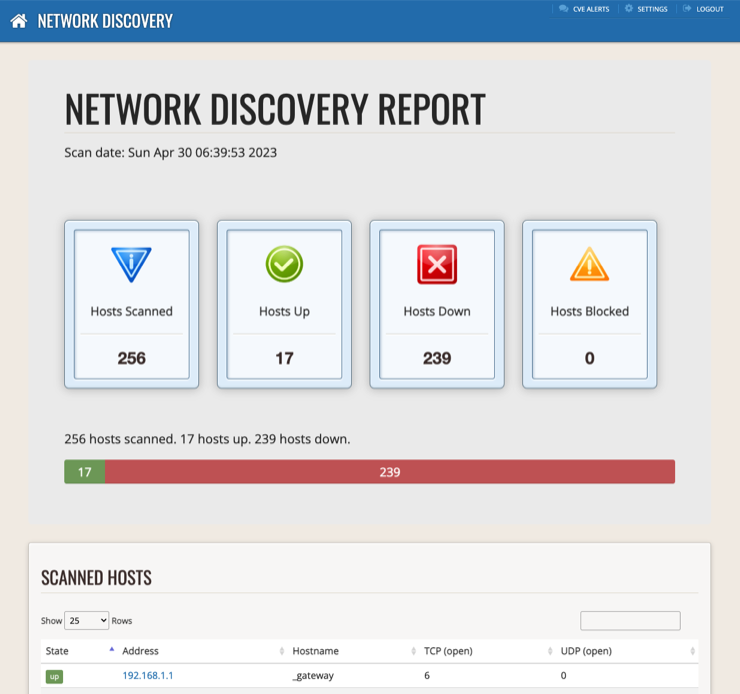
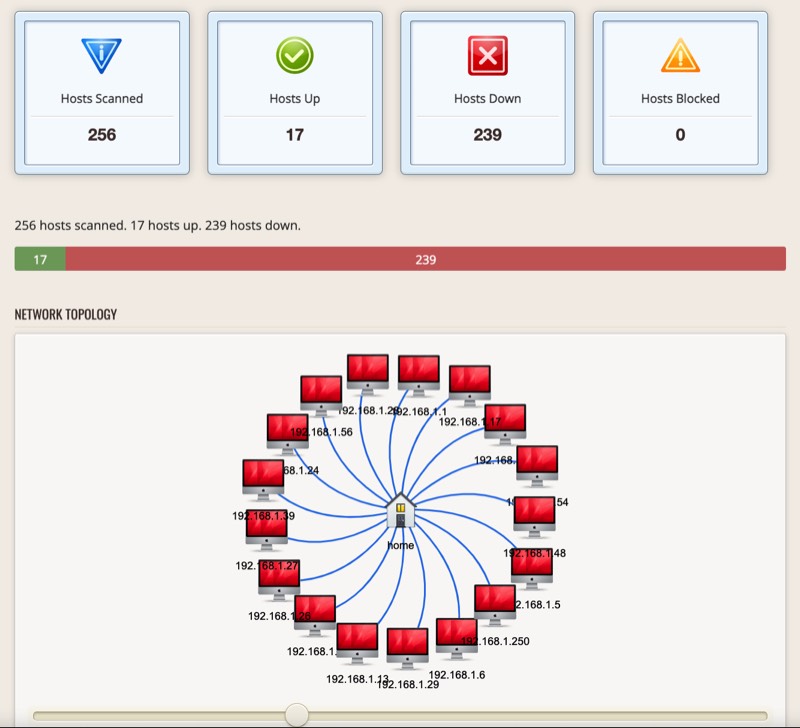
Asset Discovery
Stay ahead of emerging threats and maintain a robust security posture with Vulnerability Vines' Asset Discovery. Experience unparalleled insights, seamless integration, and a user-friendly interface that elevates your organization's security to new heights. Discover your digital assets and safeguard your digital landscape with Vulnerability Vines today!


Swift and Seamless Incident Response
Our user-friendly interface makes it easy to track and manage incidents, ensuring a quick and efficient resolution. Stay ahead of cyber threats and maintain the highest level of security for your business with Vulnerability Vines' unparalleled Incident Response capabilities.
Vines


Vines

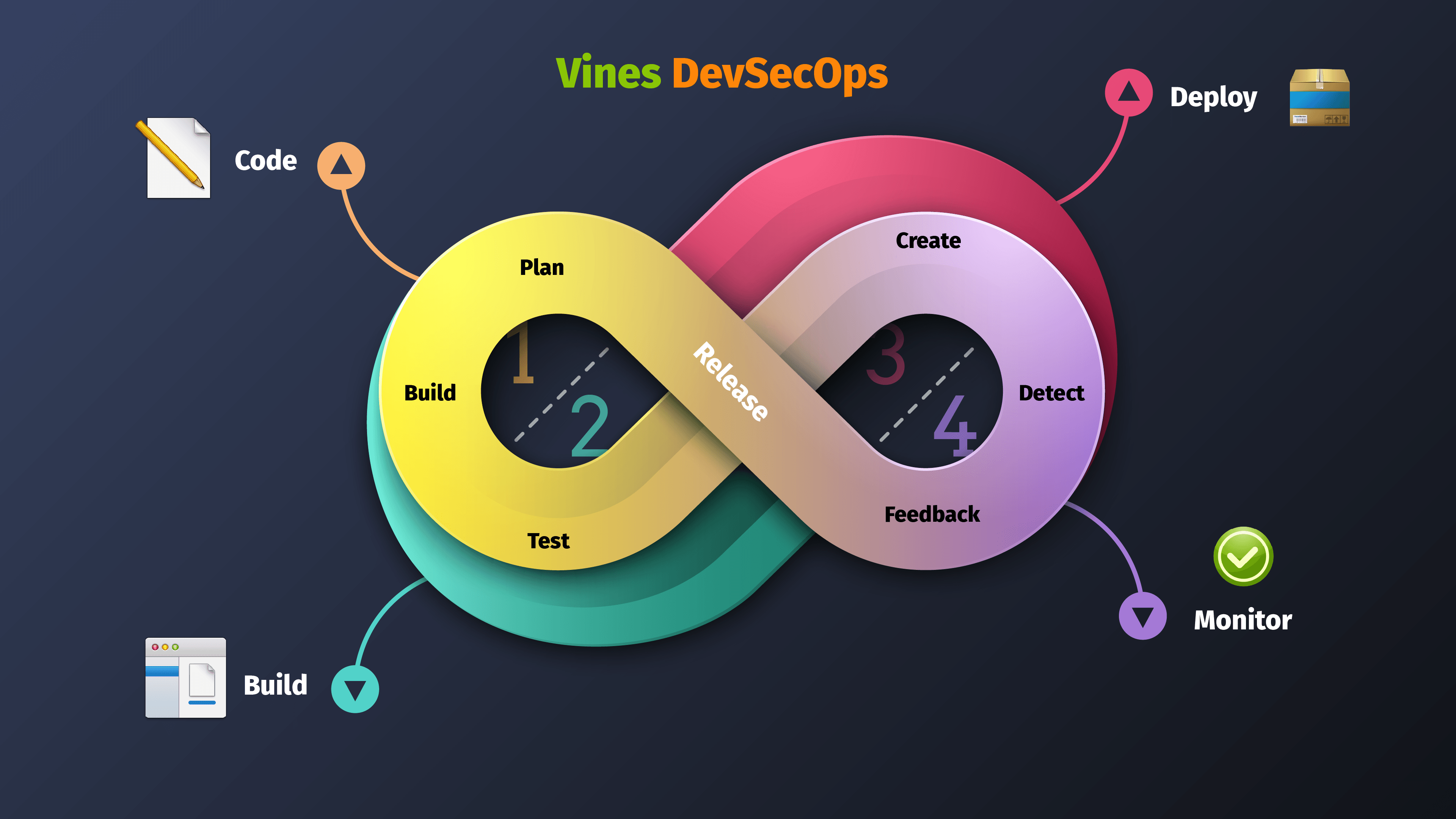
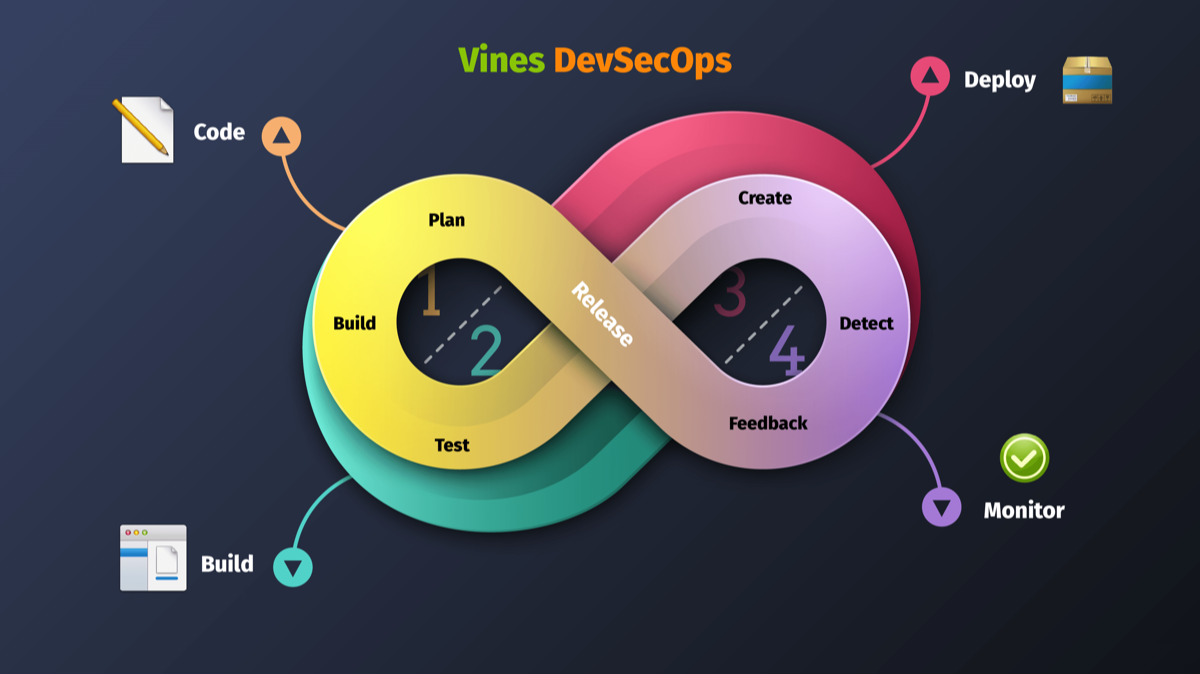
Robust DevSecOps Integration
Stay ahead of threats and ensure the highest level of protection for your applications, infrastructure, and data with our cutting-edge DevSecOps feature. Experience unparalleled security, compliance, and efficiency with Vulnerability Vines – your ultimate DevSecOps partner.


Comprehensive Cloud Security Assessment
This essential component of Vulnerability Vines product is designed to identify and mitigate potential security risks in your cloud environment, ensuring the safety and integrity of your data and applications.
Gain critical insights into misconfigurations, access control issues, and other vulnerabilities that may expose your organization to cyber threats. With our Cloud Security Assessment, empower your business with the confidence to operate securely and efficiently in the cloud.
Vines


Vines

Robust Compliance Management
That's why Vulnerability Vines is designed to help you effortlessly manage and maintain compliance with the leading regulatory frameworks: PCI, NIST-53, GDPR, and HIPAA.
With Vulnerability Vines' robust compliance management feature, your organization can easily assess and align its security posture with industry-specific regulations, reducing the risk of non-compliance penalties and reputational damage. Our automated solution saves time and resources by simplifying the process of tracking and updating your compliance status across multiple frameworks.
Our platform empowers your team with actionable insights and recommendations, enabling them to prioritize and address vulnerabilities more efficiently. You can gain peace of mind knowing that your sensitive data is protected and that your organization's security practices are up to date with the latest regulatory requirements.
Stay ahead of the compliance curve with Vulnerability Vines, and safeguard your organization's reputation, customer trust, and financial stability.


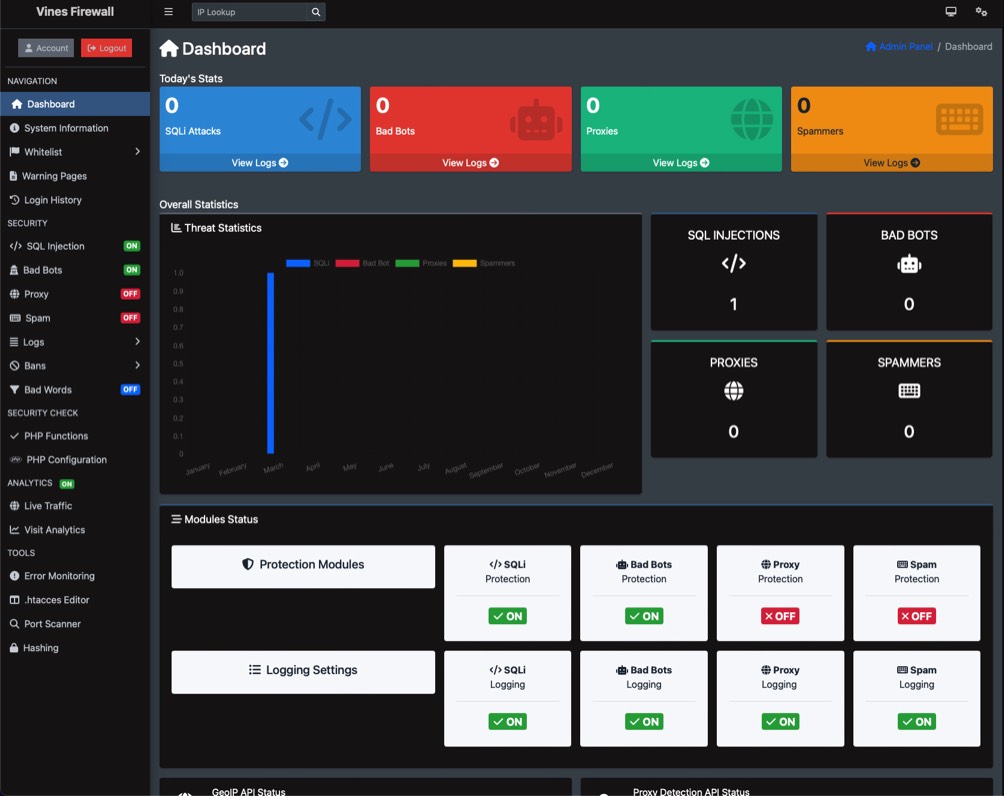
Web Application Firewall for Unmatched Security
By continuously monitoring and analyzing web traffic, our WAF intelligently detects and blocks any suspicious activities, ensuring that your website remains secure and your data stays protected.
With an easy-to-use interface, customizable security policies, and real-time alerts, you can gain complete control over your web application's security and stay one step ahead of evolving threats.
Choose Vulnerability Vines' Web Application Firewall and experience unparalleled protection, enhanced performance, and peace of mind for your online business.
Vines


Vines
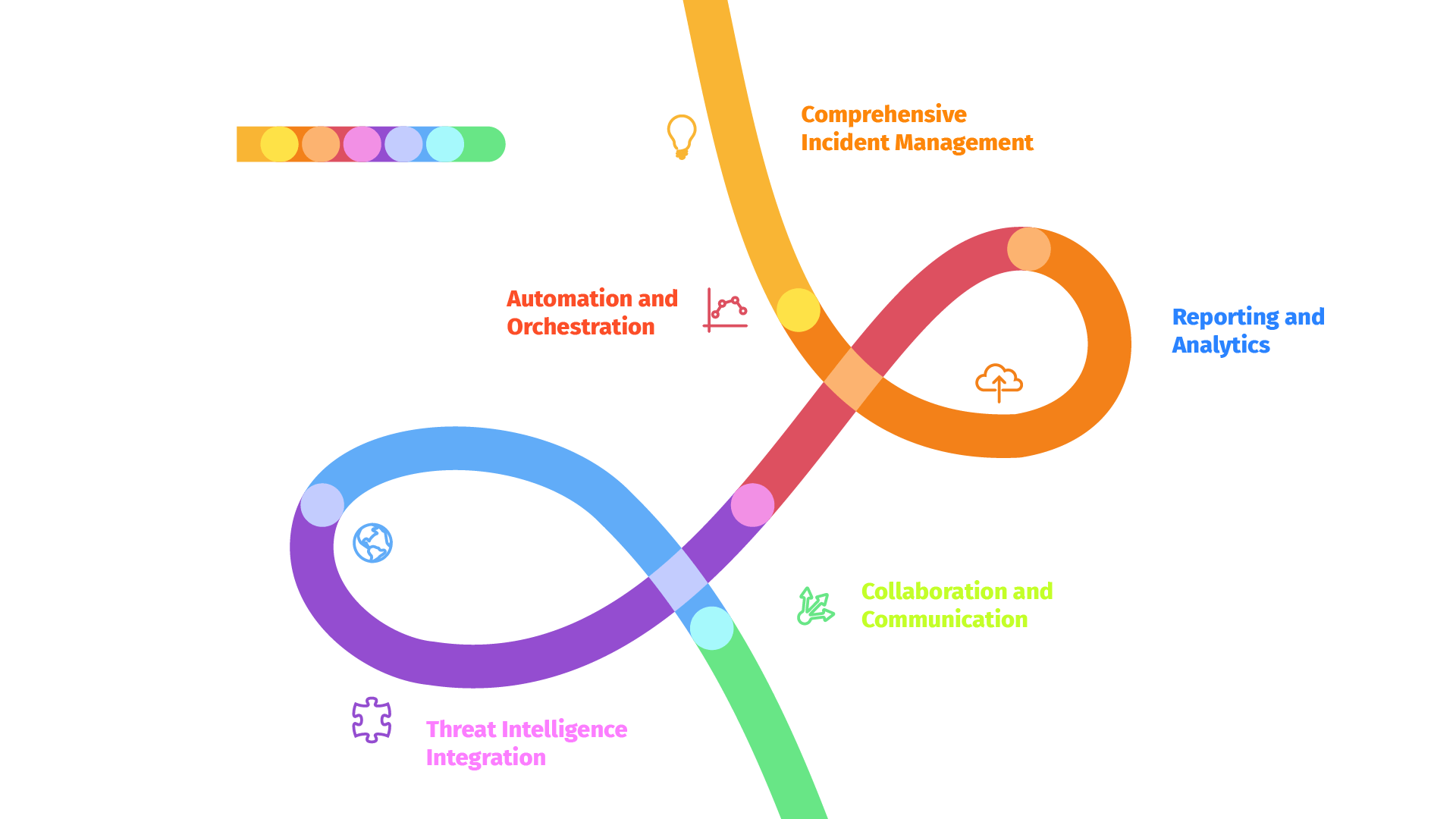
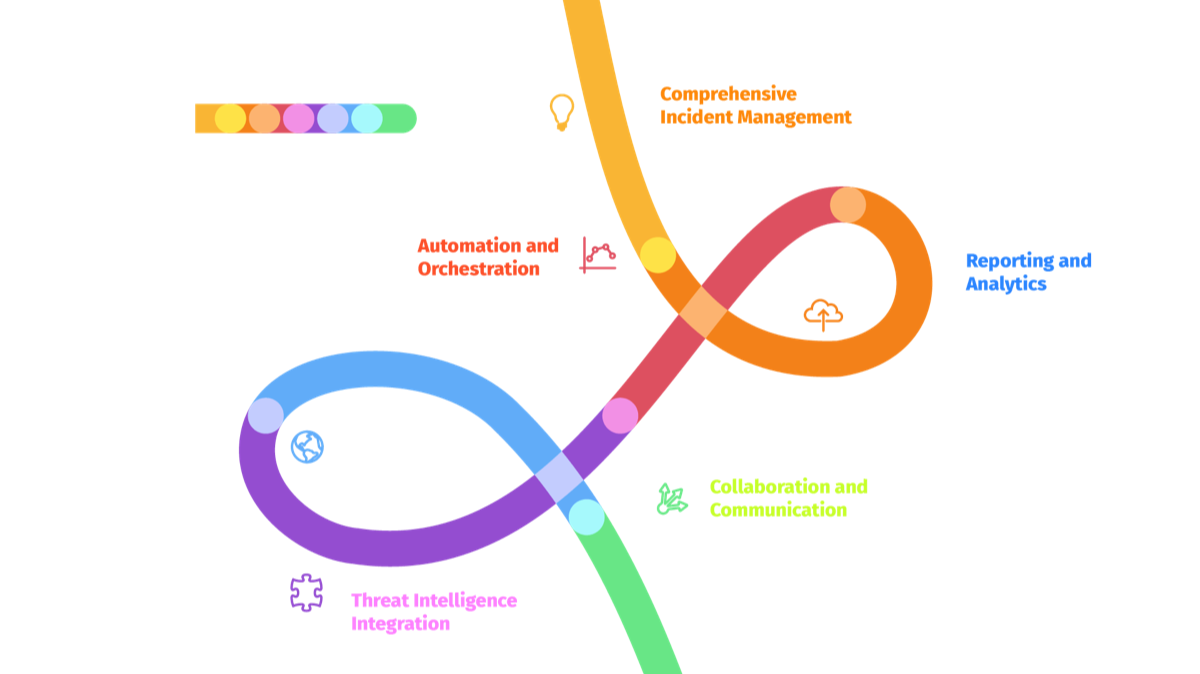
SOAR: Secure, Optimize, Analyze & Respond
With SOAR, you can streamline threat identification, accelerate incident response, and safeguard your digital assets against ever-evolving cyber threats.
Unleash the full potential of your security team and stay a step ahead of attackers with vulnerability vines and SOAR - your ultimate defense against cyber threats.


Patch Management for Optimal Security
With our streamlined Patch Management system, you can confidently maintain the integrity of your network while minimizing risks and maximizing productivity.
Experience a seamless and secure environment with the cutting-edge solution that vulnerability vines has to offer.
Vines



Vines
Comprehensive Vulnerability Management
By prioritizing risk levels and streamlining remediation processes, our Vulnerability Management feature empowers your organization to maintain a strong security posture, safeguarding your critical assets and data from cyber threats.
Stay ahead of the curve and protect your organization with our proactive and intelligent Vulnerability Management solution.
Cyber Wargames
Red Team / Blue Team Exercises
The Red Team, our skilled and certified ethical hackers, will emulate the tactics, techniques, and procedures of real-world adversaries, attempting to infiltrate your organization's network, applications, and systems.
Simultaneously, the Blue Team, comprising your in-house security personnel, will work tirelessly to detect, respond, and mitigate these simulated attacks, honing their skills and testing the robustness of your security measures.
Vines


Vines
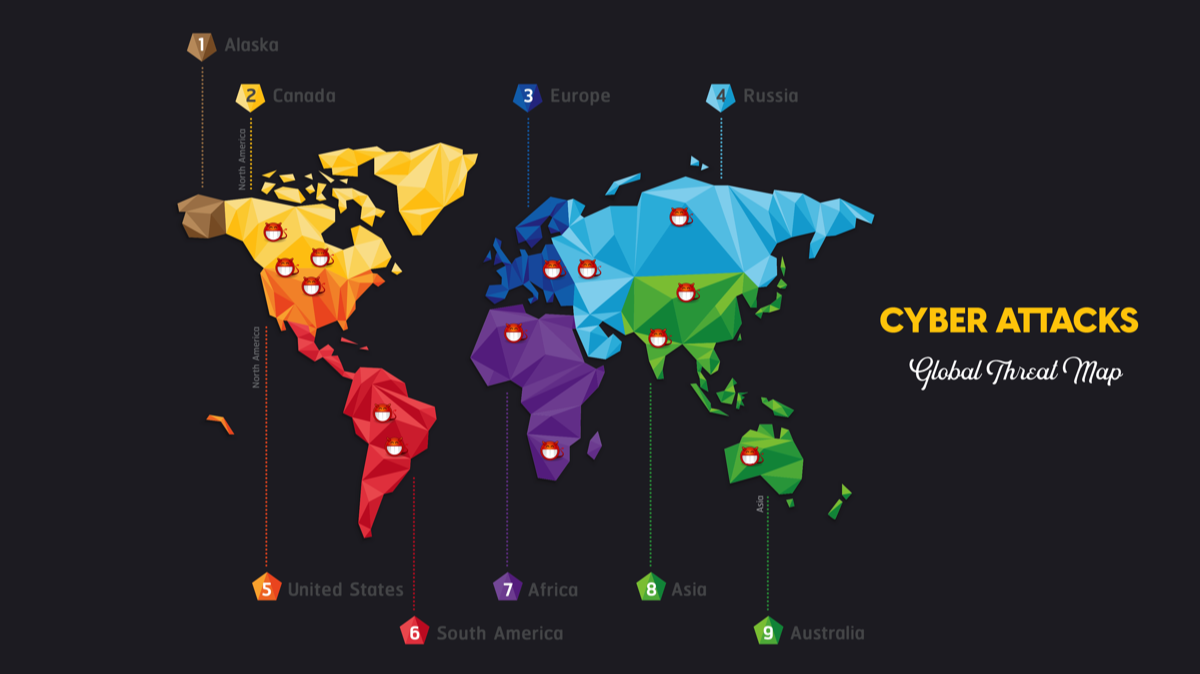
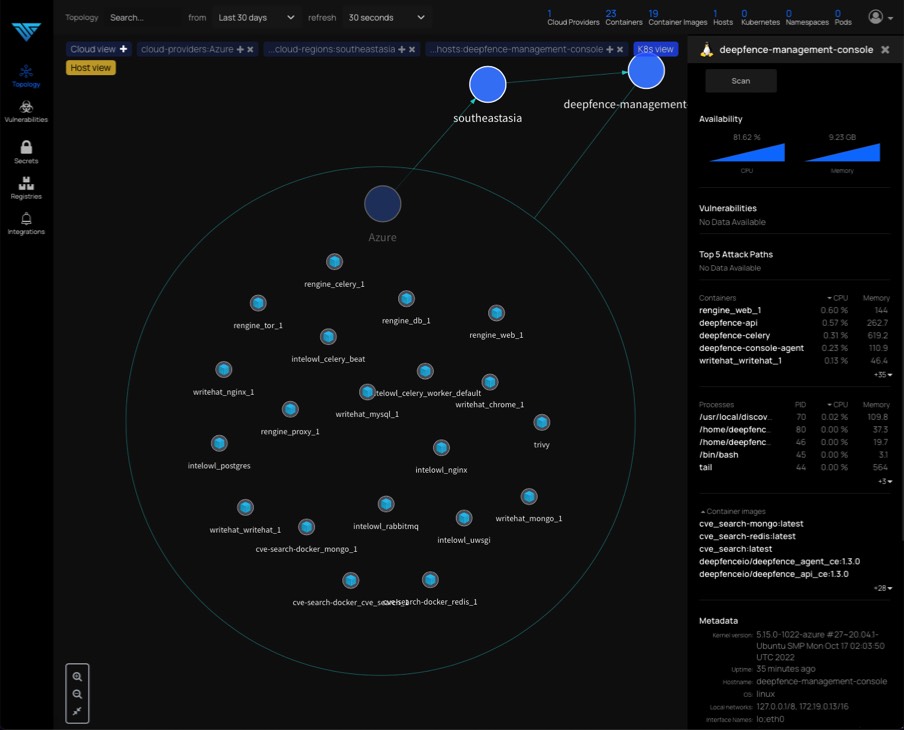
Container Security for Uncompromised Protection
Our Container Security solution offers continuous monitoring and protection for both Docker and Kubernetes environments, giving you complete visibility and control over your container ecosystem.
Embrace the power of containerization with confidence, knowing that our state-of-the-art technology shields your applications from risks and empowers you to maintain a secure and compliant ecosystem.


Attack Surface Management
With our Vulnerability Vines product, you can now effectively manage and secure your entire attack surface with our comprehensive Attack Surface Management feature.
With a holistic view of your network, our Attack Surface Management empowers you to proactively assess, prioritize, and remediate security risks, ensuring a robust defense against cyberattacks.
Don't leave your organization exposed – choose Vulnerability Vines for end-to-end security and peace of mind.
Vines
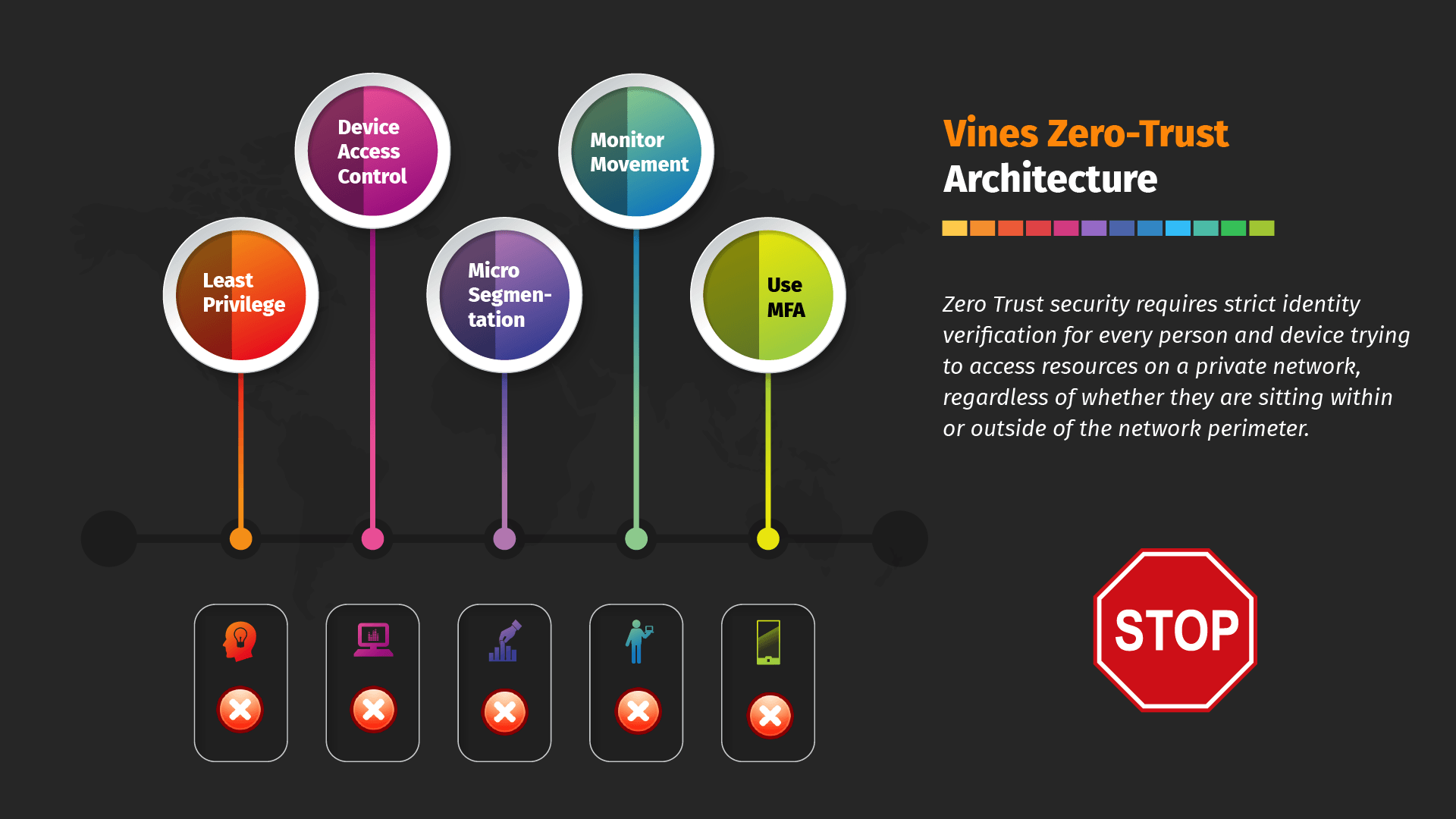
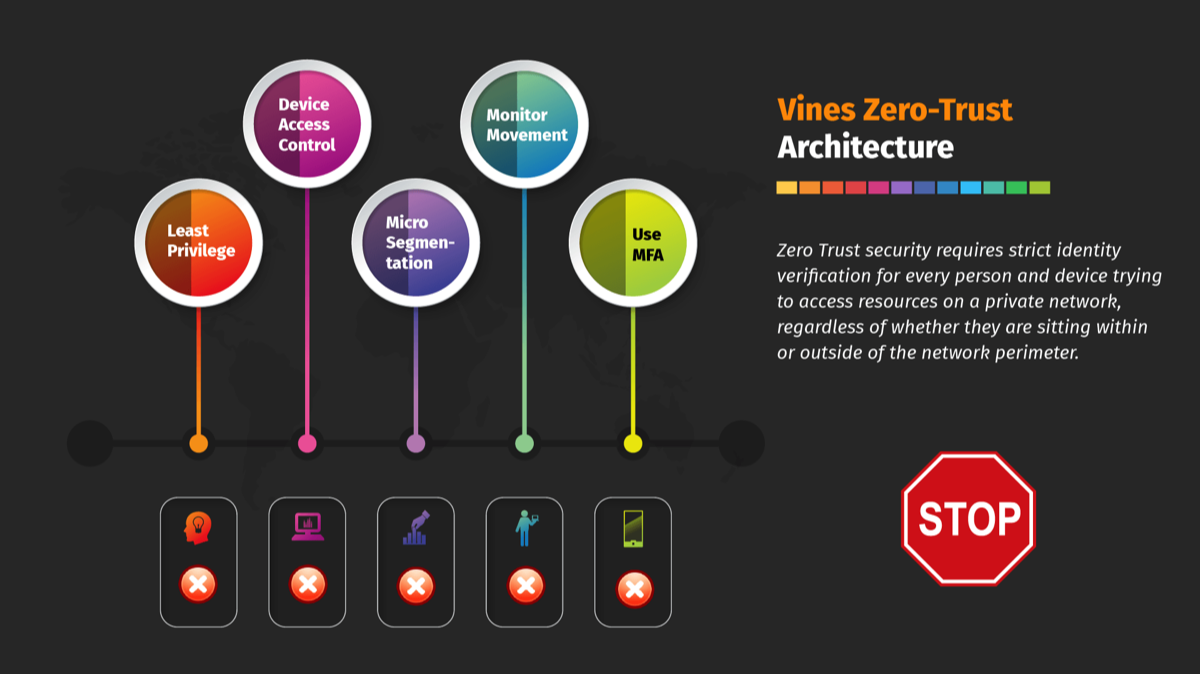
Zero-Trust Architecture
The zero-trust approach is a key feature of the product, ensuring that no entity, whether internal or external, is granted automatic access to the network or resources.
By implementing the zero-trust model, Vulnerability Vines ensures that potential attackers can't exploit any inherent trust within the system, making it much harder for them to access critical data and resources.
Vines


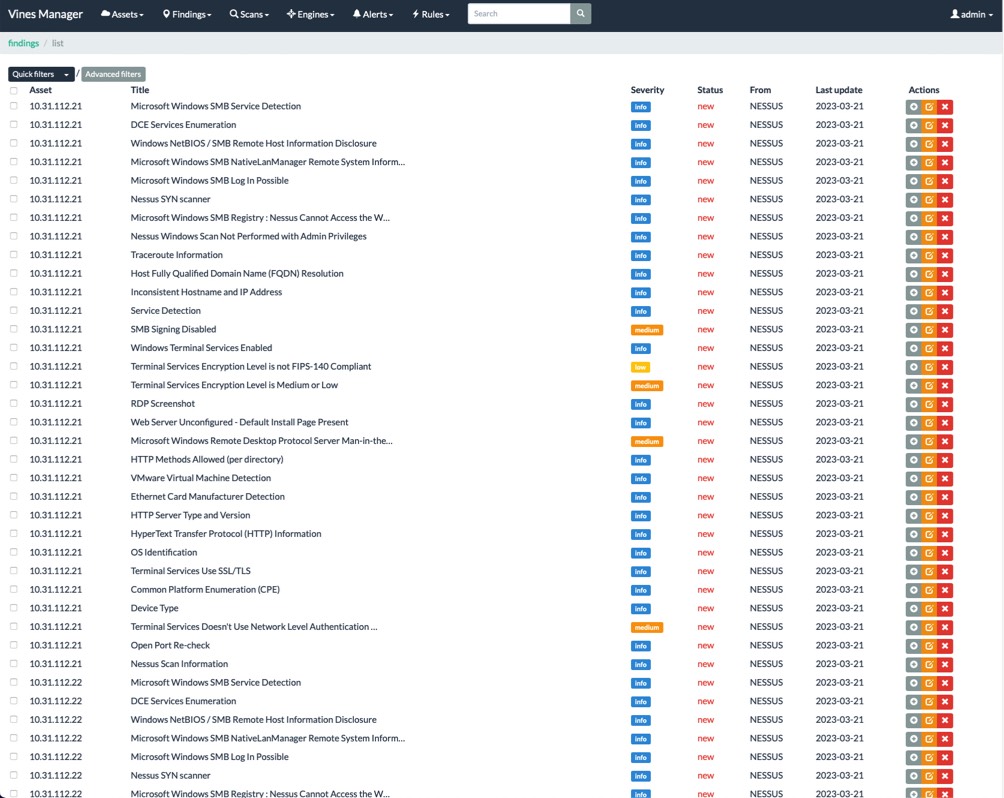
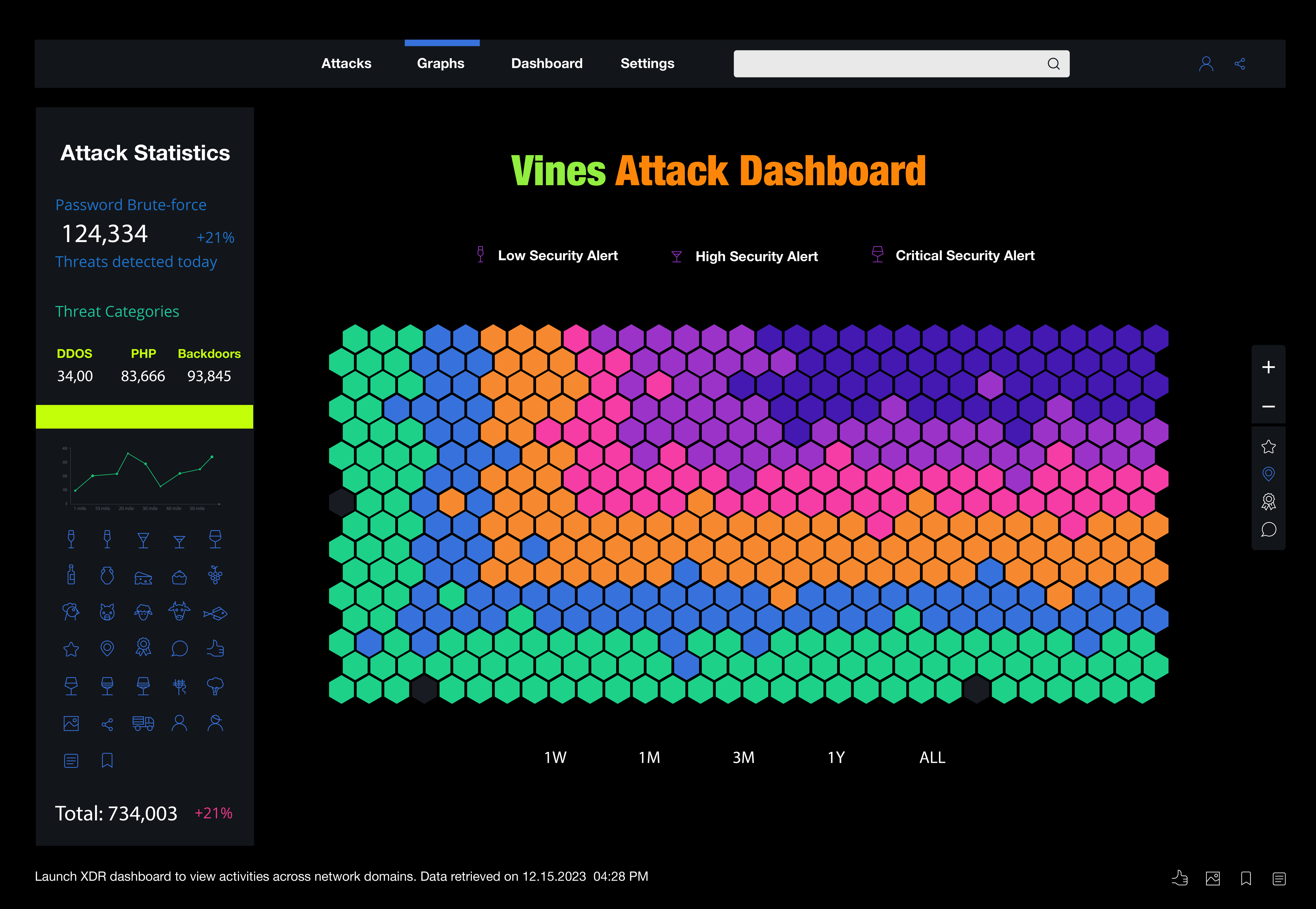
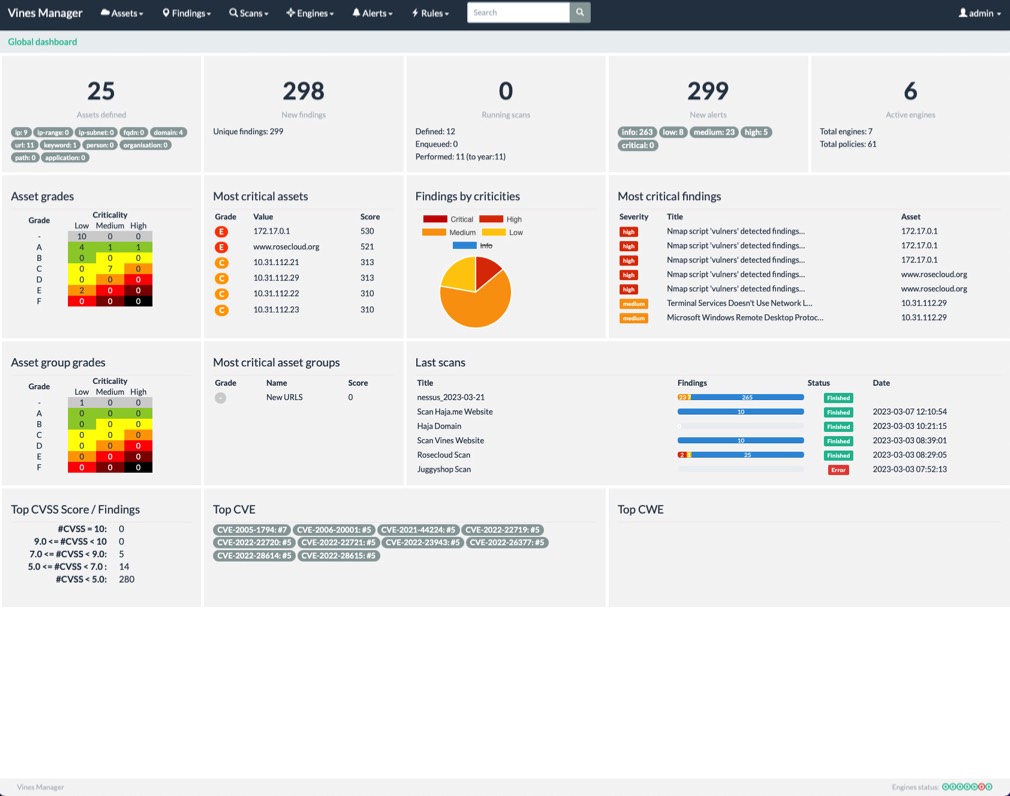
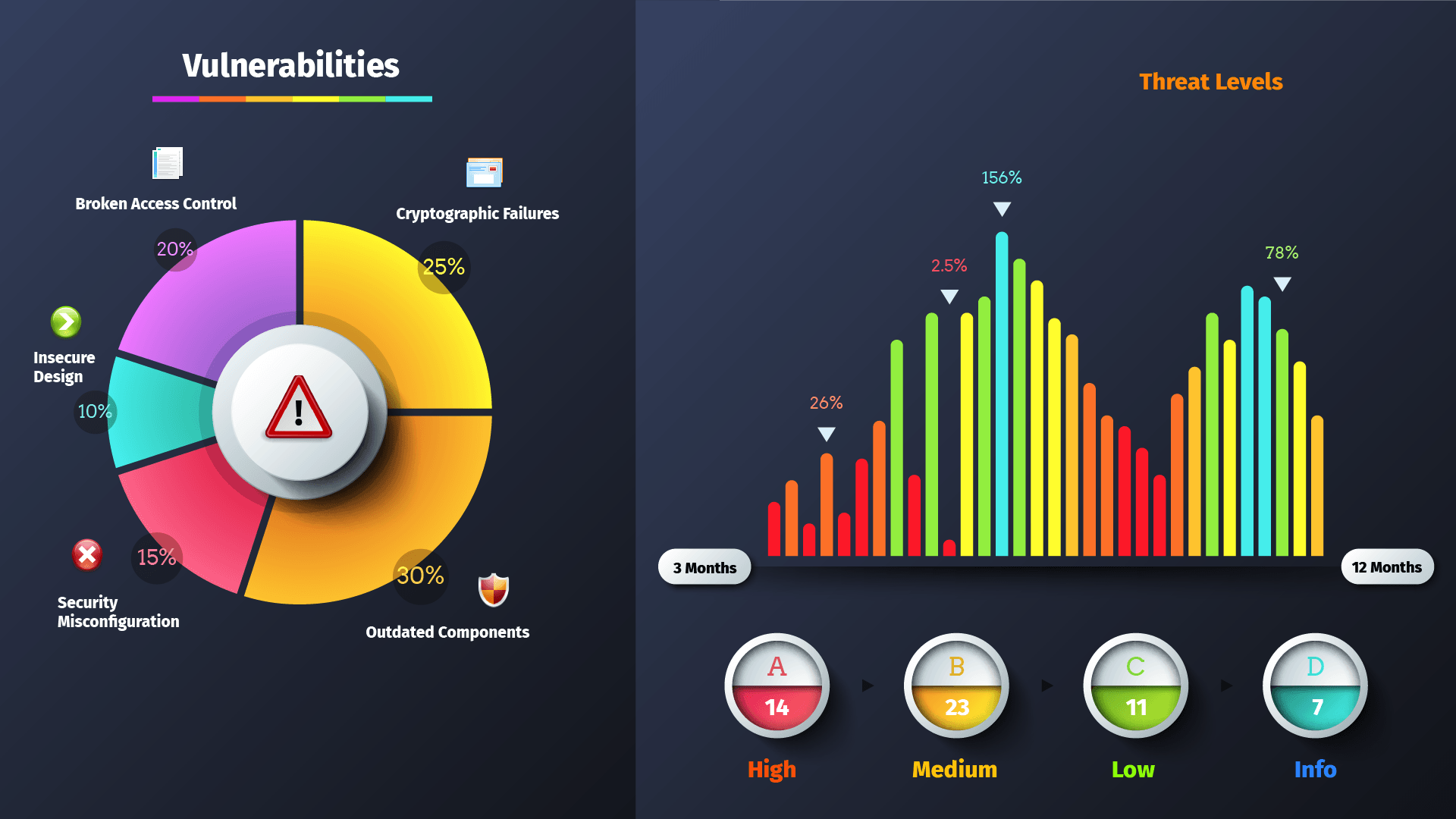
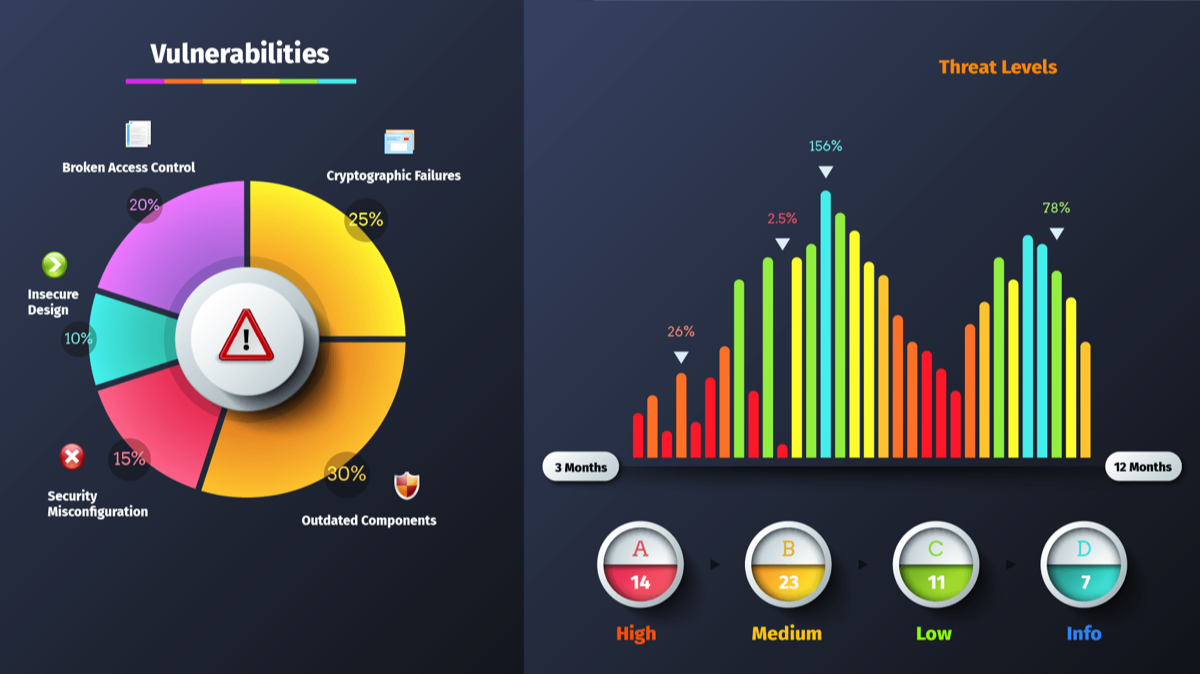
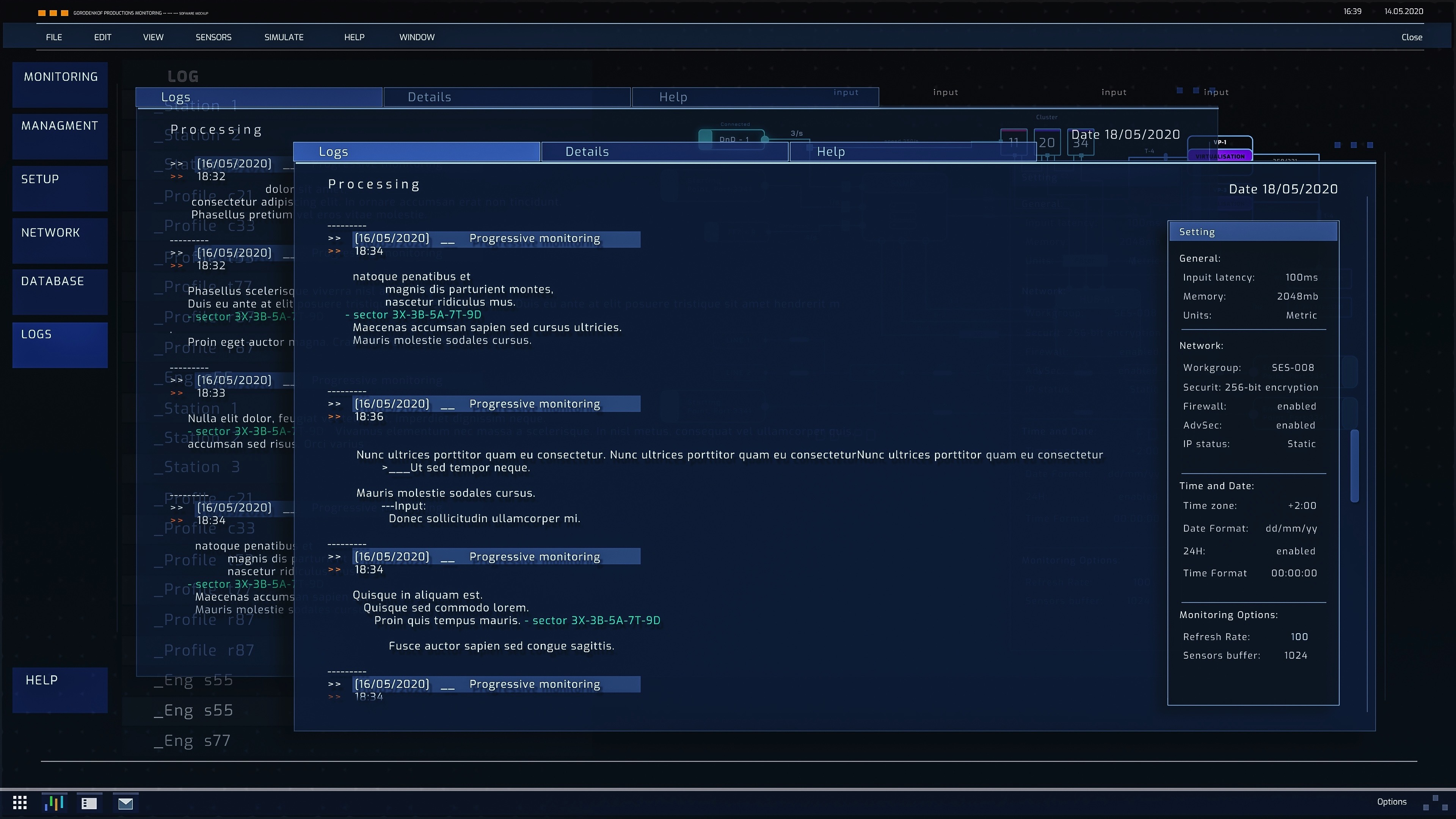
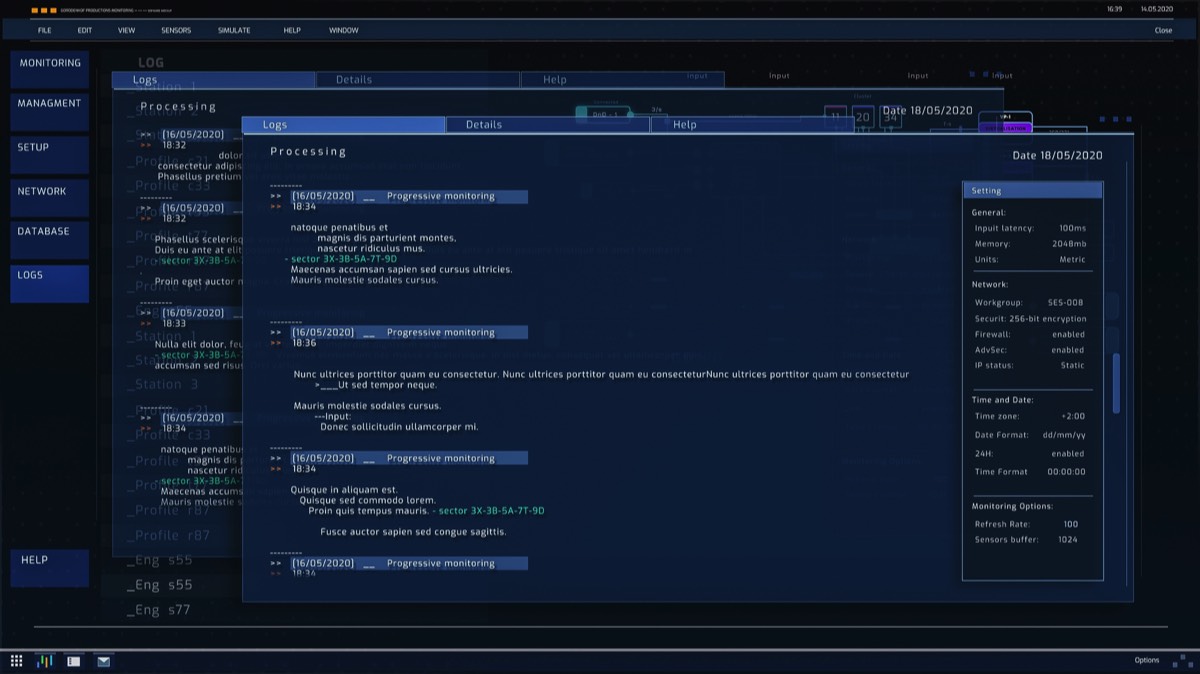
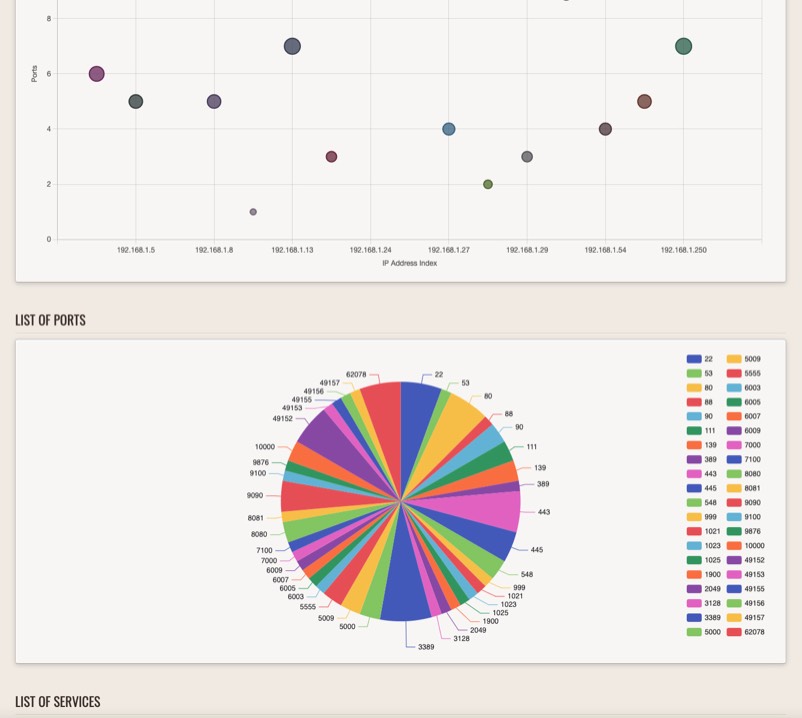
SOC Vulnerability Vines Screenshots
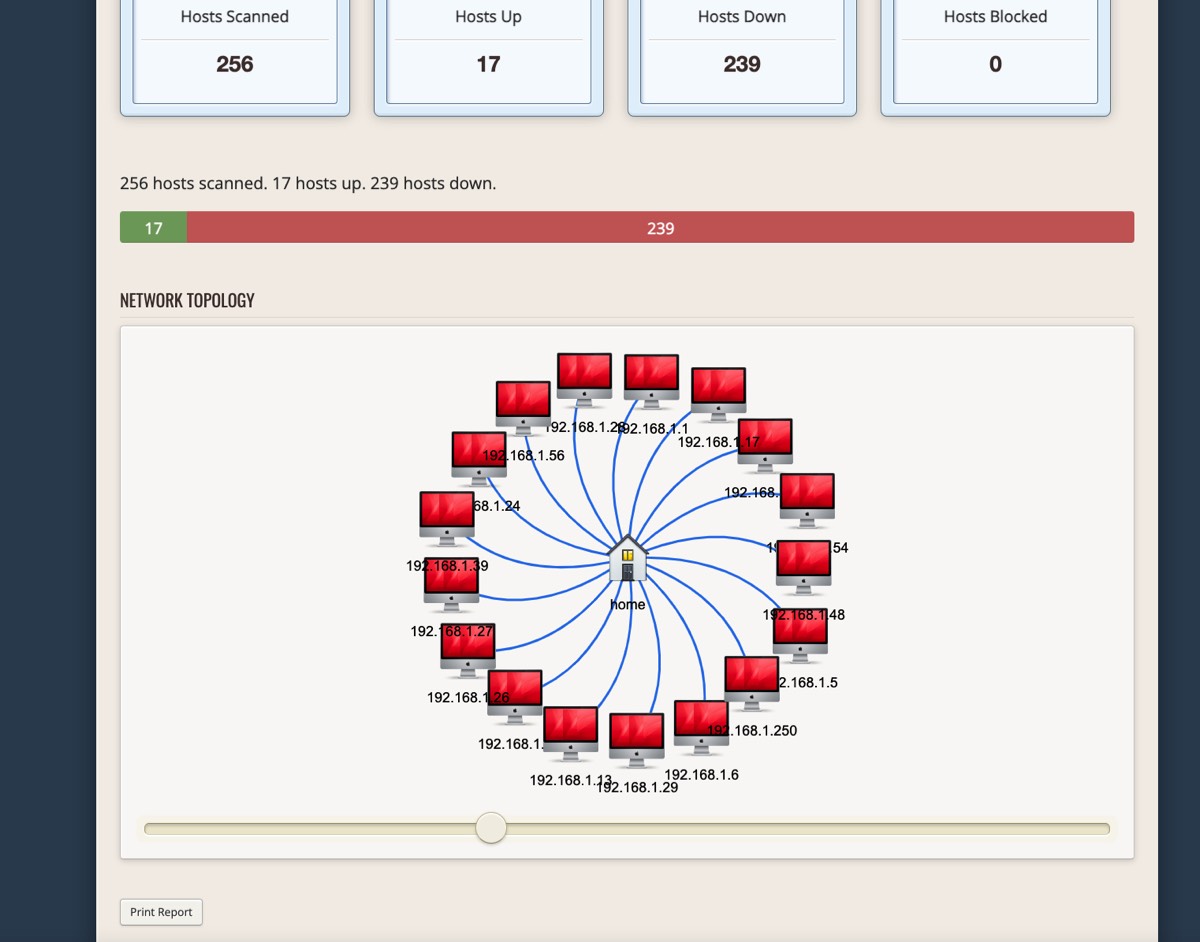
Image Title
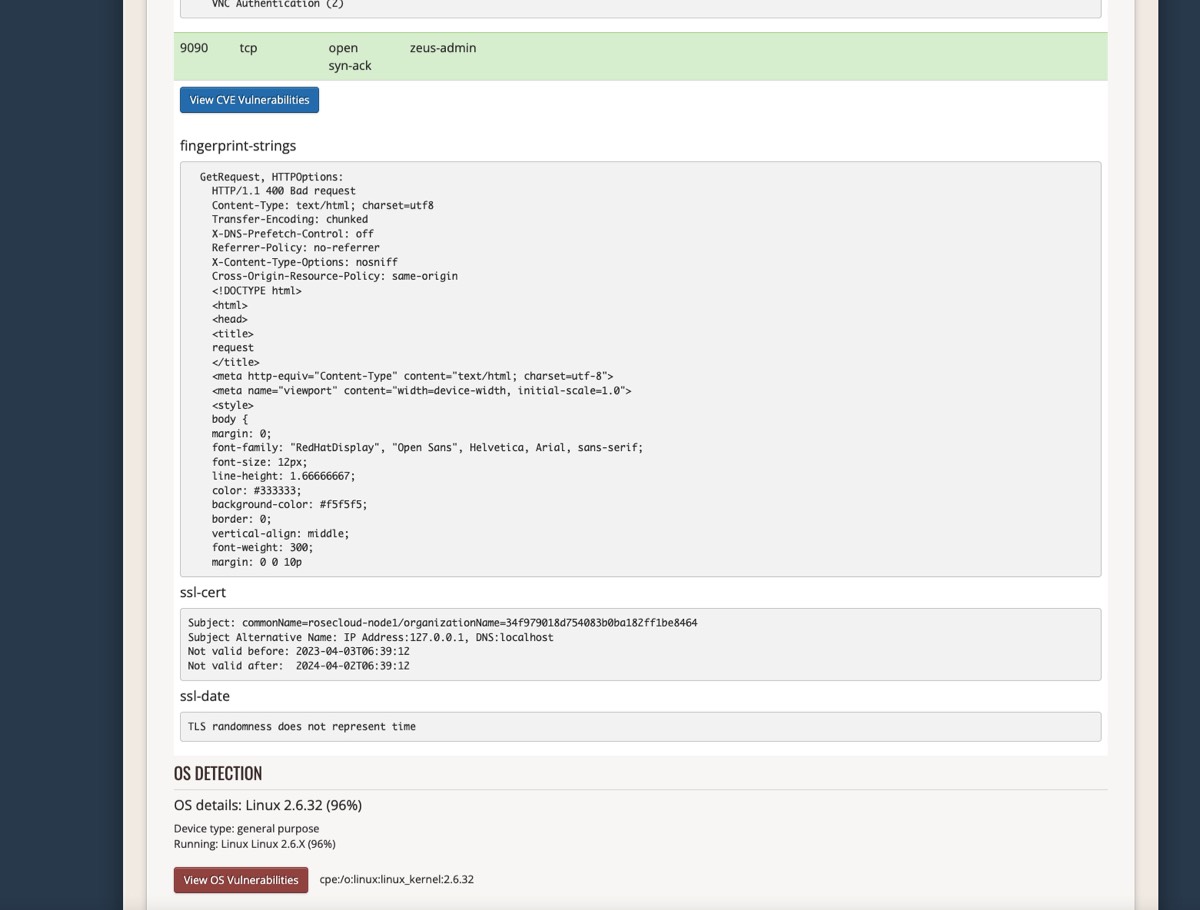
Image Title
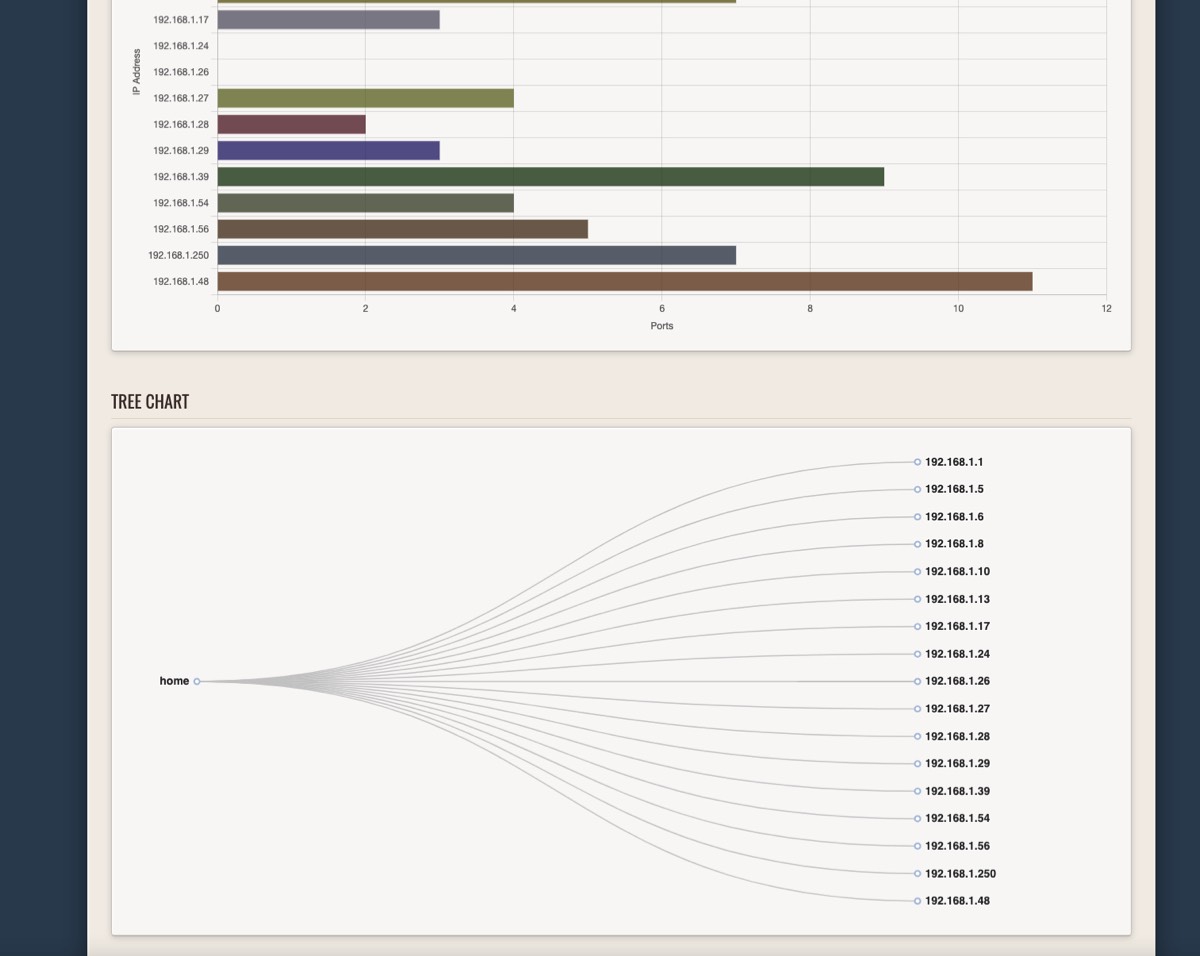
Image Title
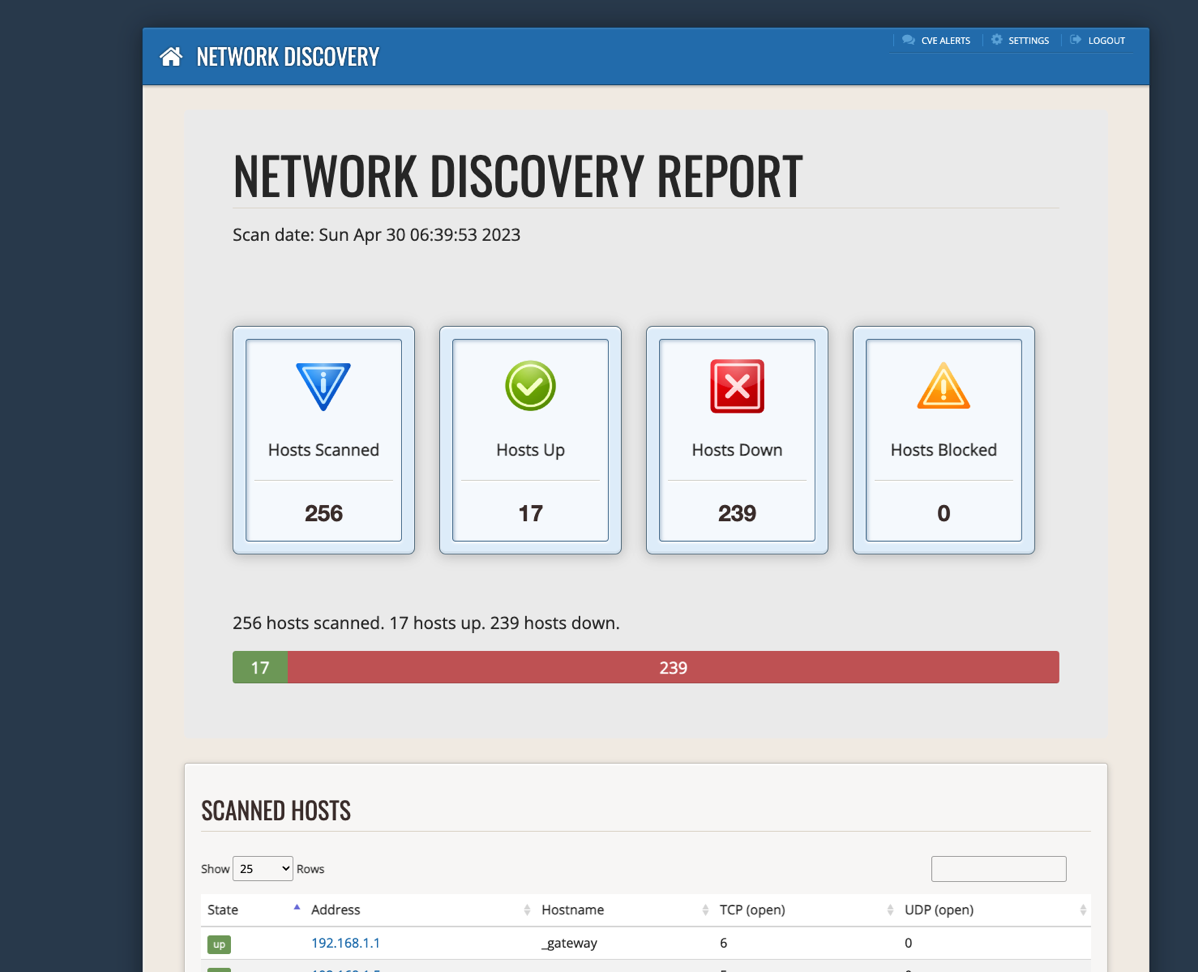
Image Title
Image Title
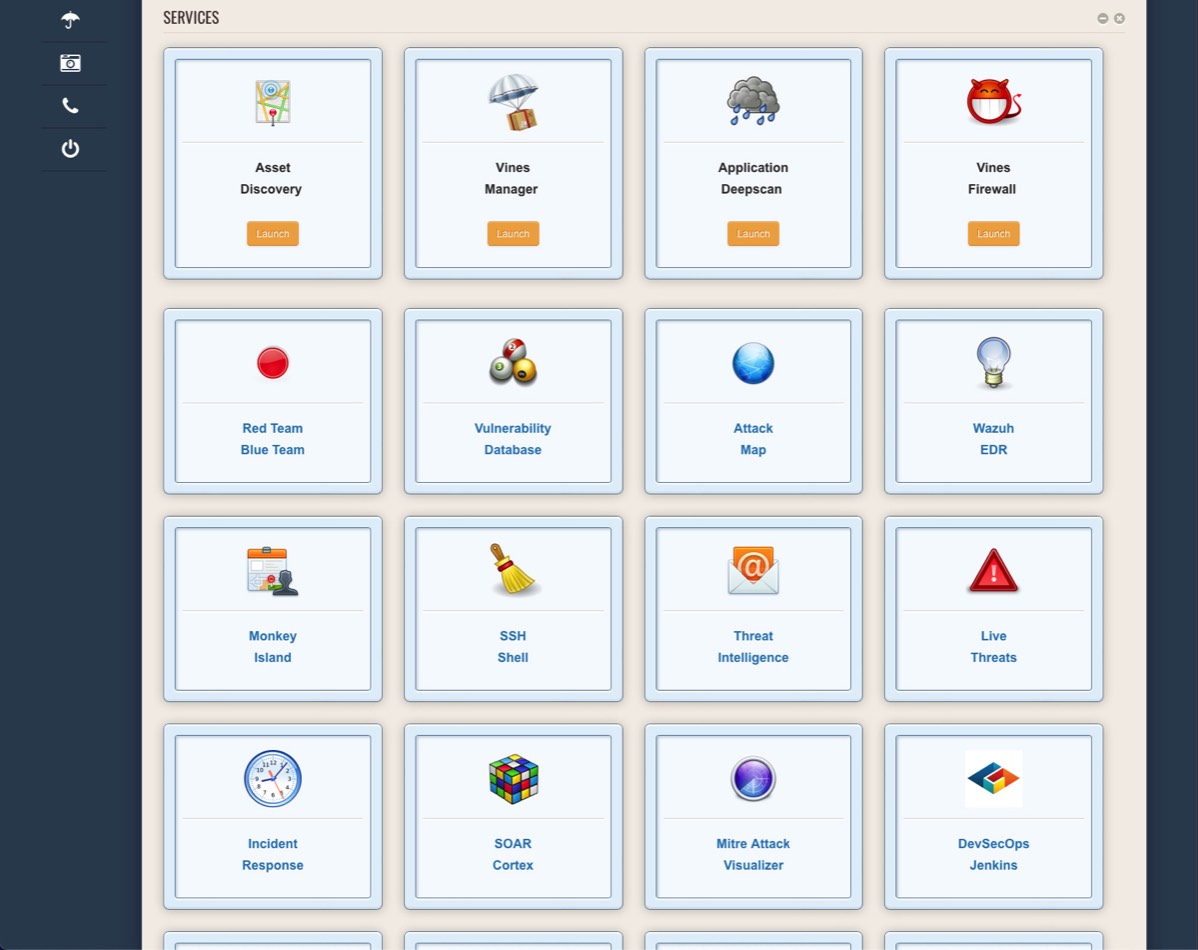
Image Title
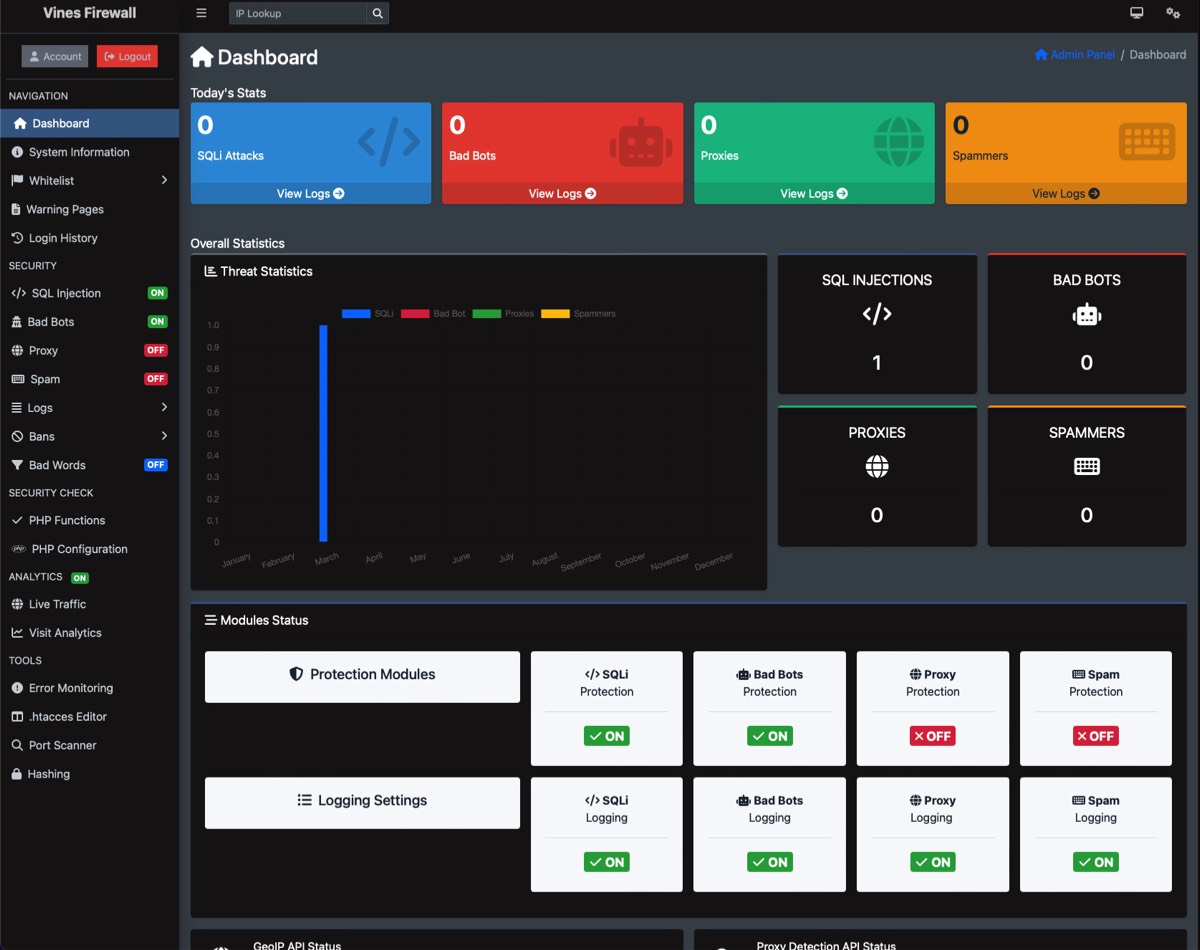
Image Title
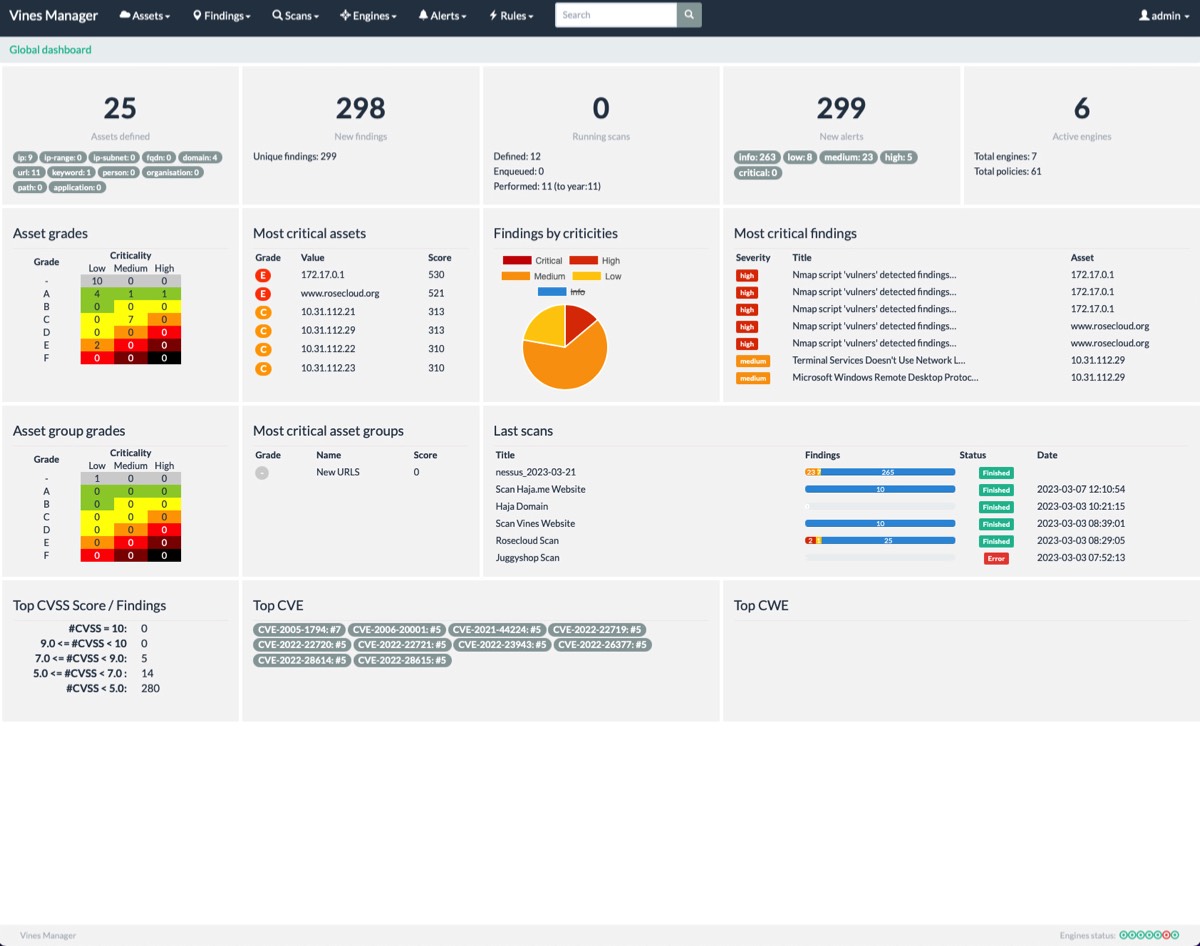
Image Title
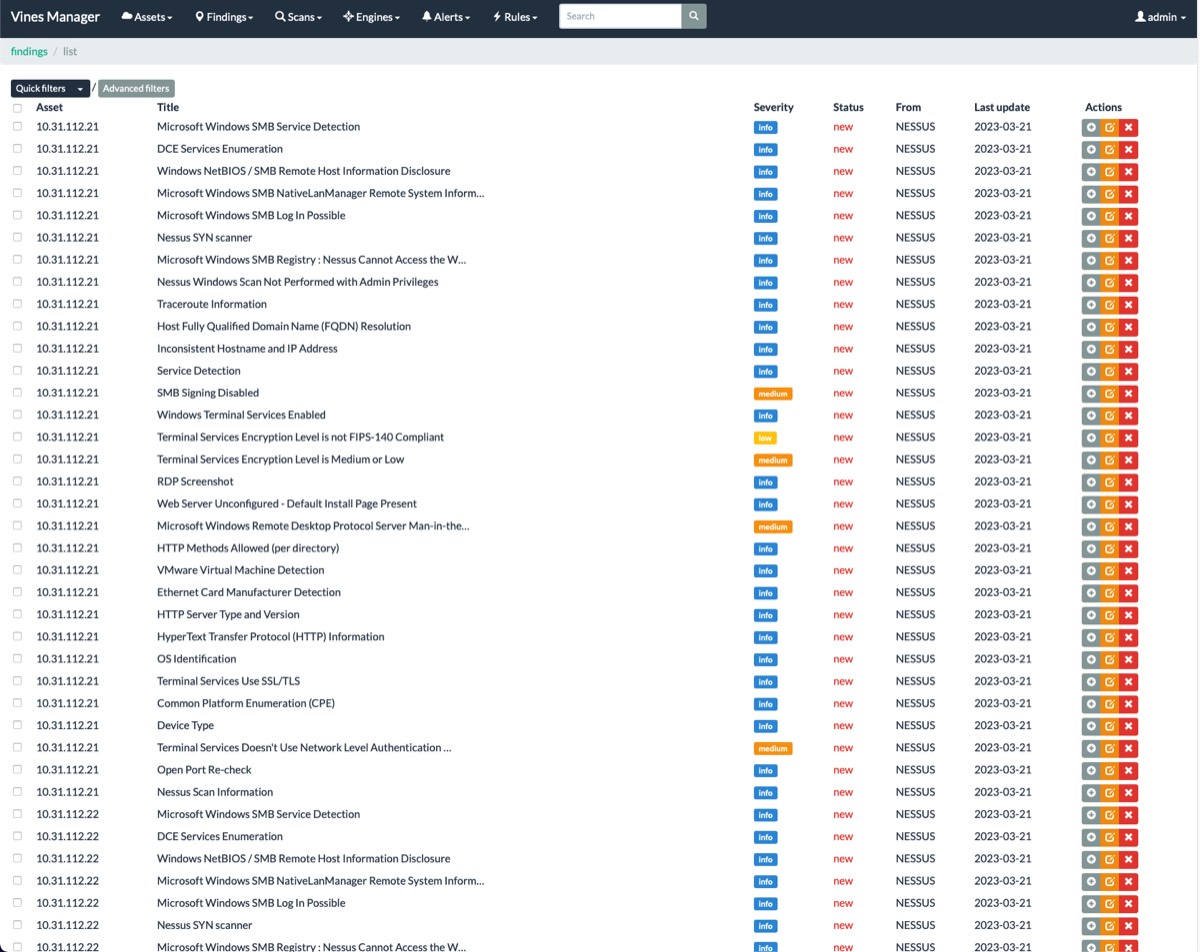
Image Title
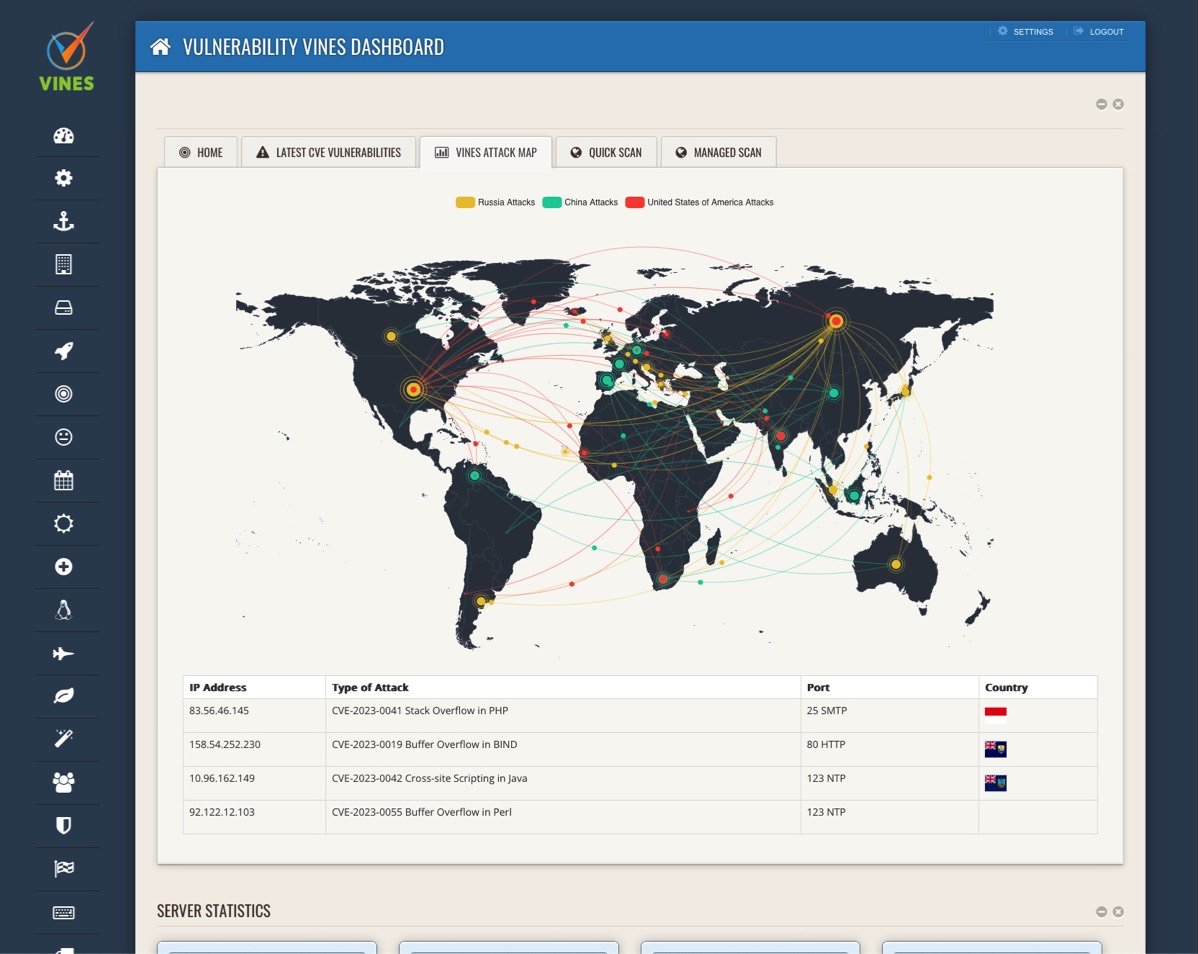
Image Title

Image Title
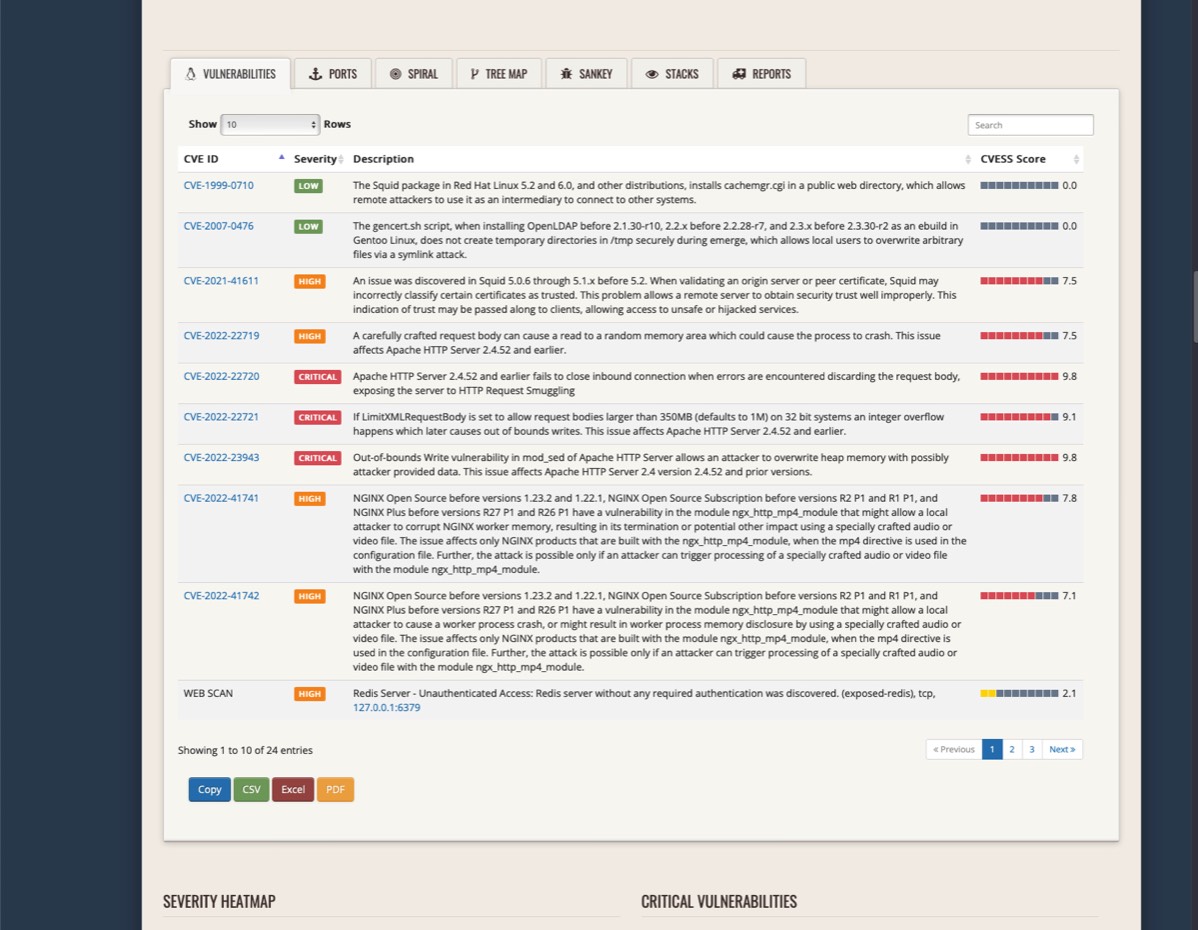
Image Title
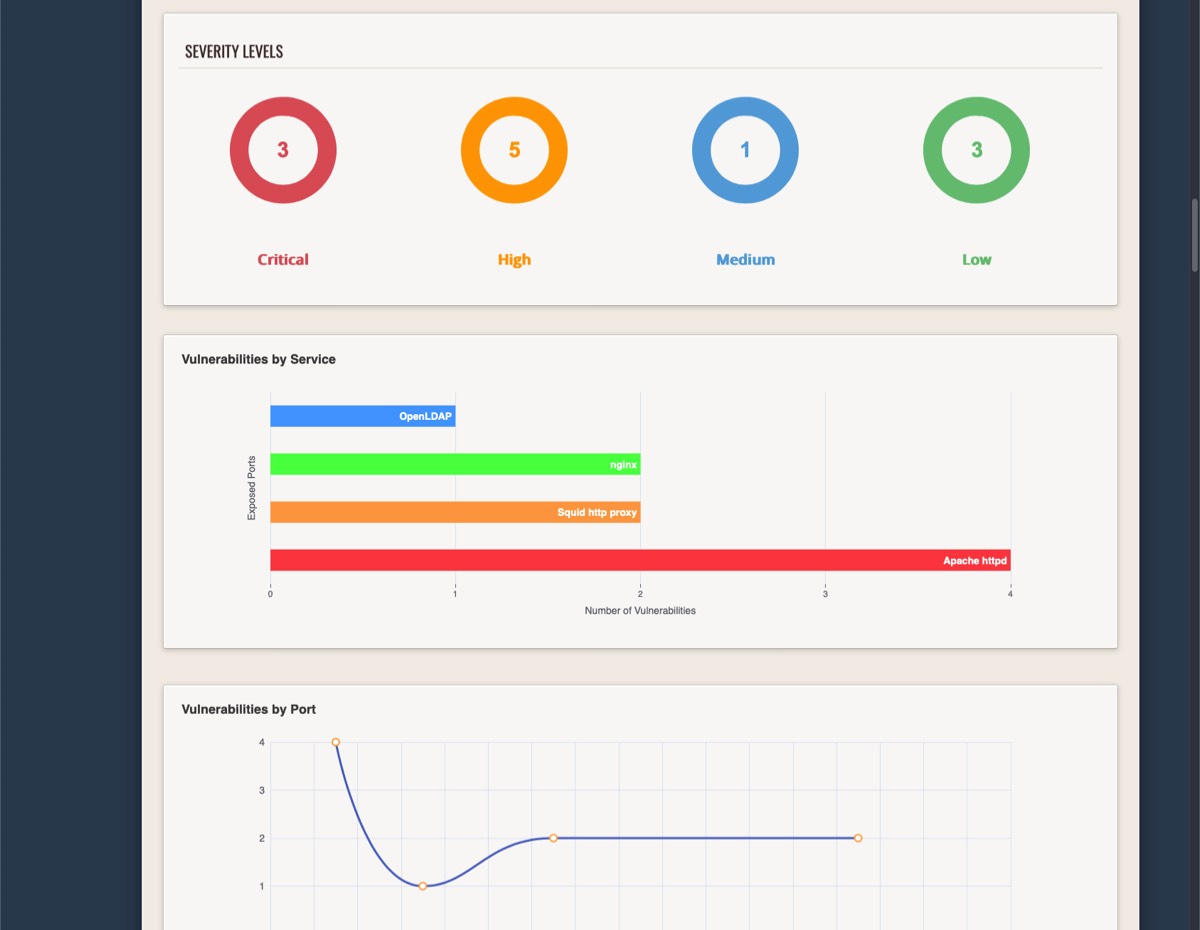
Image Title
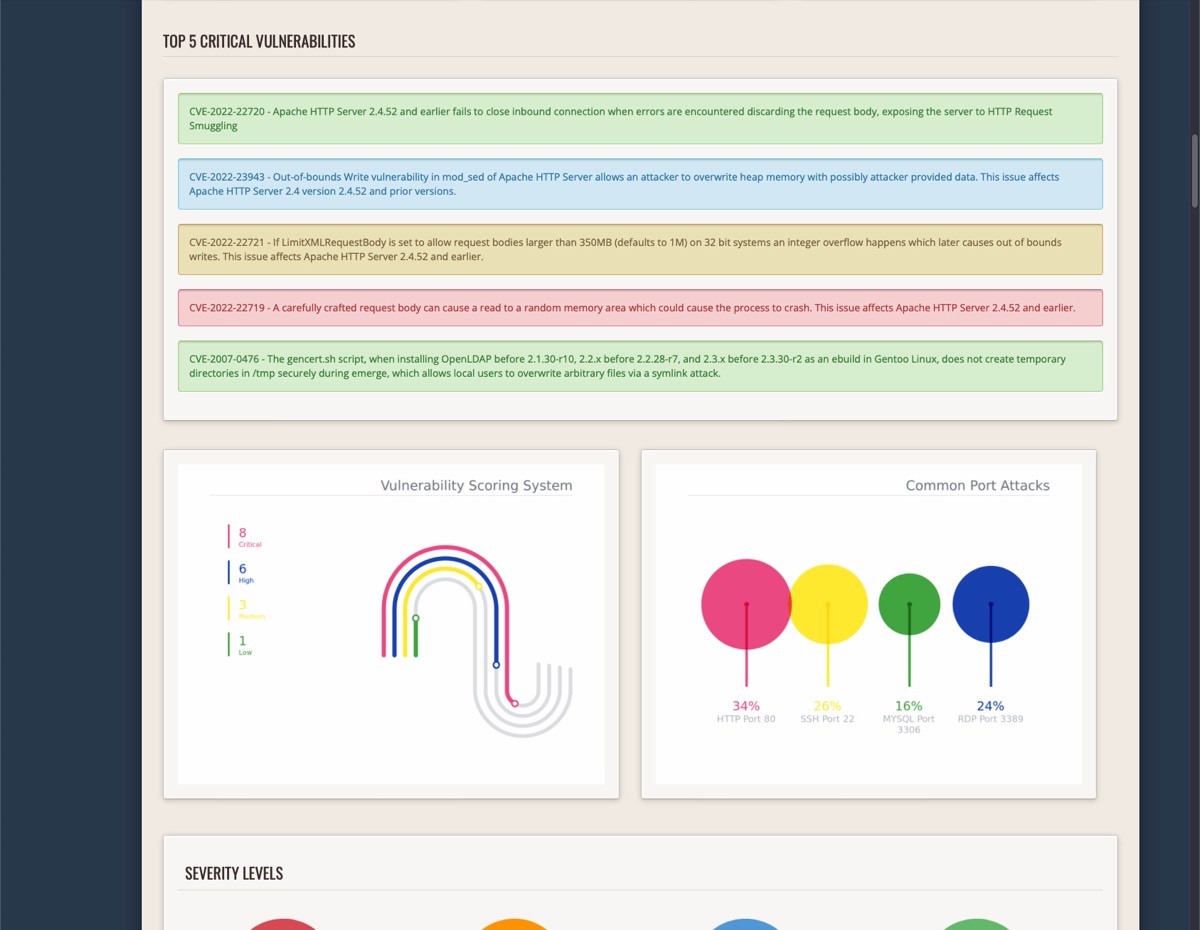
Image Title

Image Title
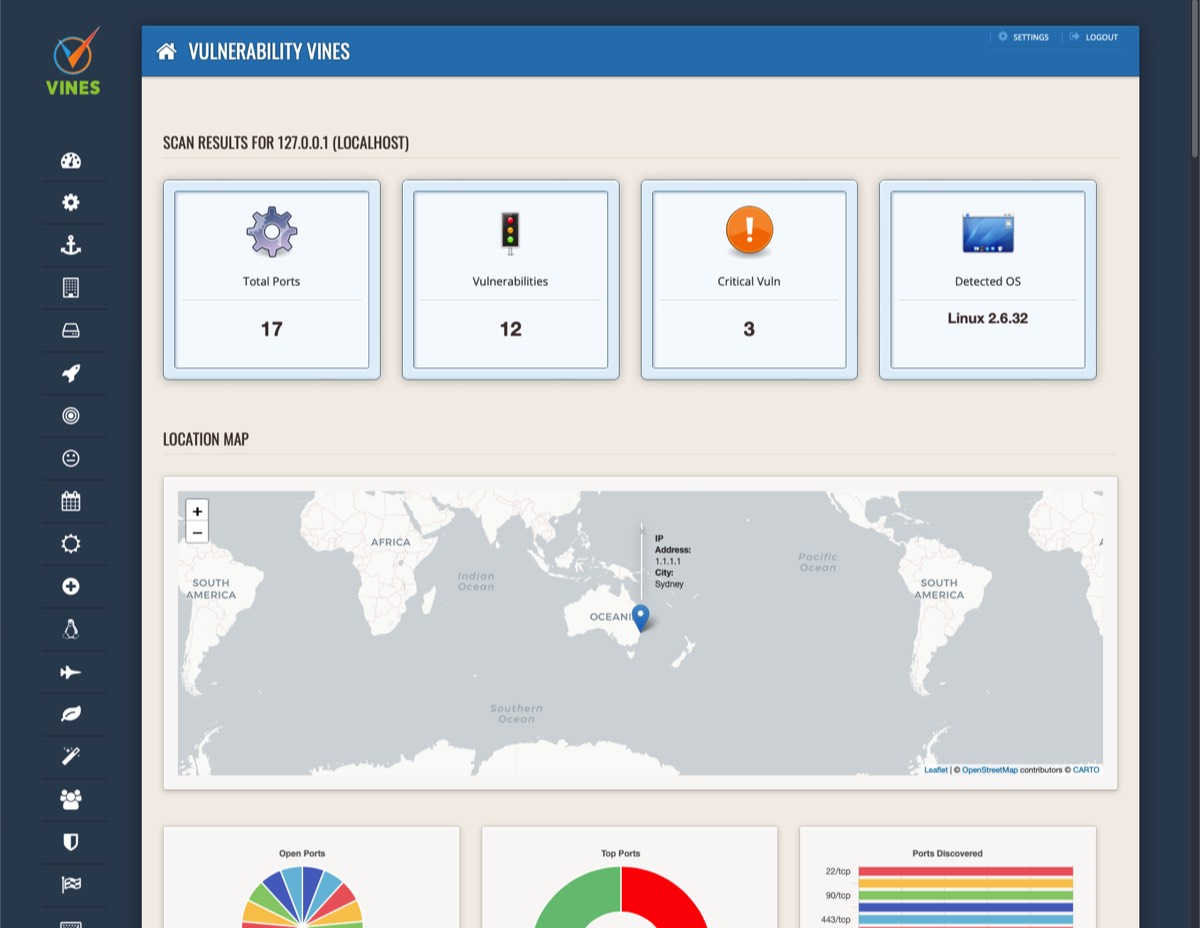
Image Title
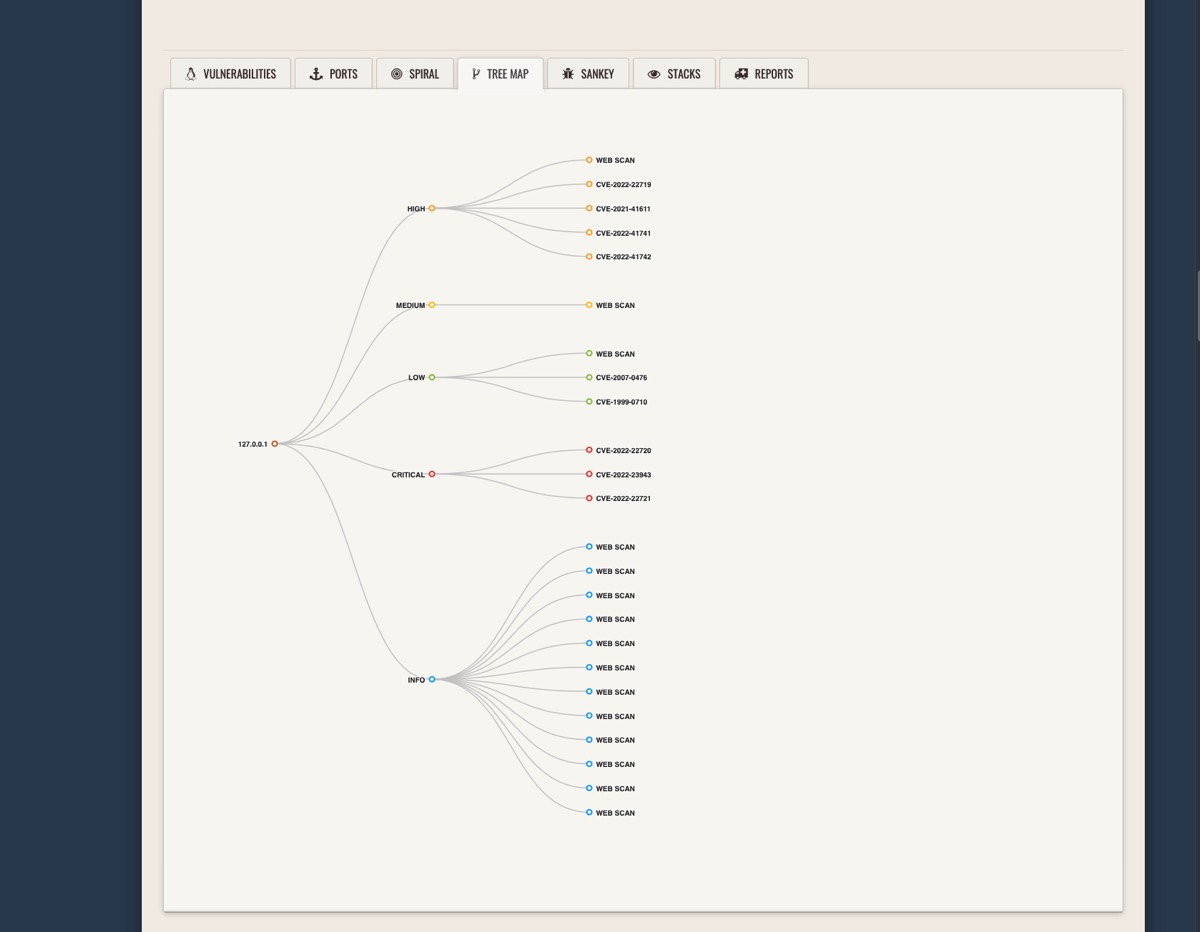
Image Title
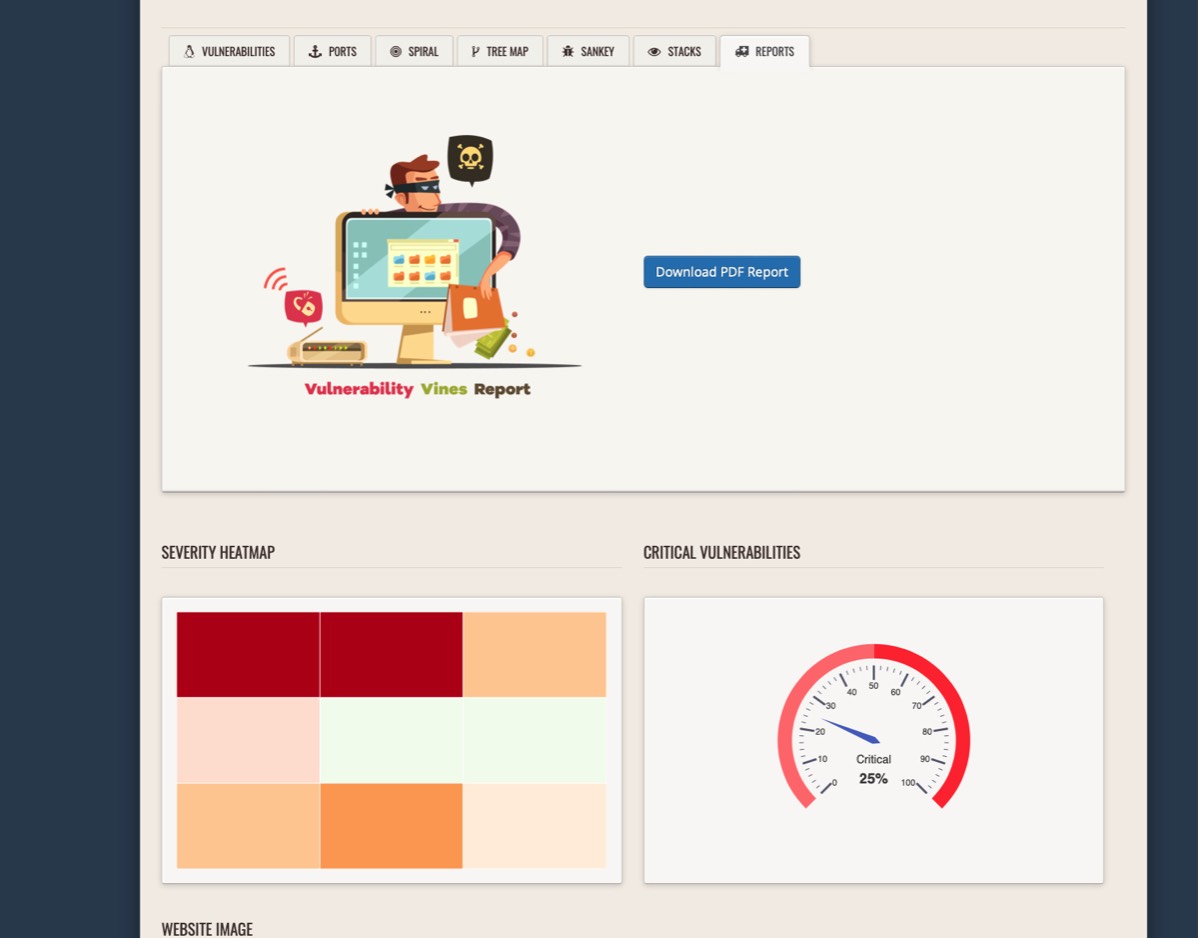
Image Title
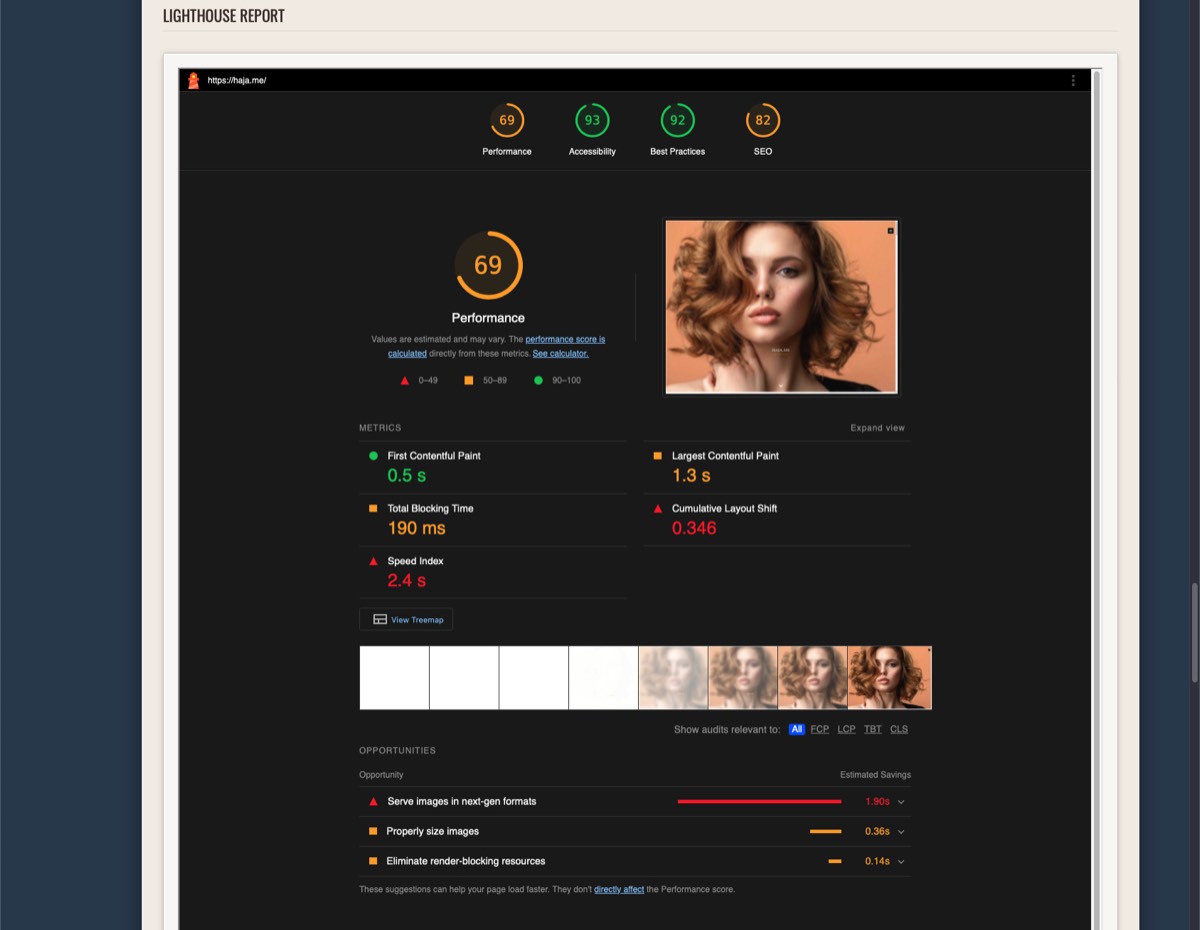
Image Title
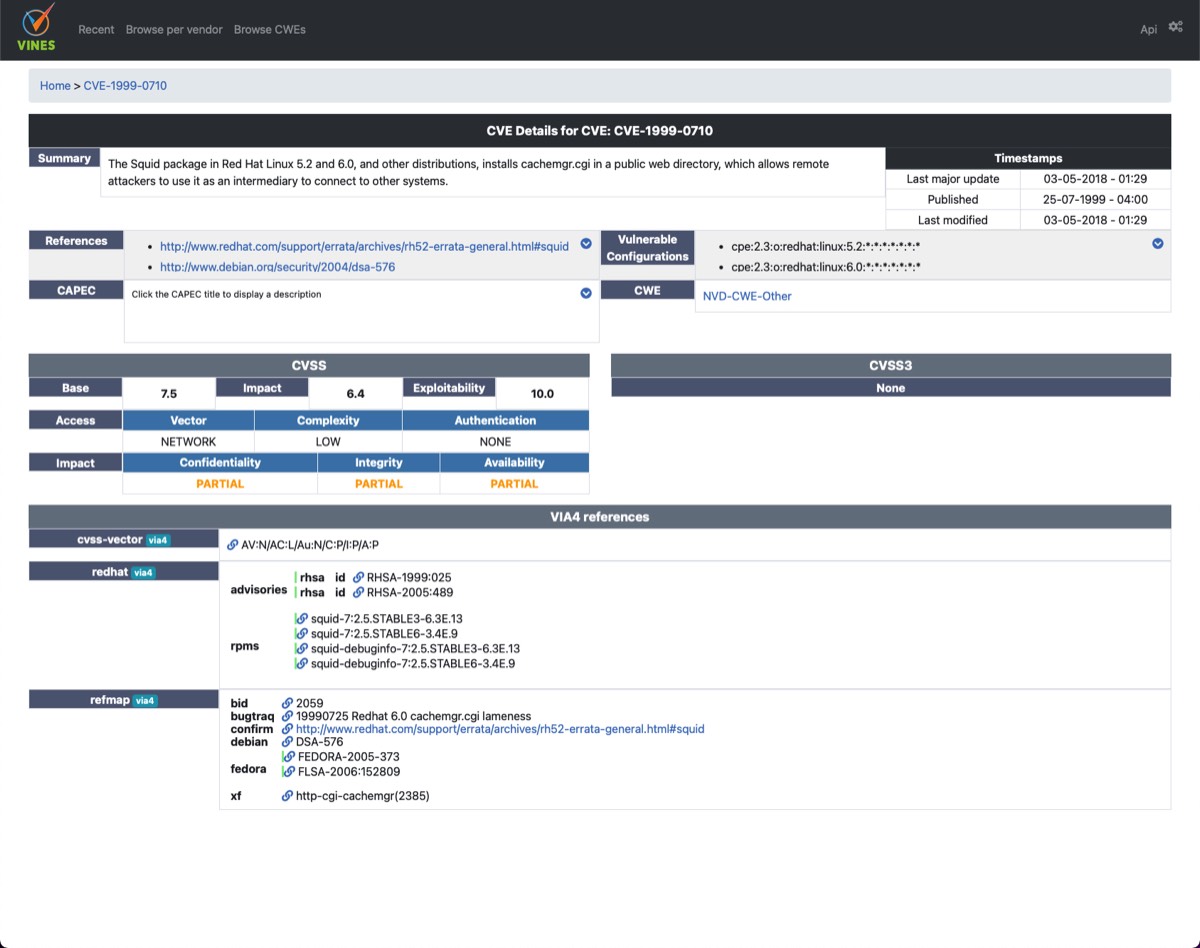
Image Title

Image Title
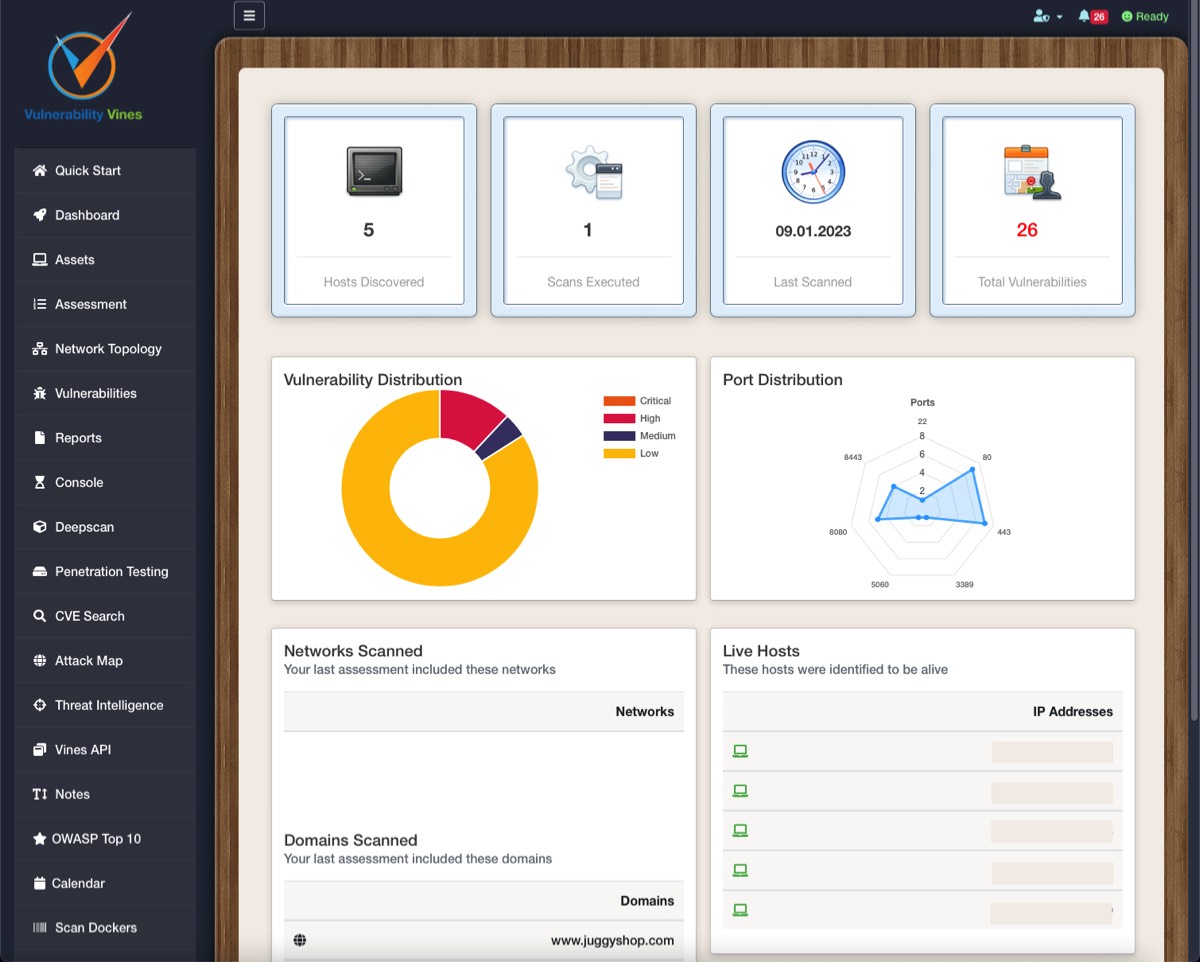
Image Title
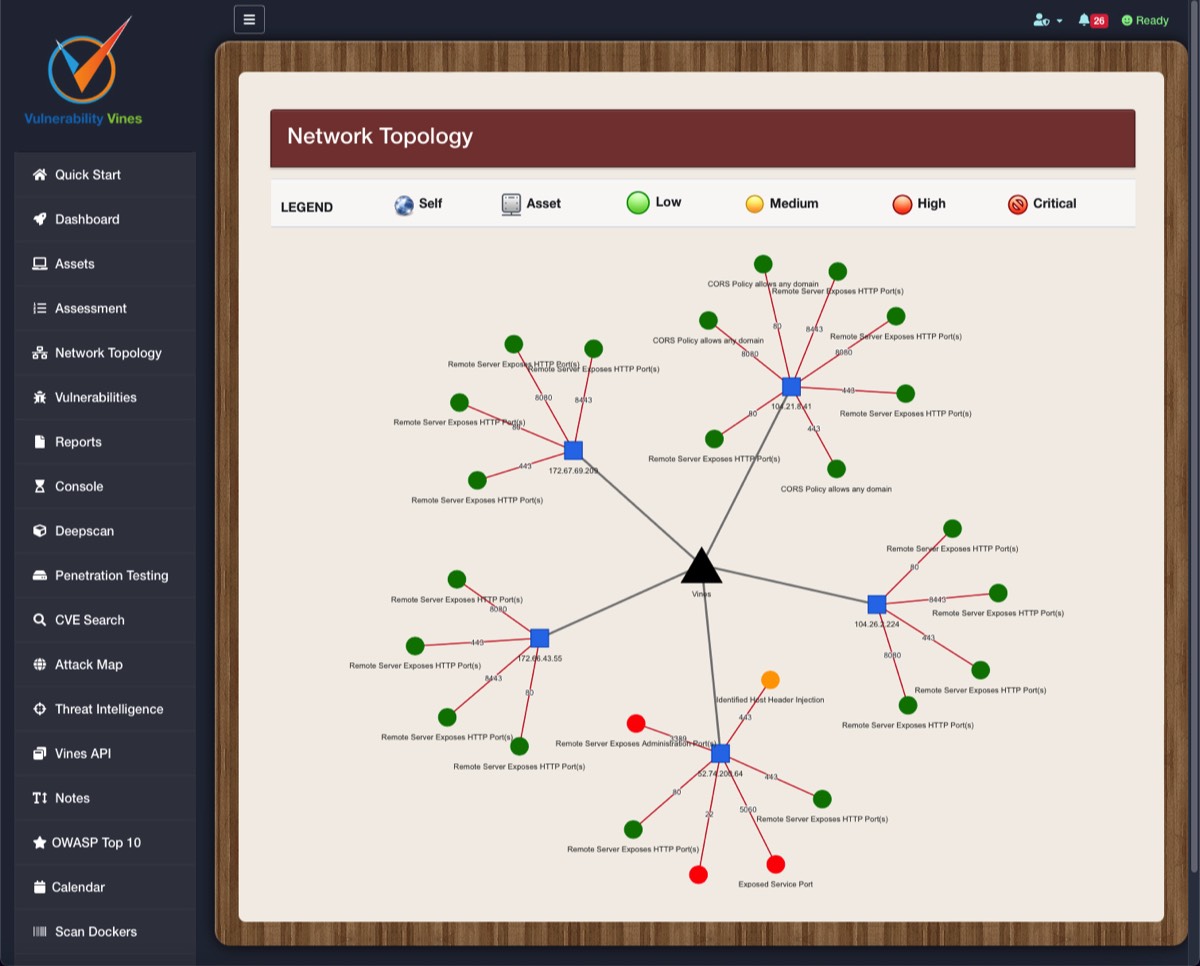
Image Title
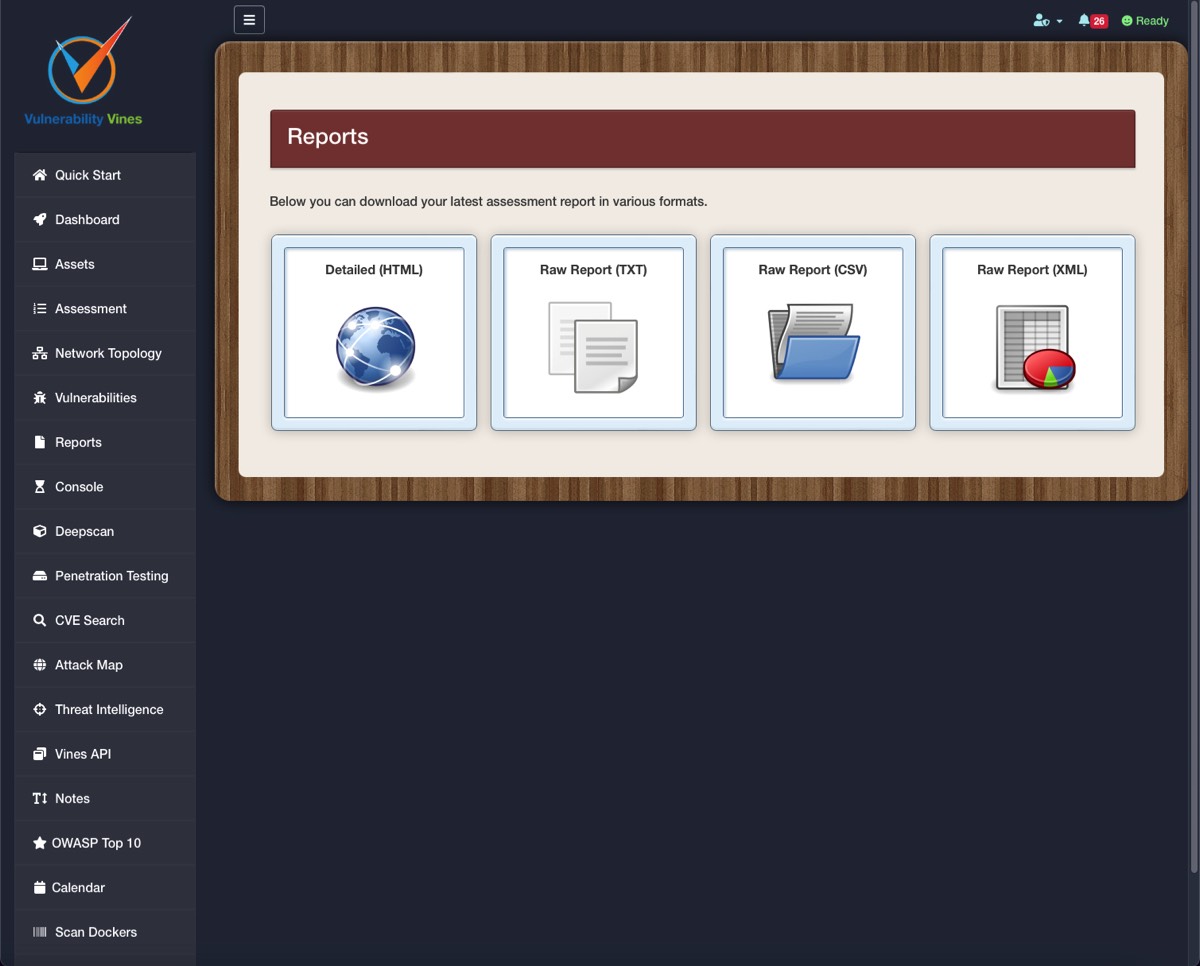
Image Title
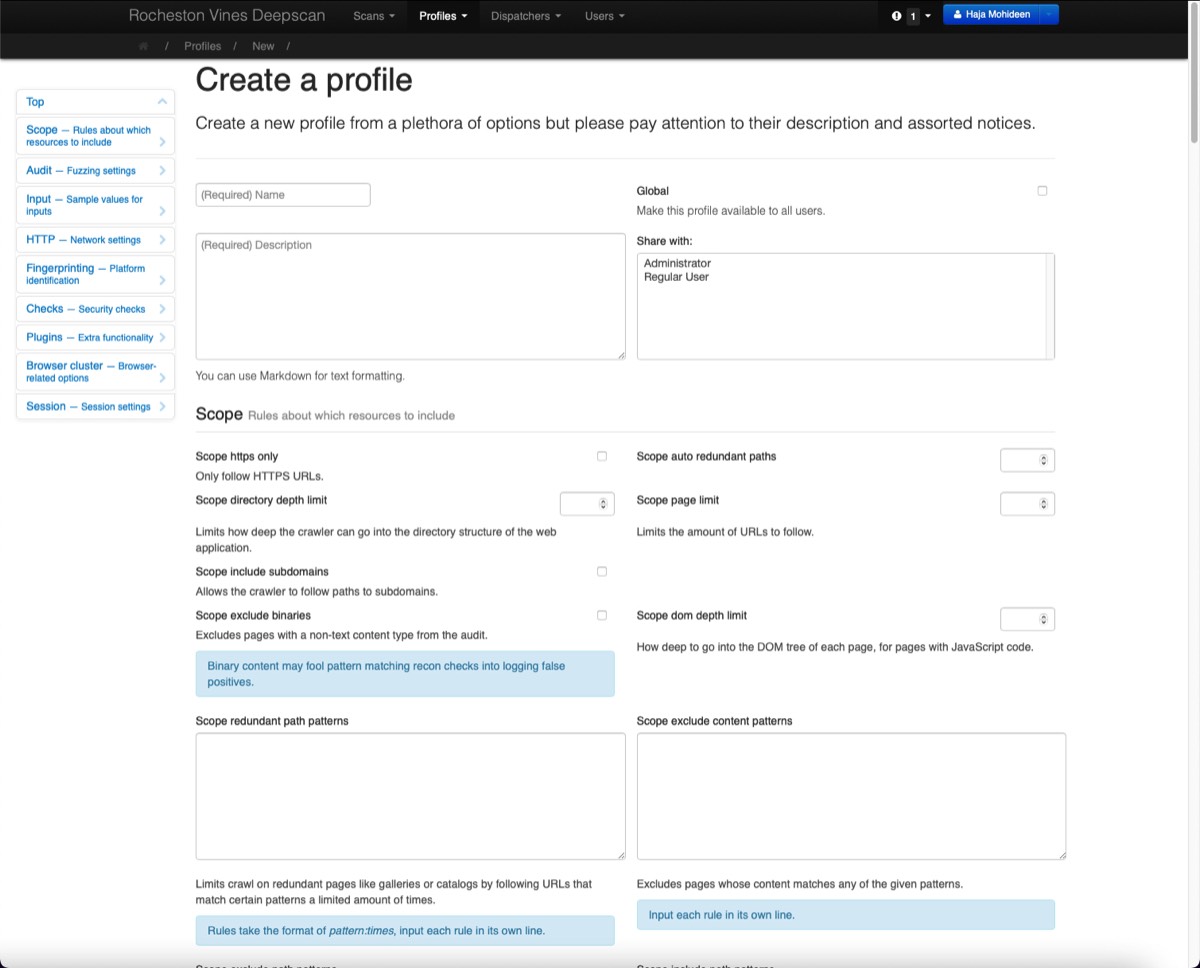
Image Title
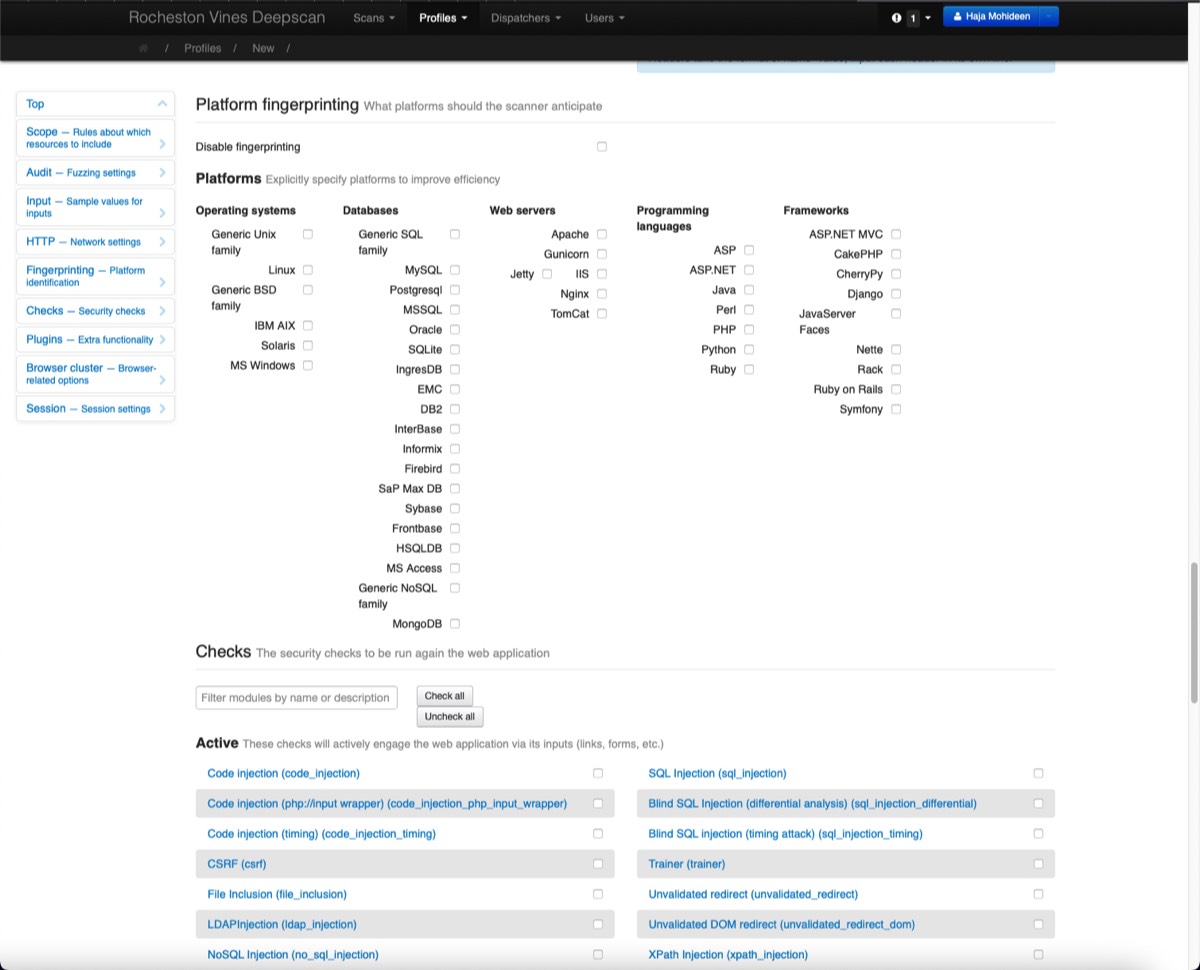
Image Title
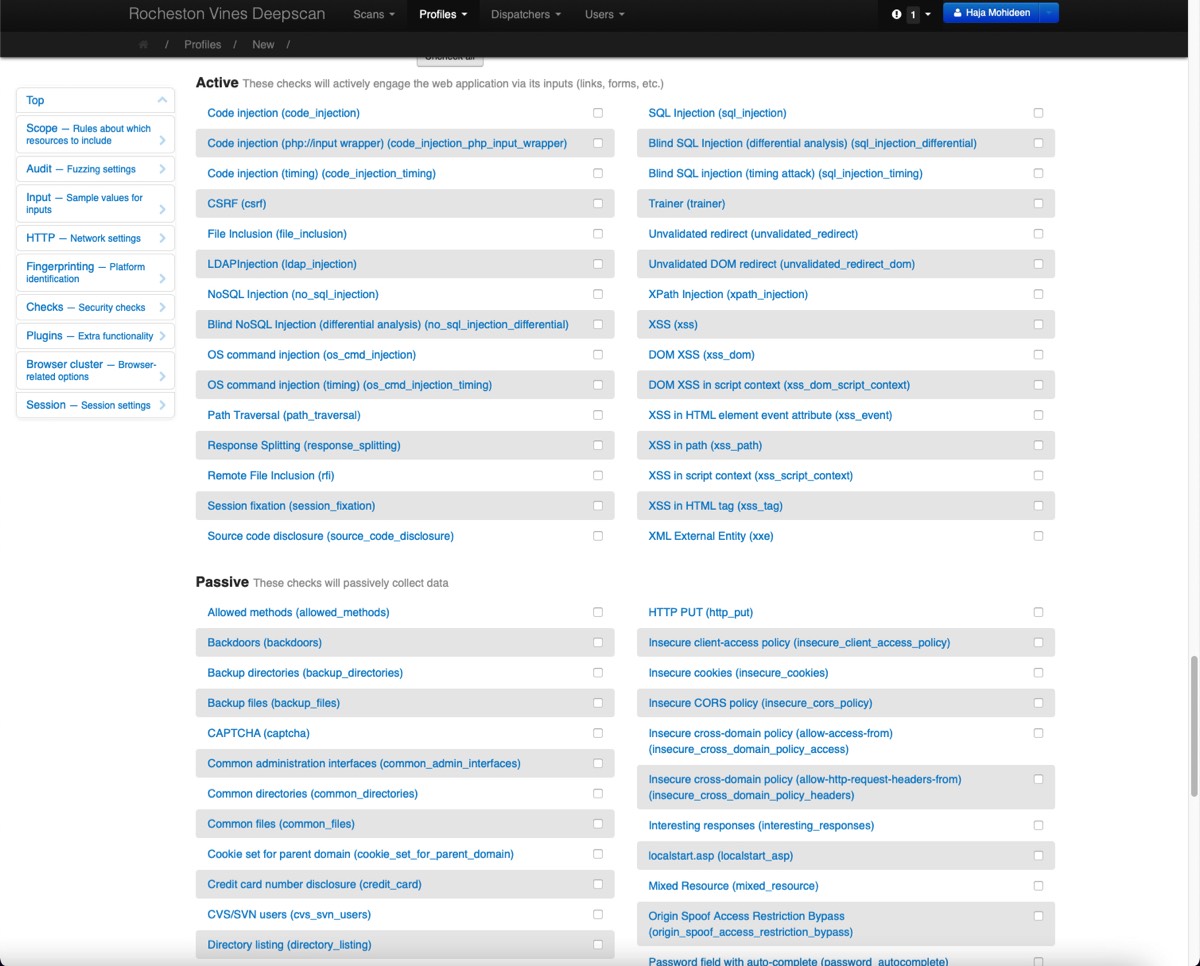
Image Title
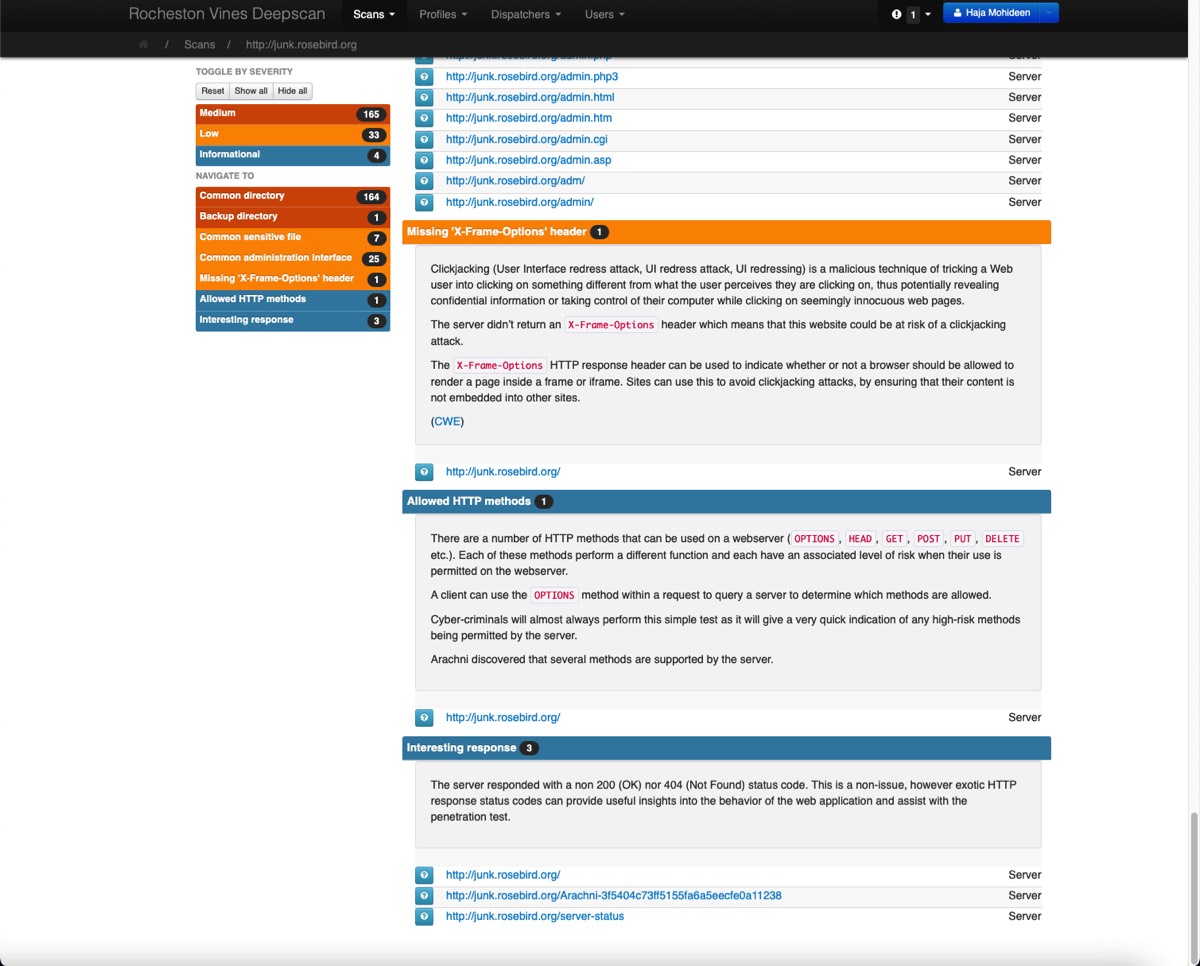
Image Title
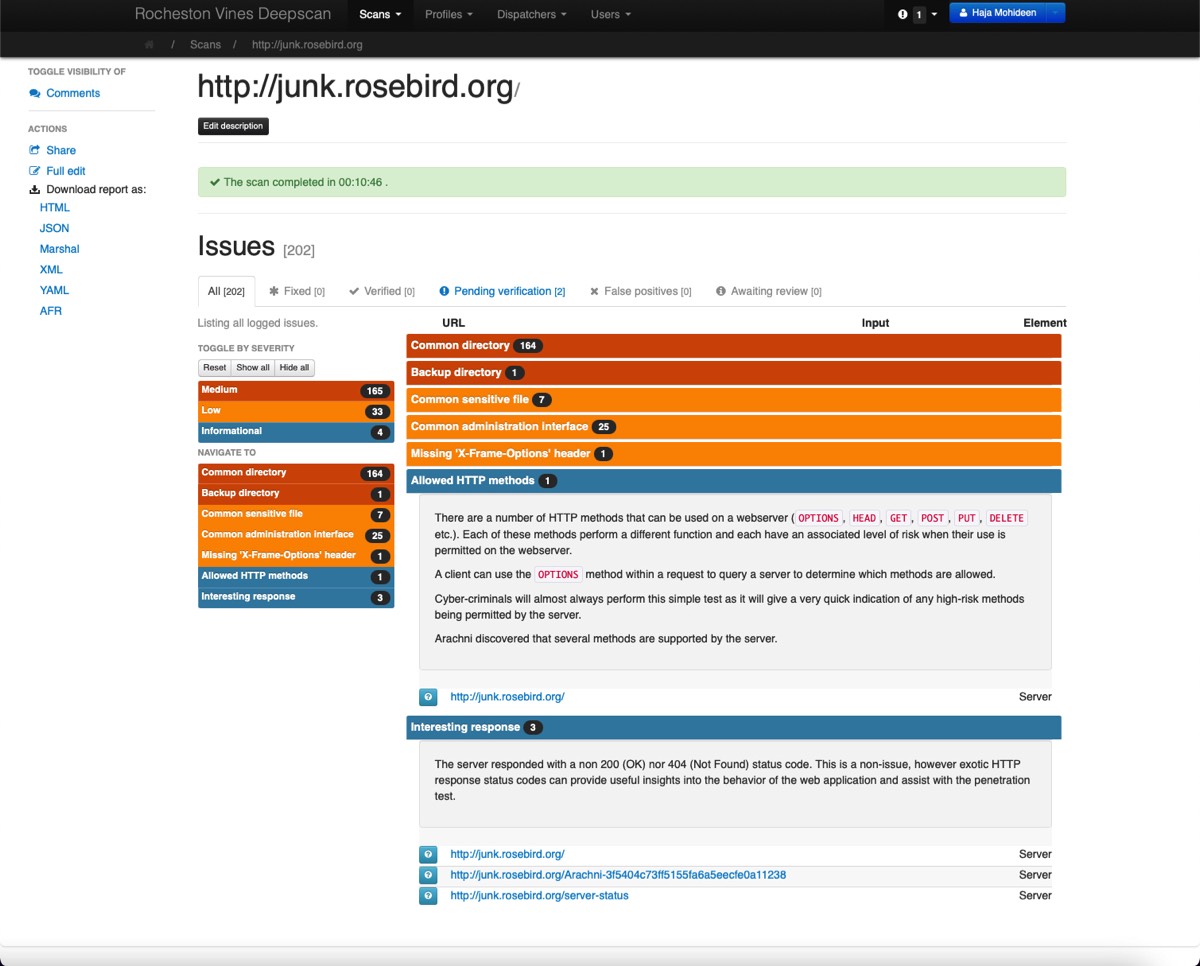
Image Title
Image Title
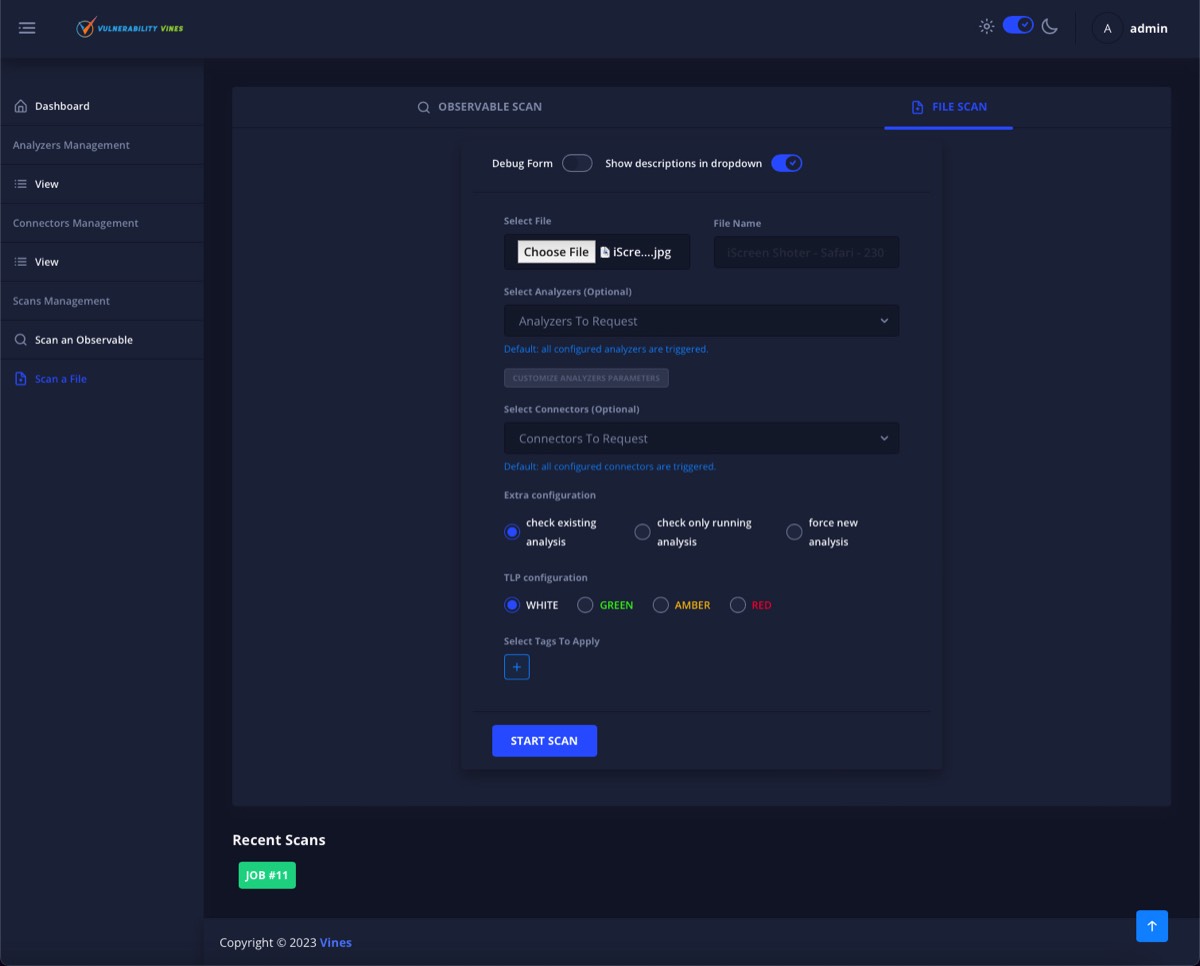
Image Title
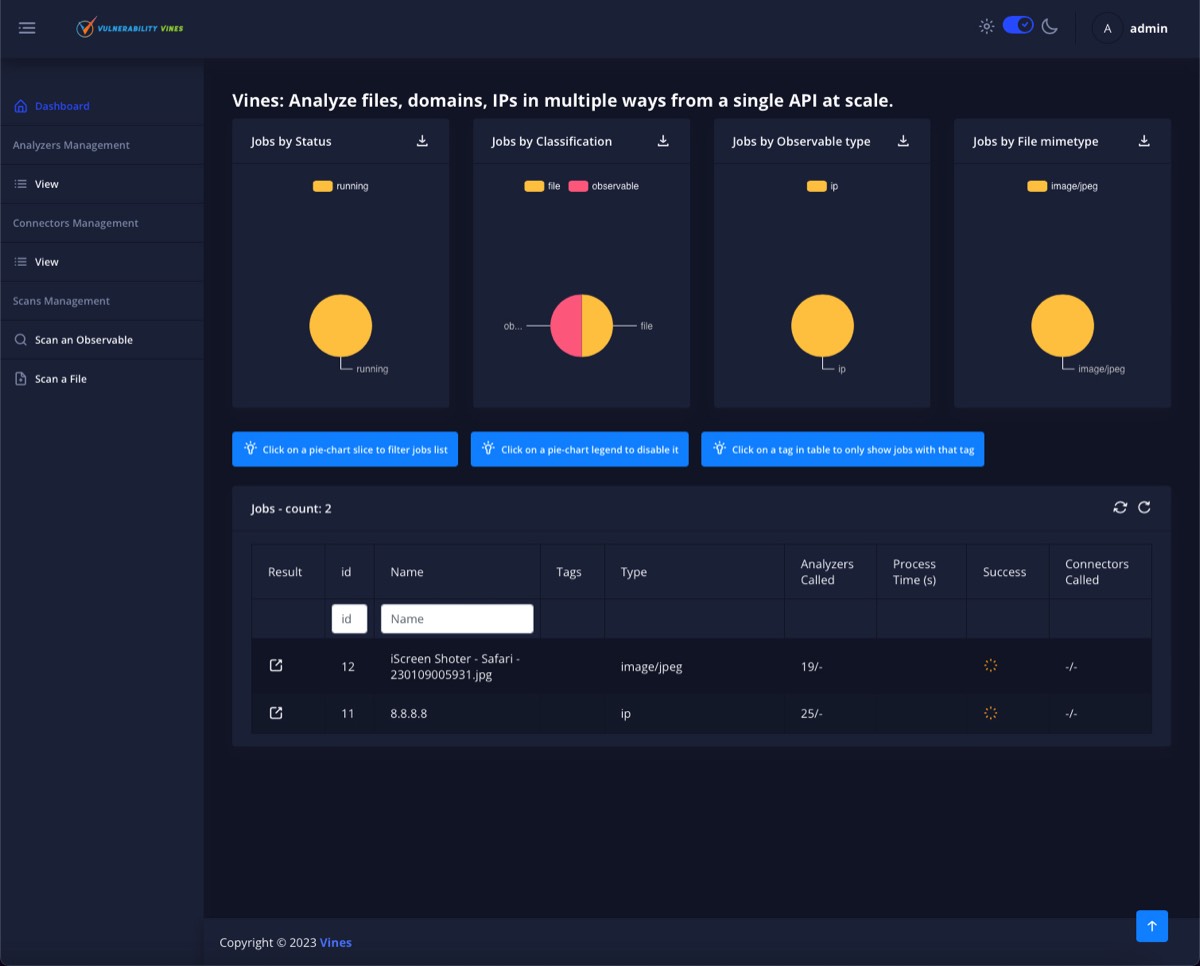
Image Title
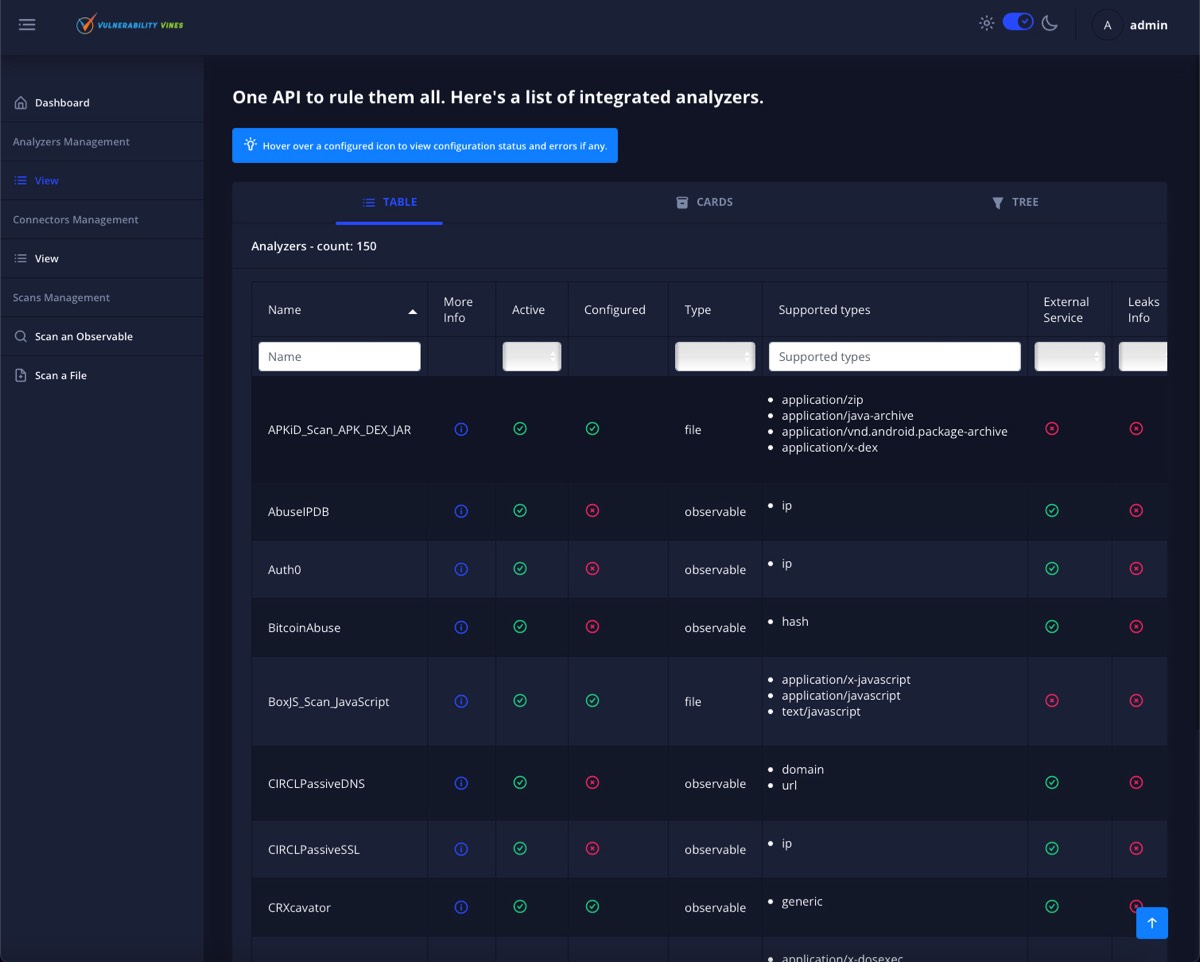
Image Title
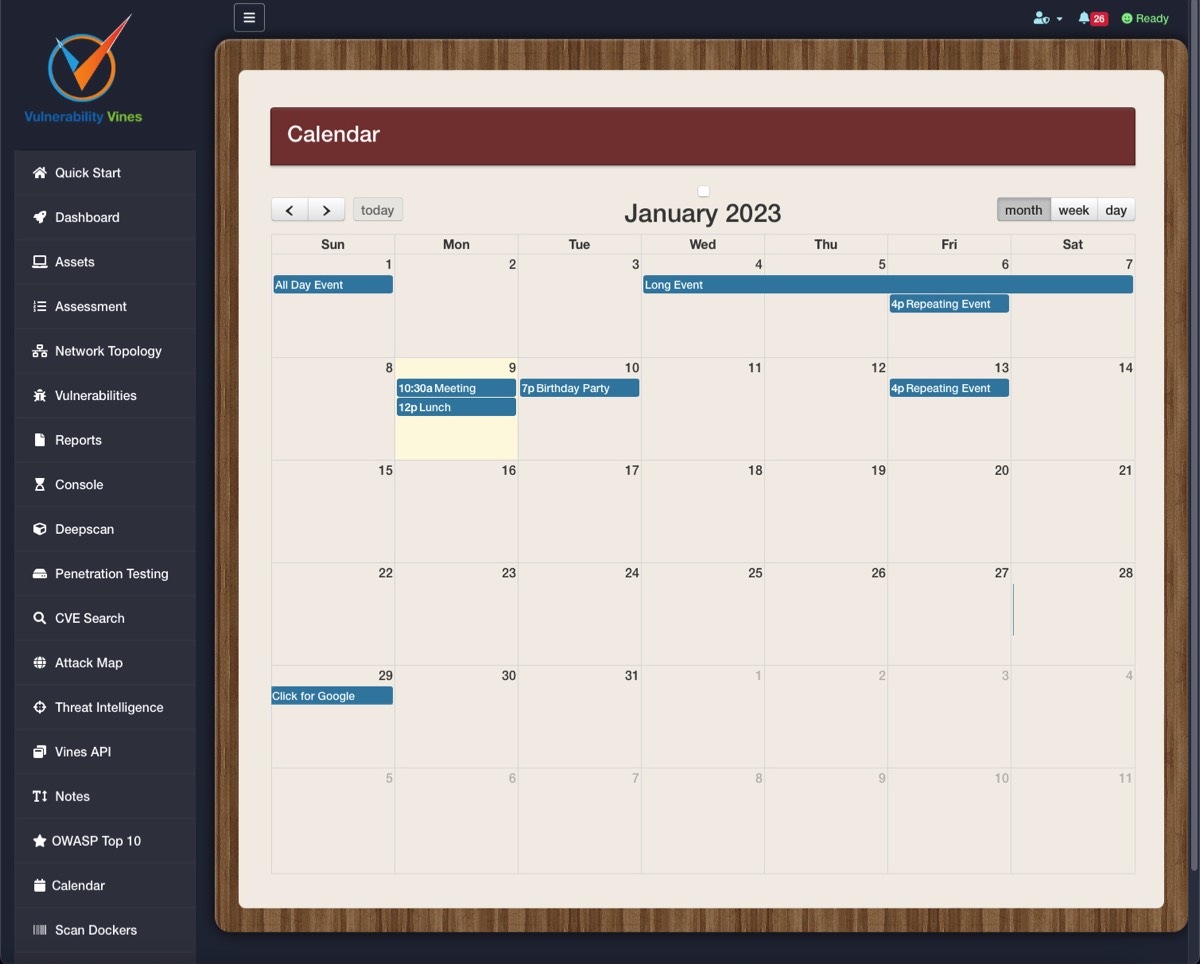
Image Title
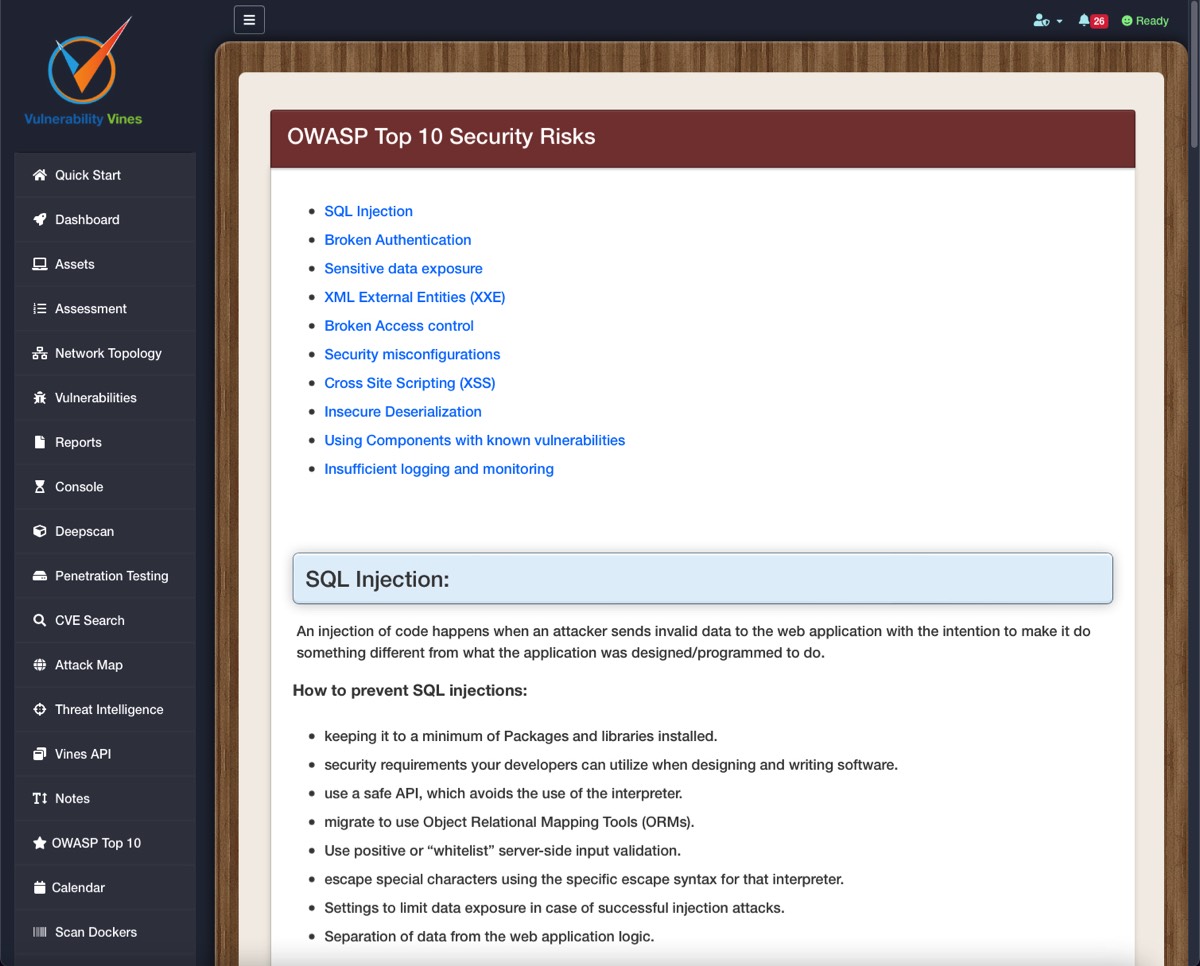
Image Title

Image Title
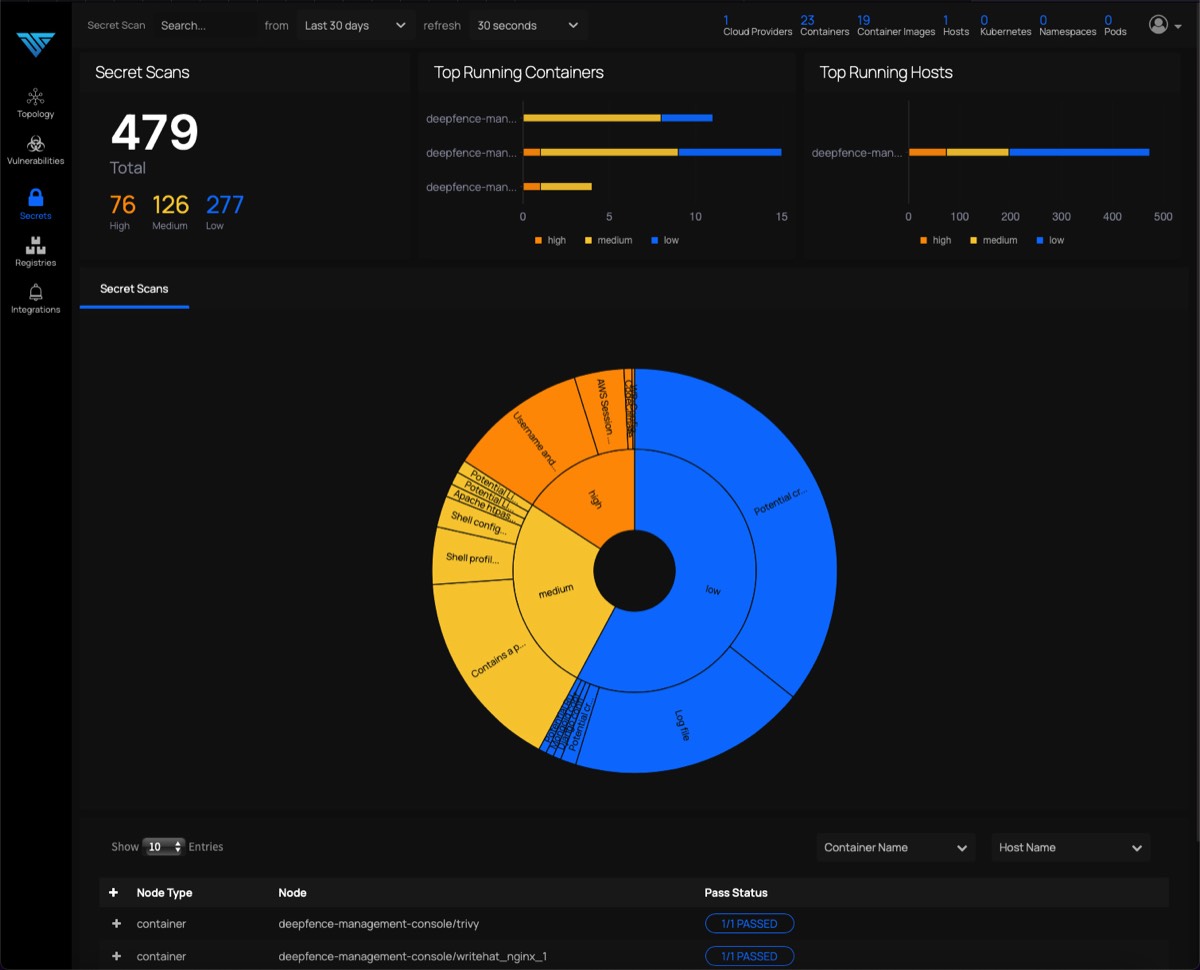
Image Title
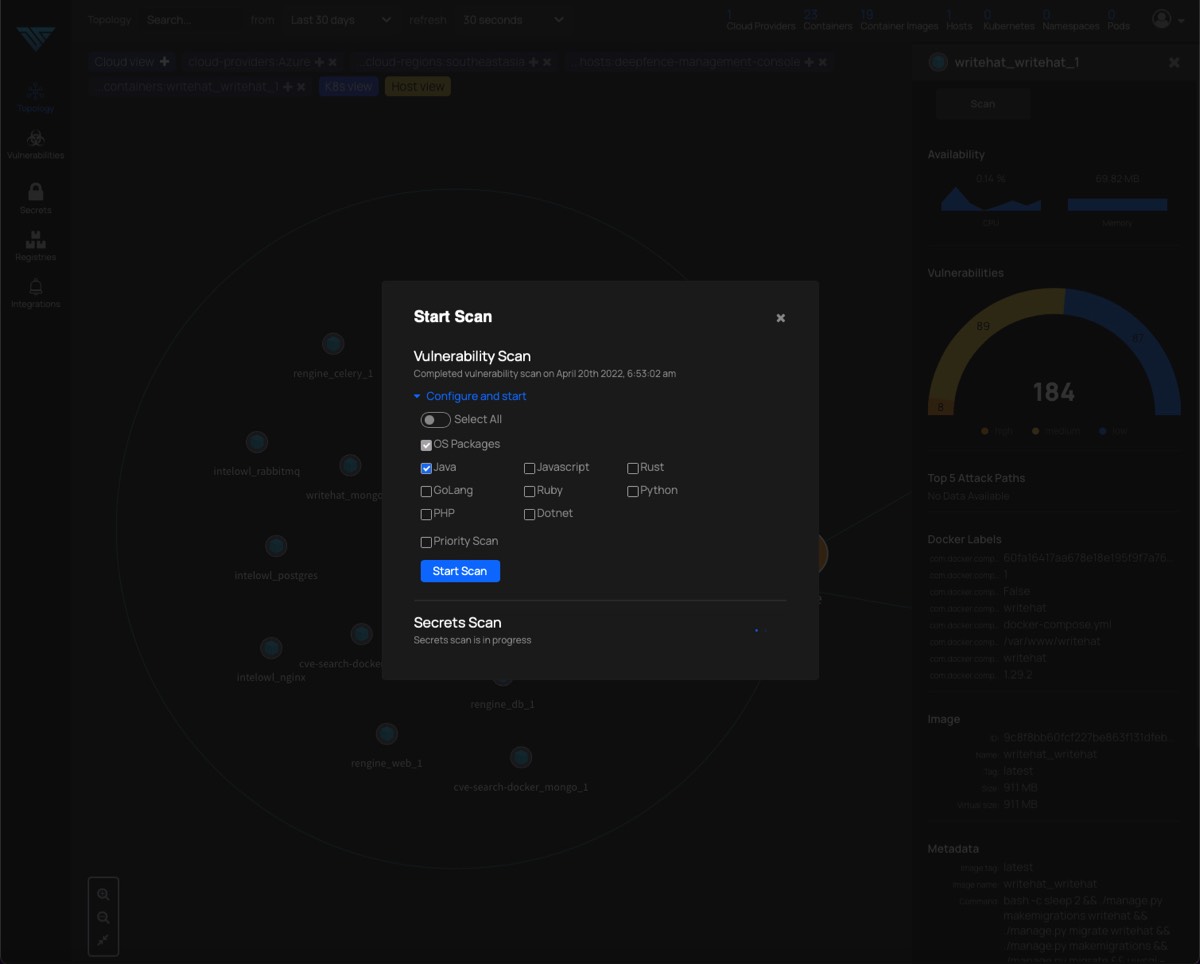
Image Title
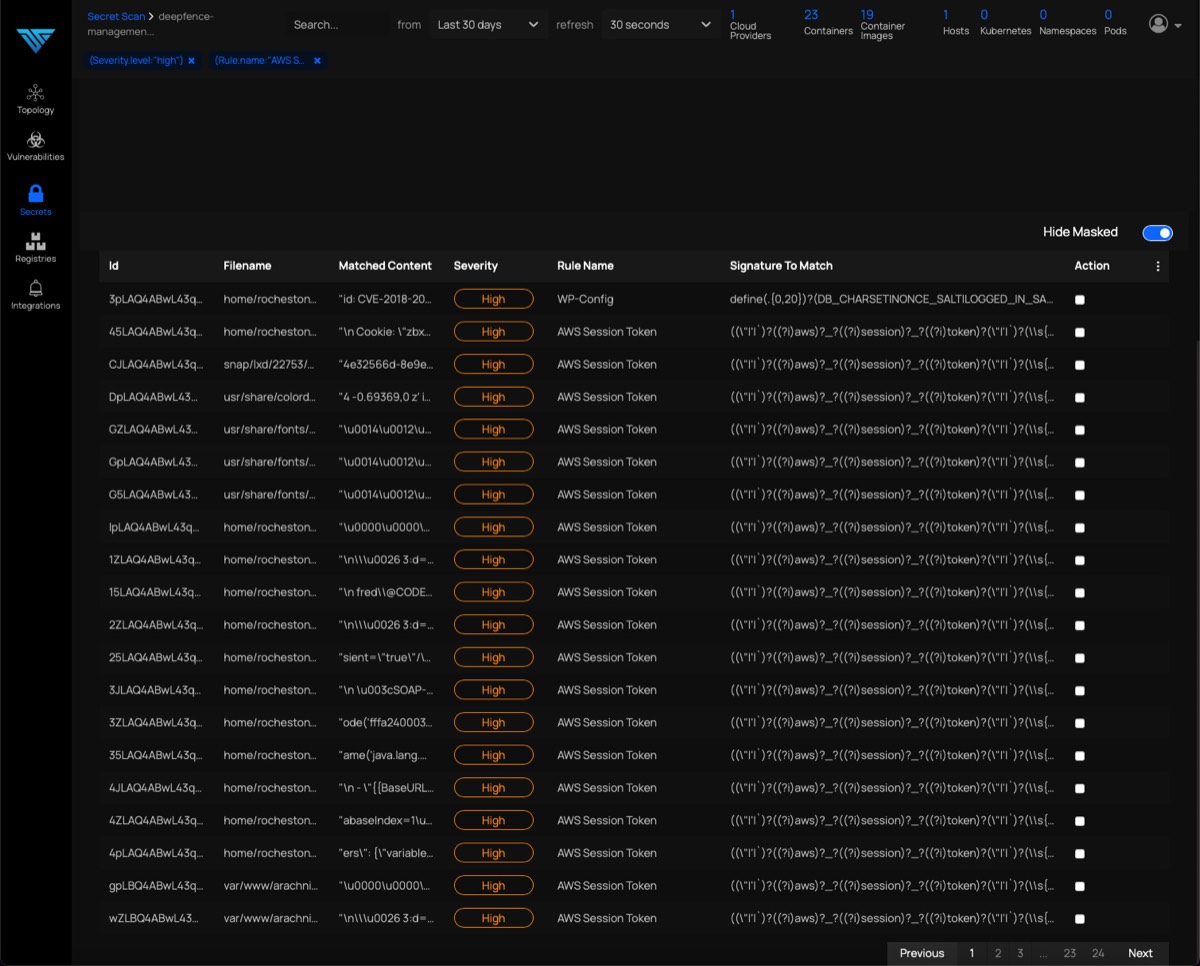
Image Title
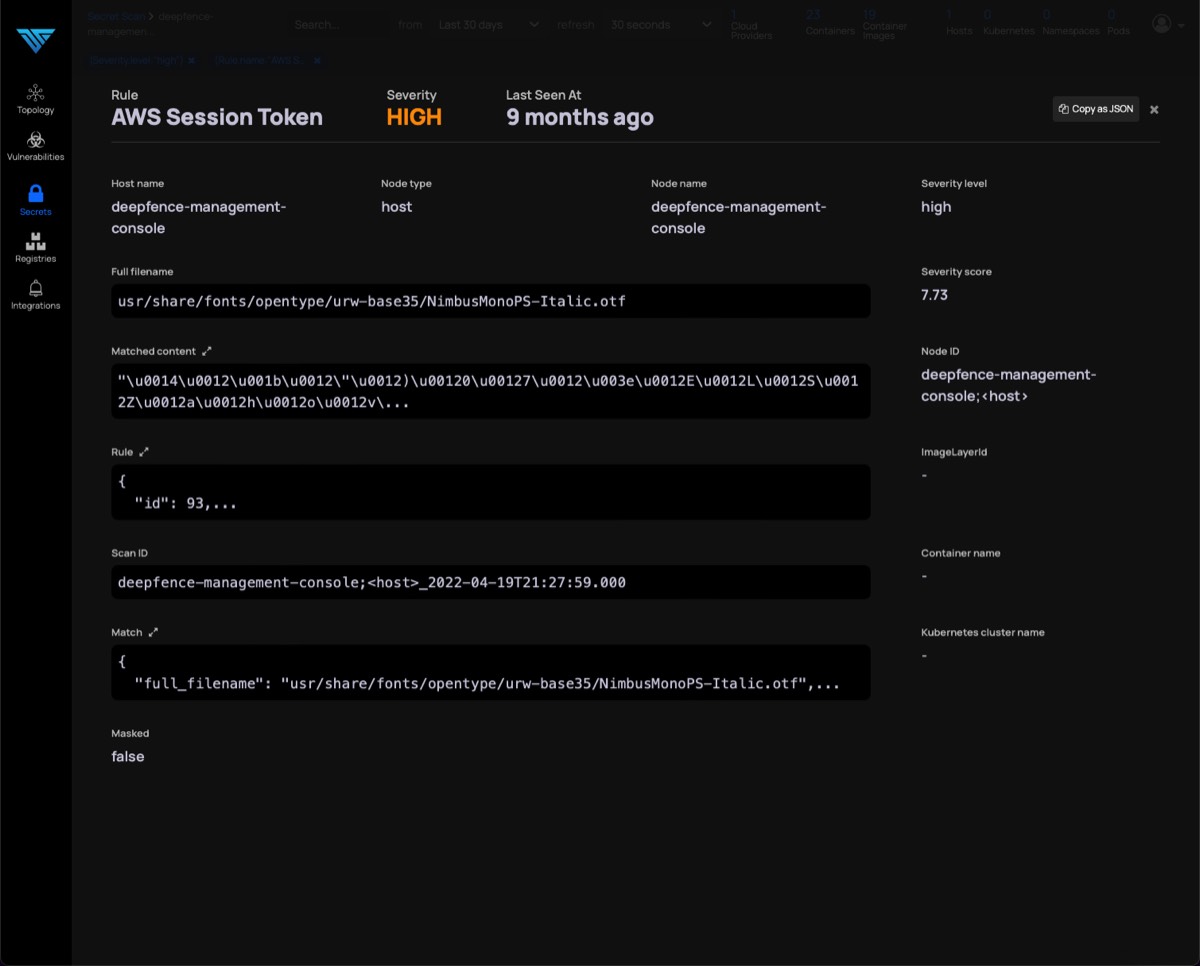
Image Title
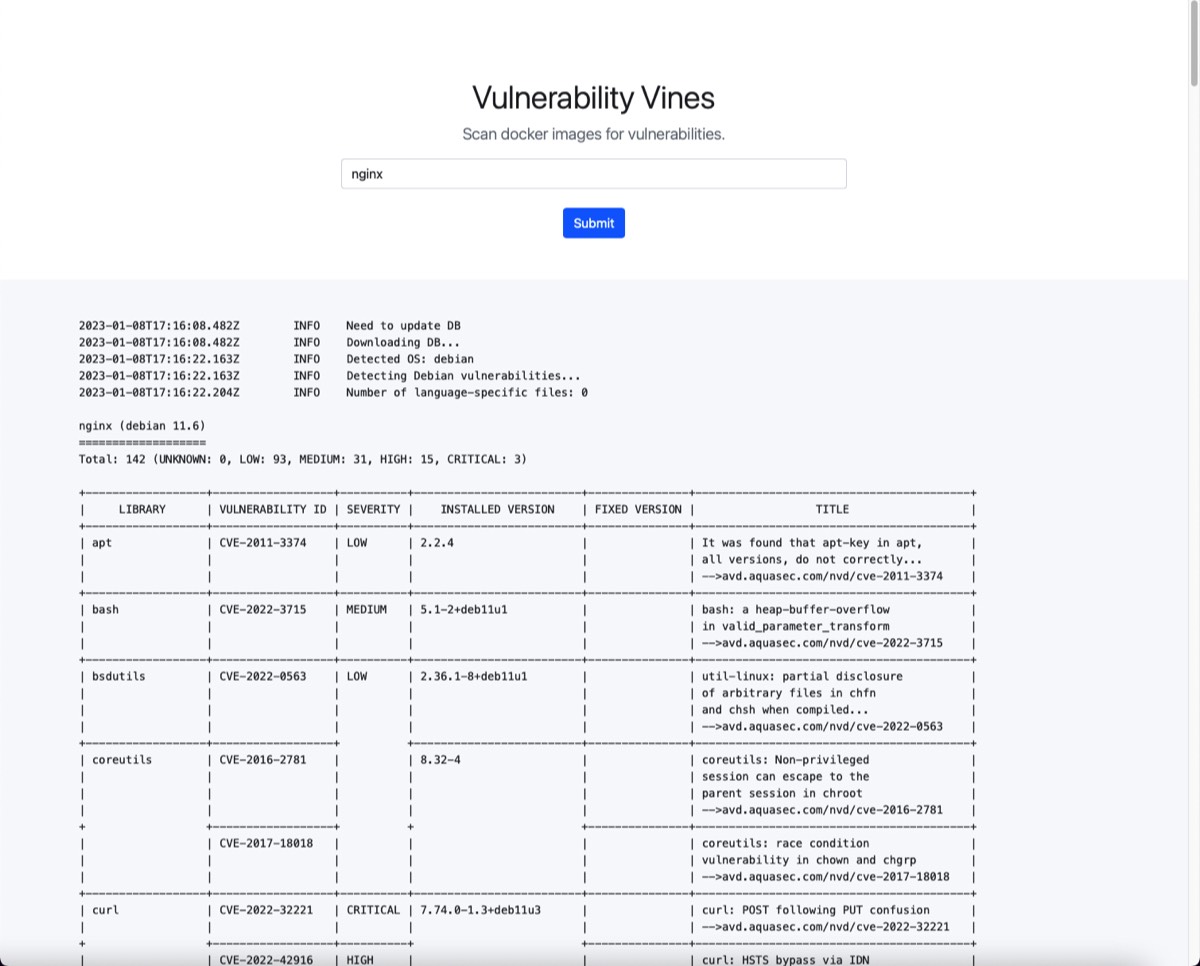
Image Title
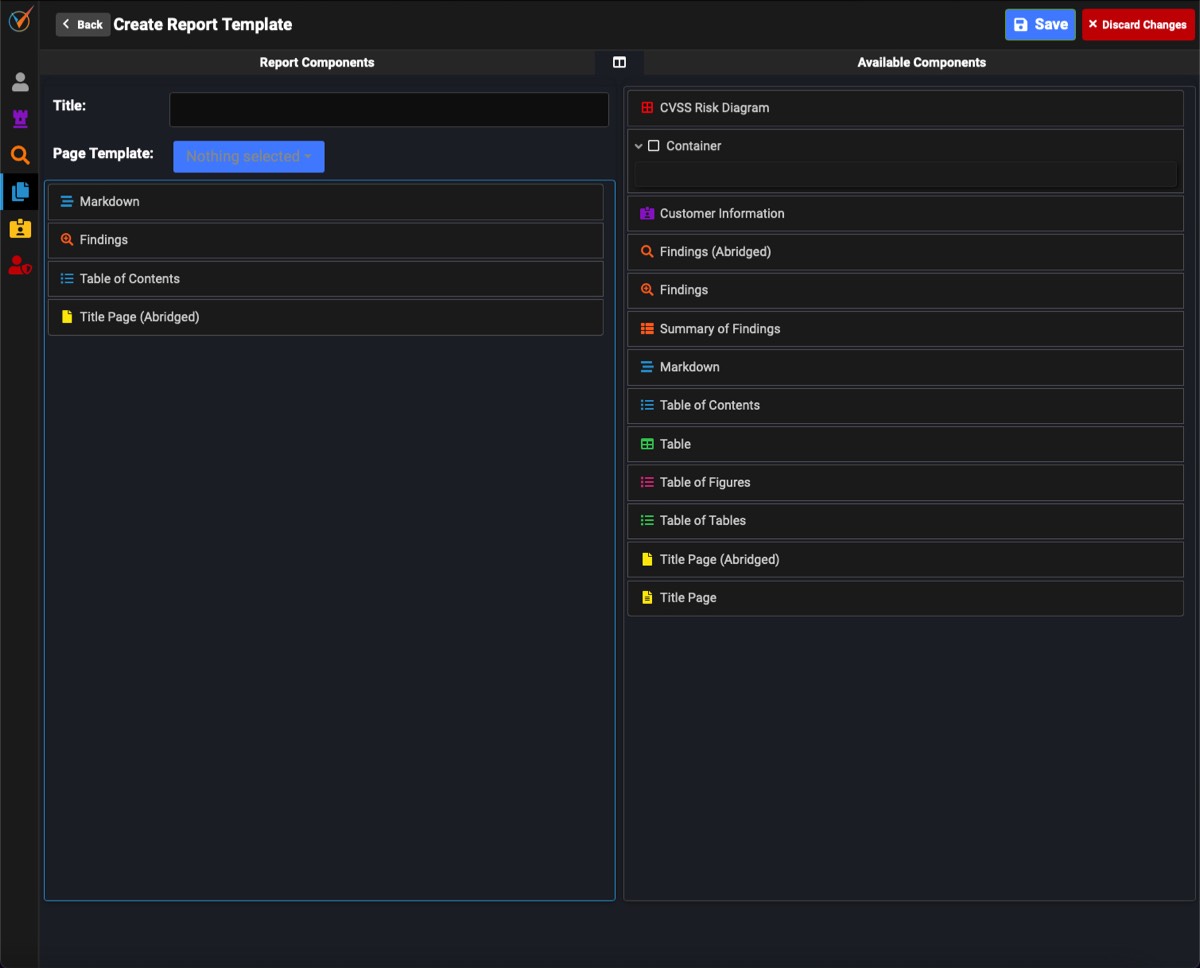
Image Title

Image Title
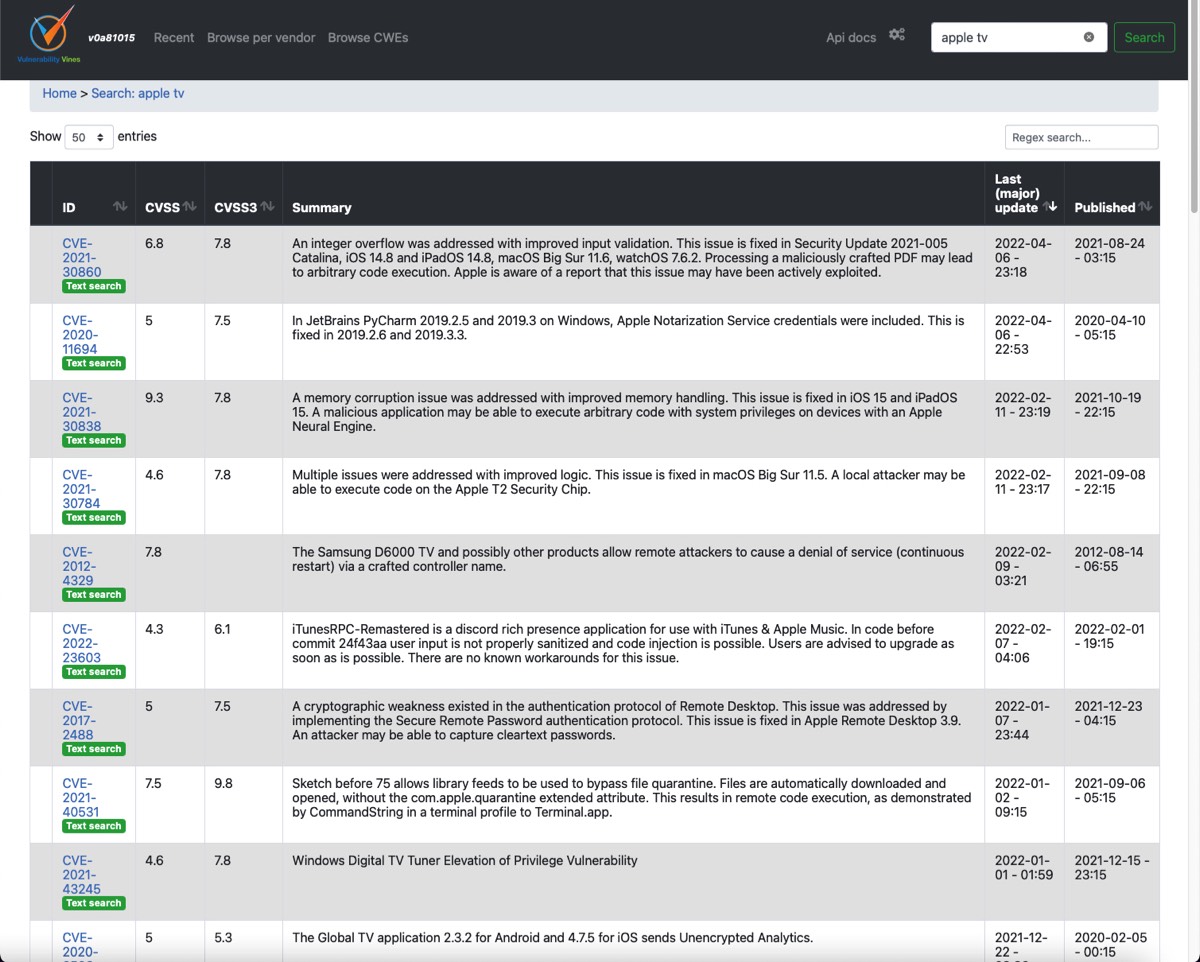
Image Title
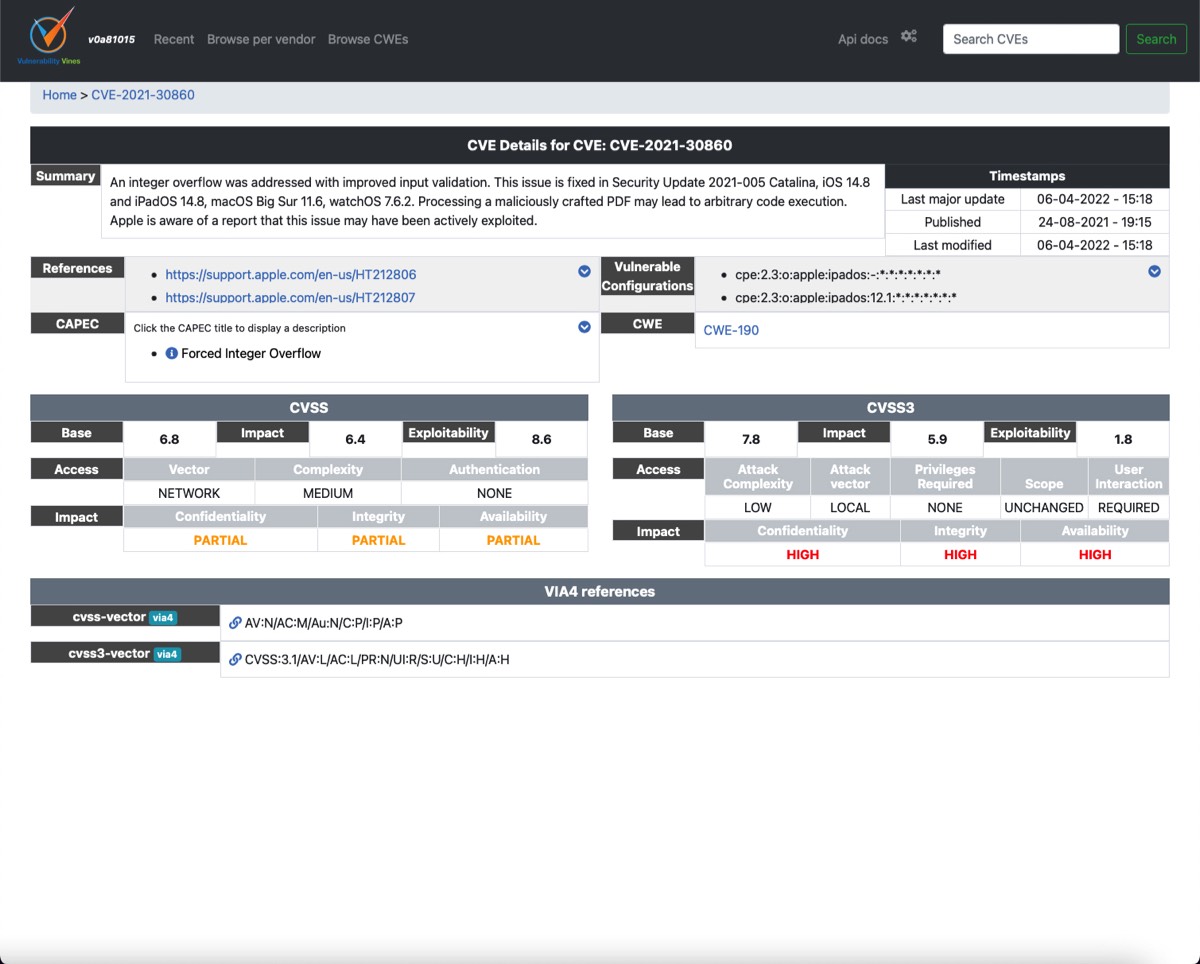
Image Title
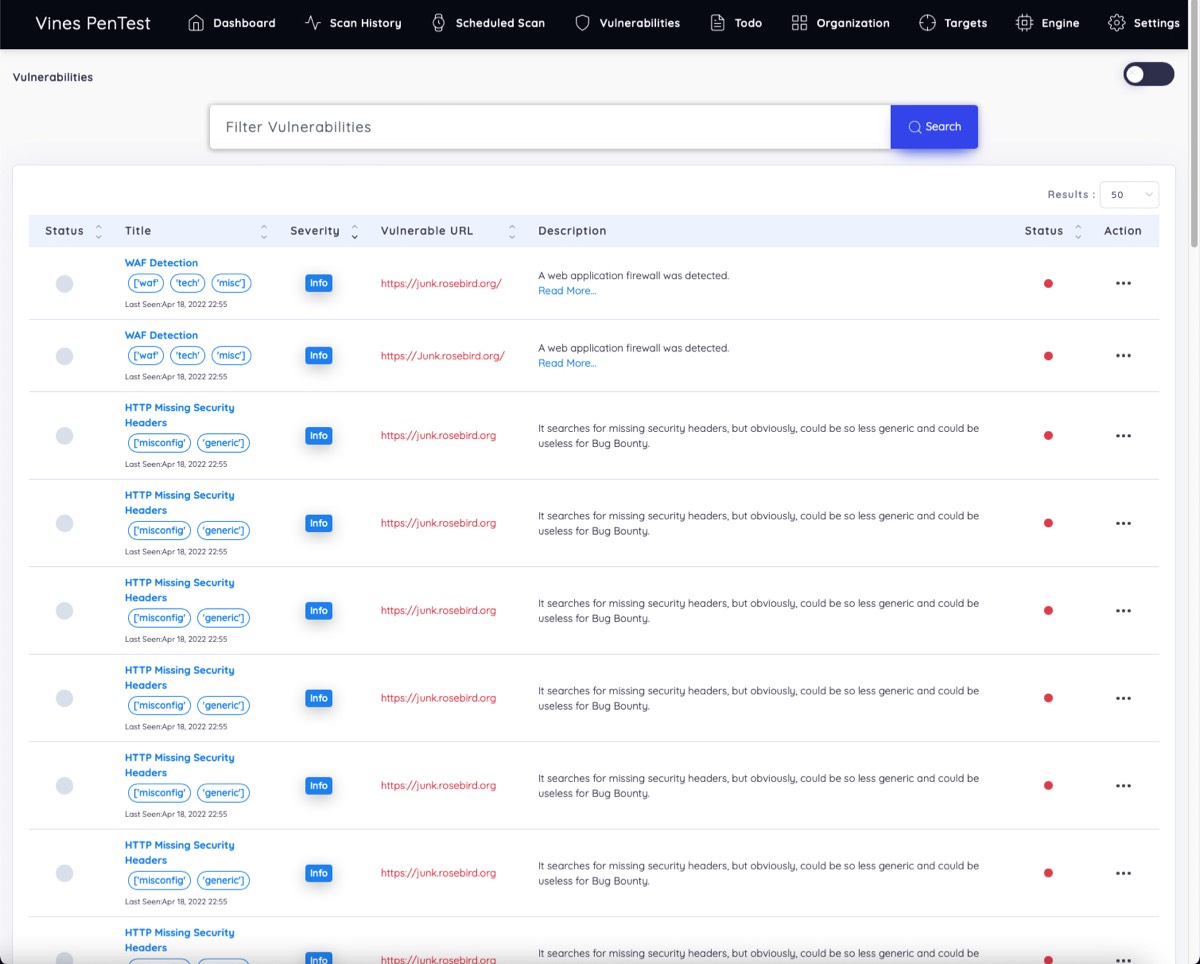
Image Title
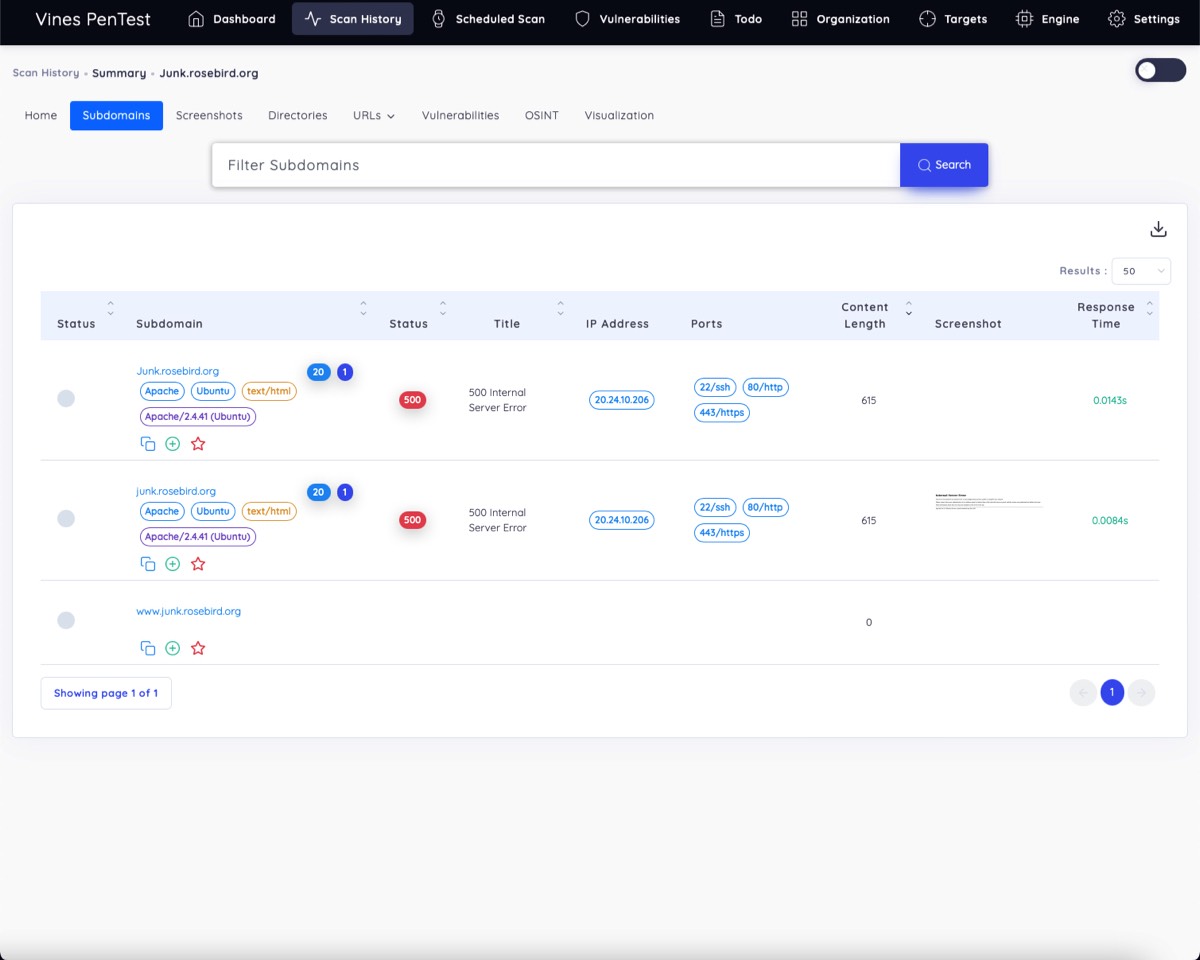
Image Title
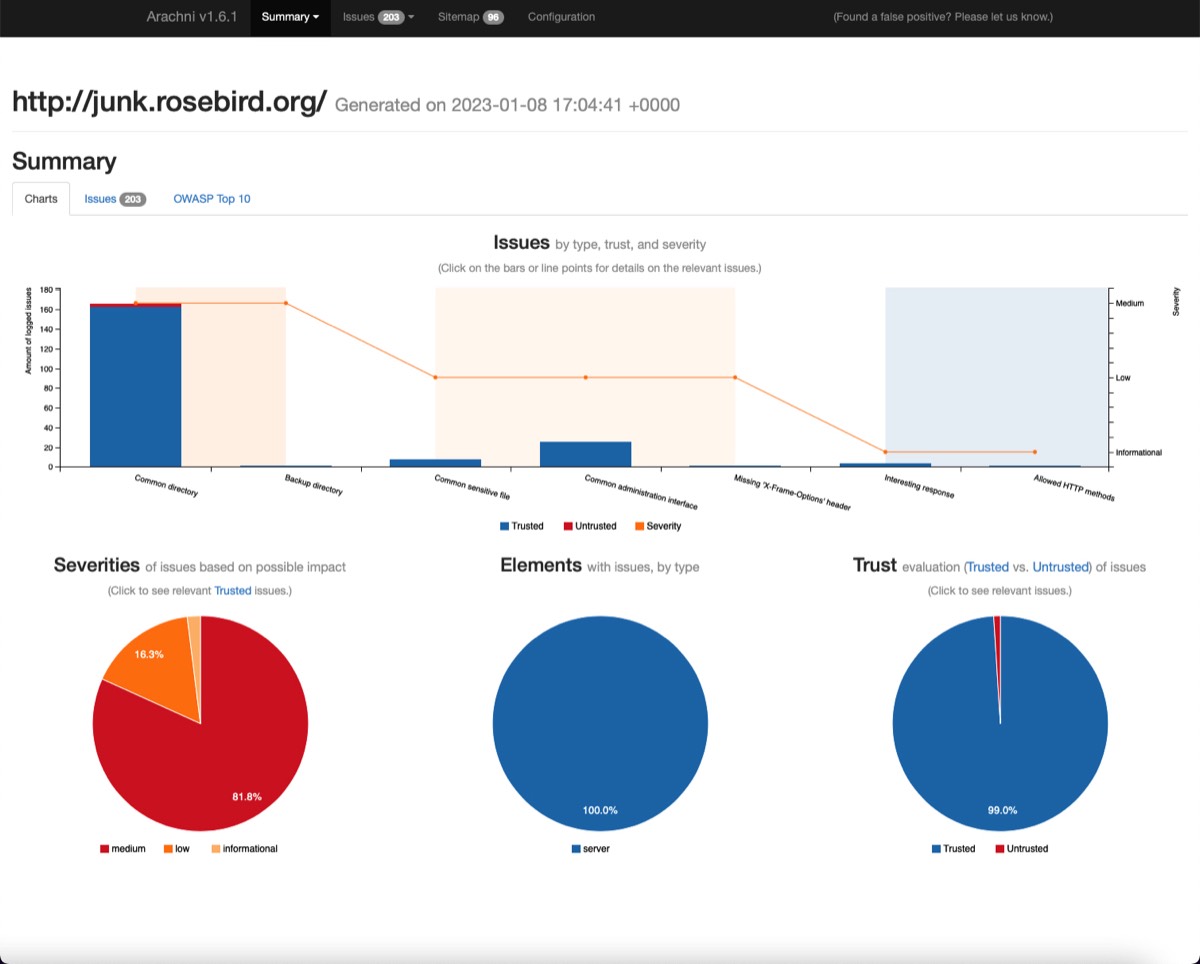
Image Title
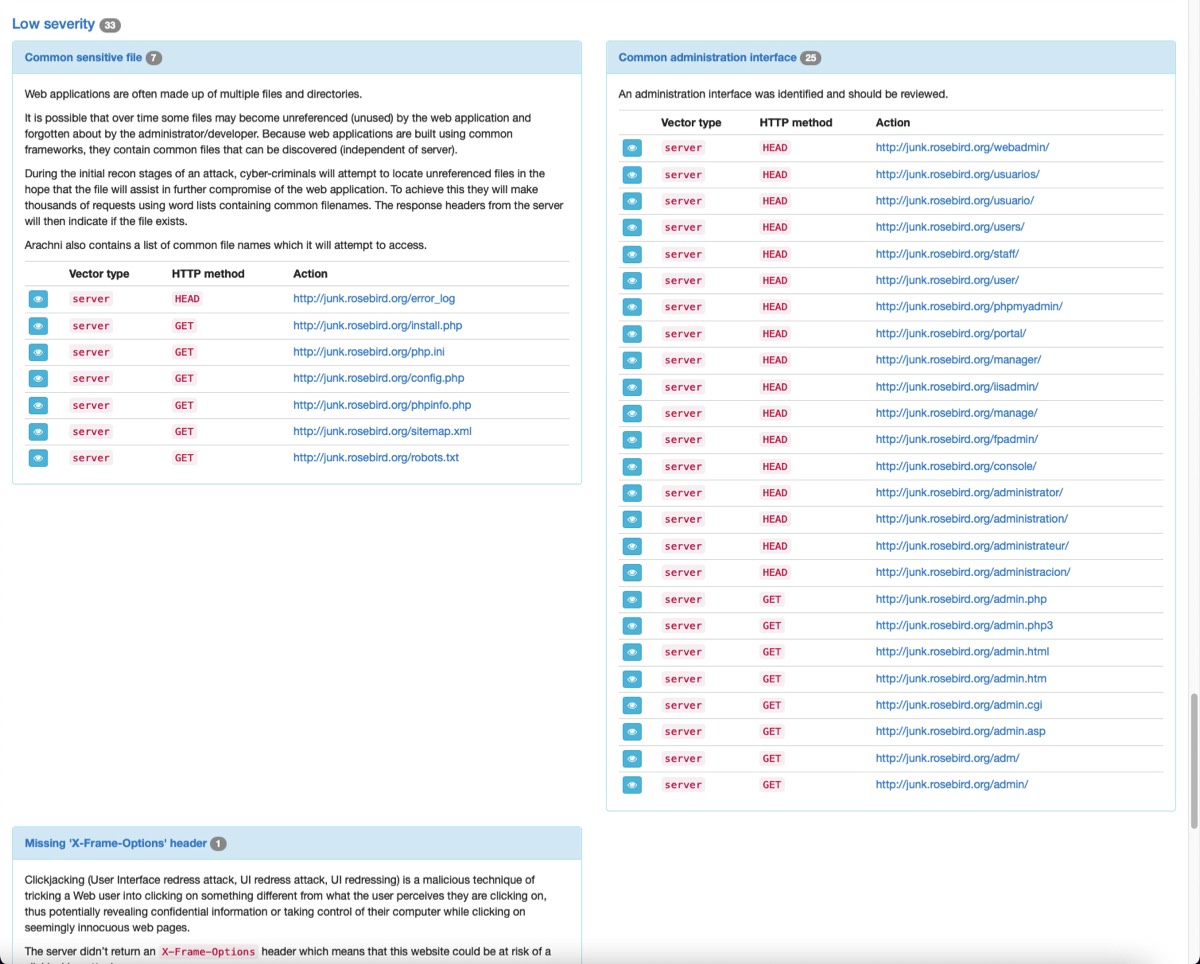
Image Title

Image Title
Image Title
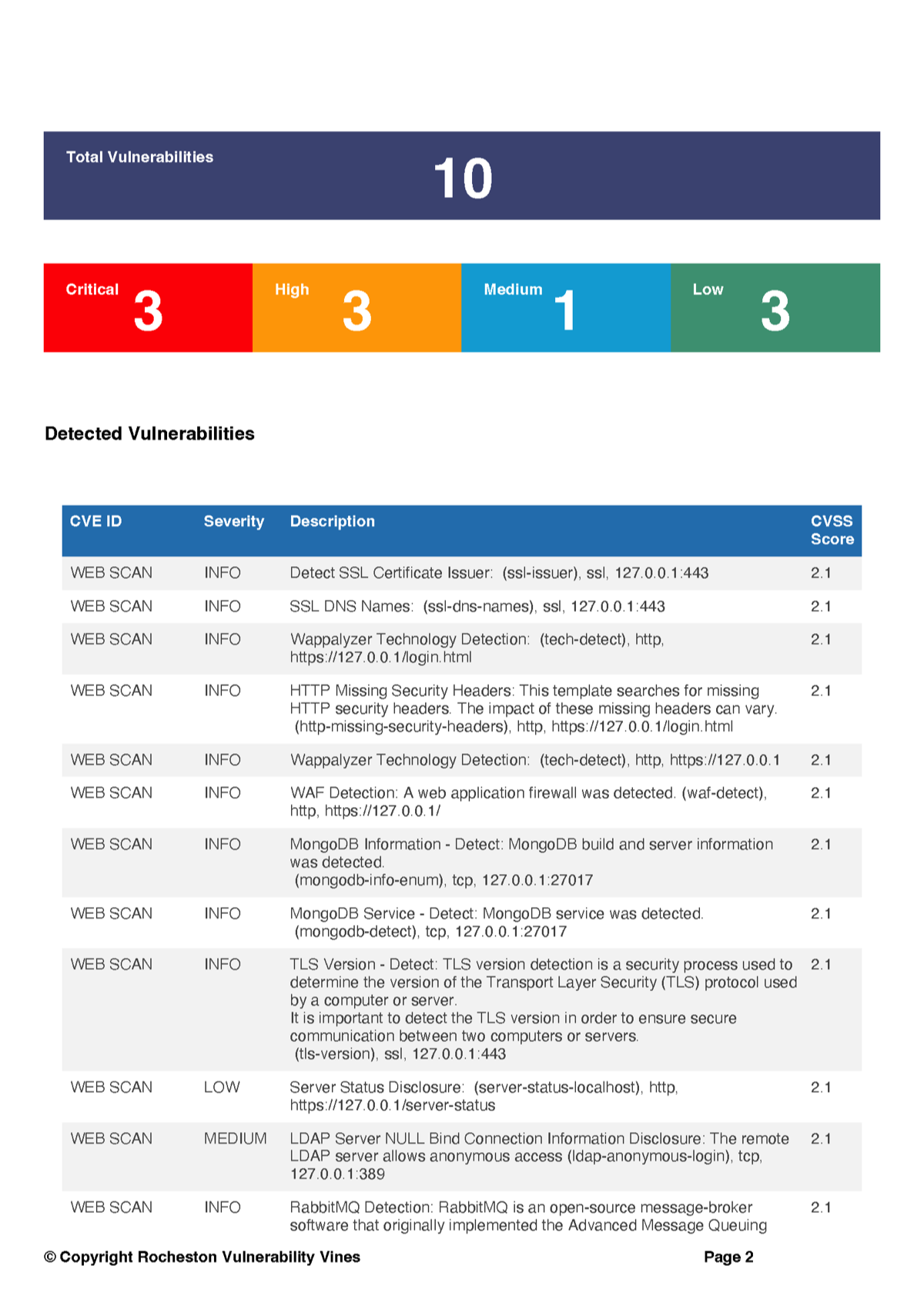
Image Title
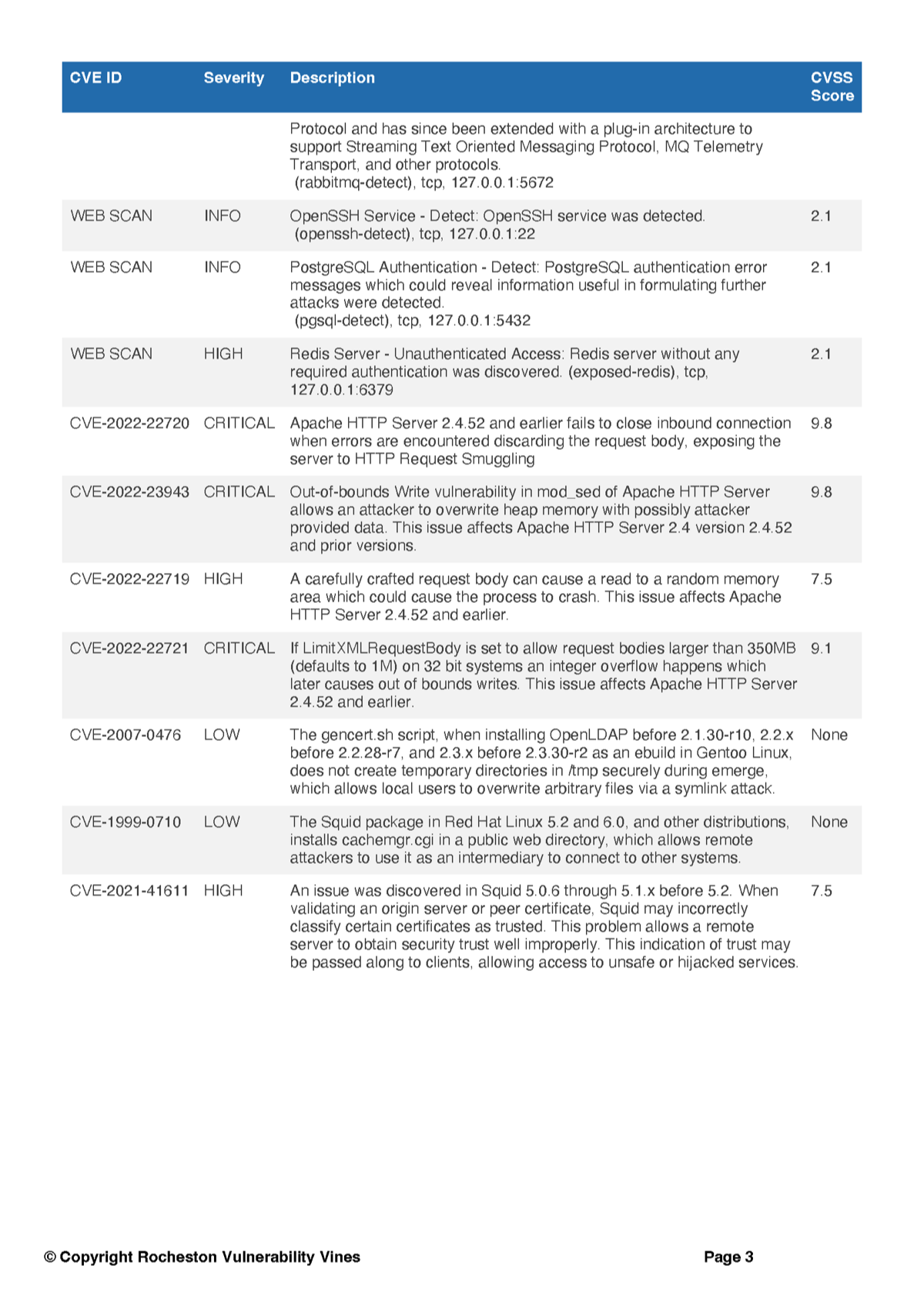
Image Title
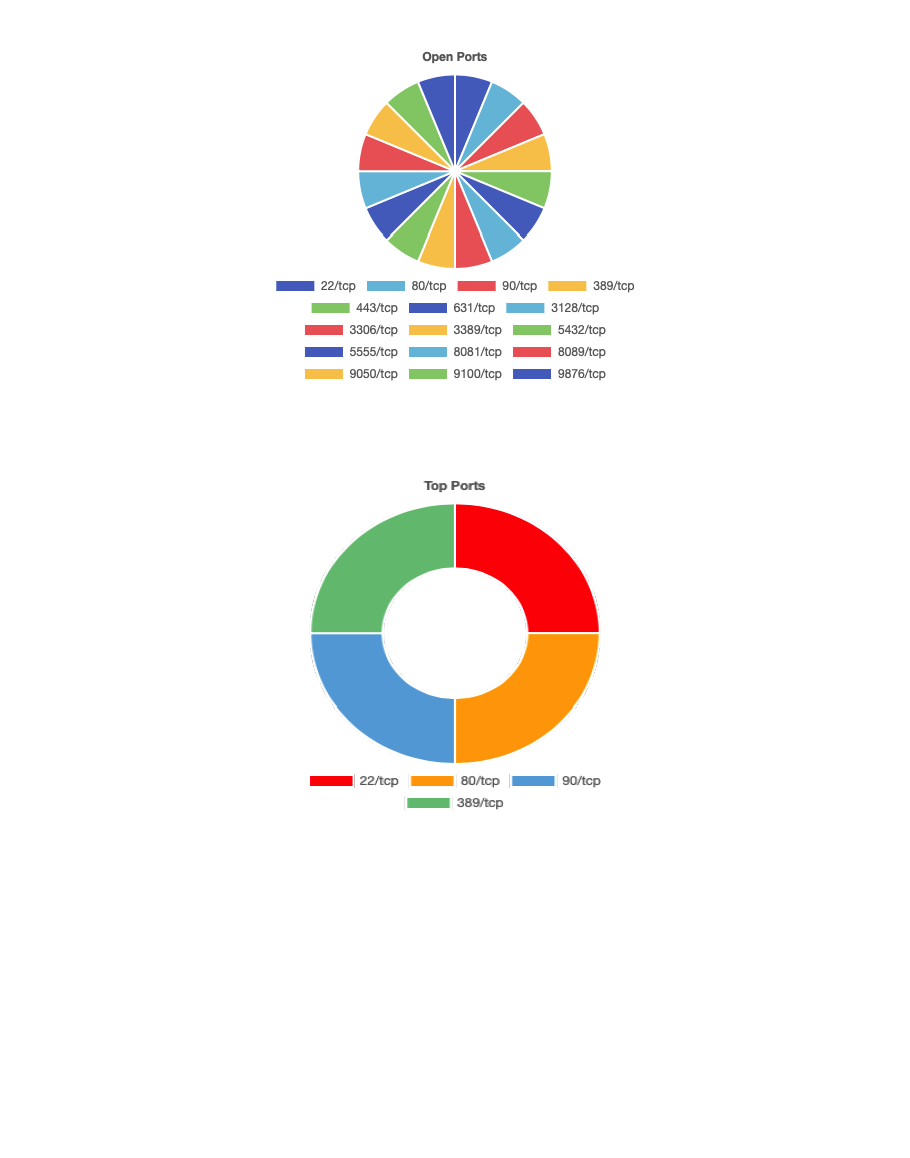
Image Title
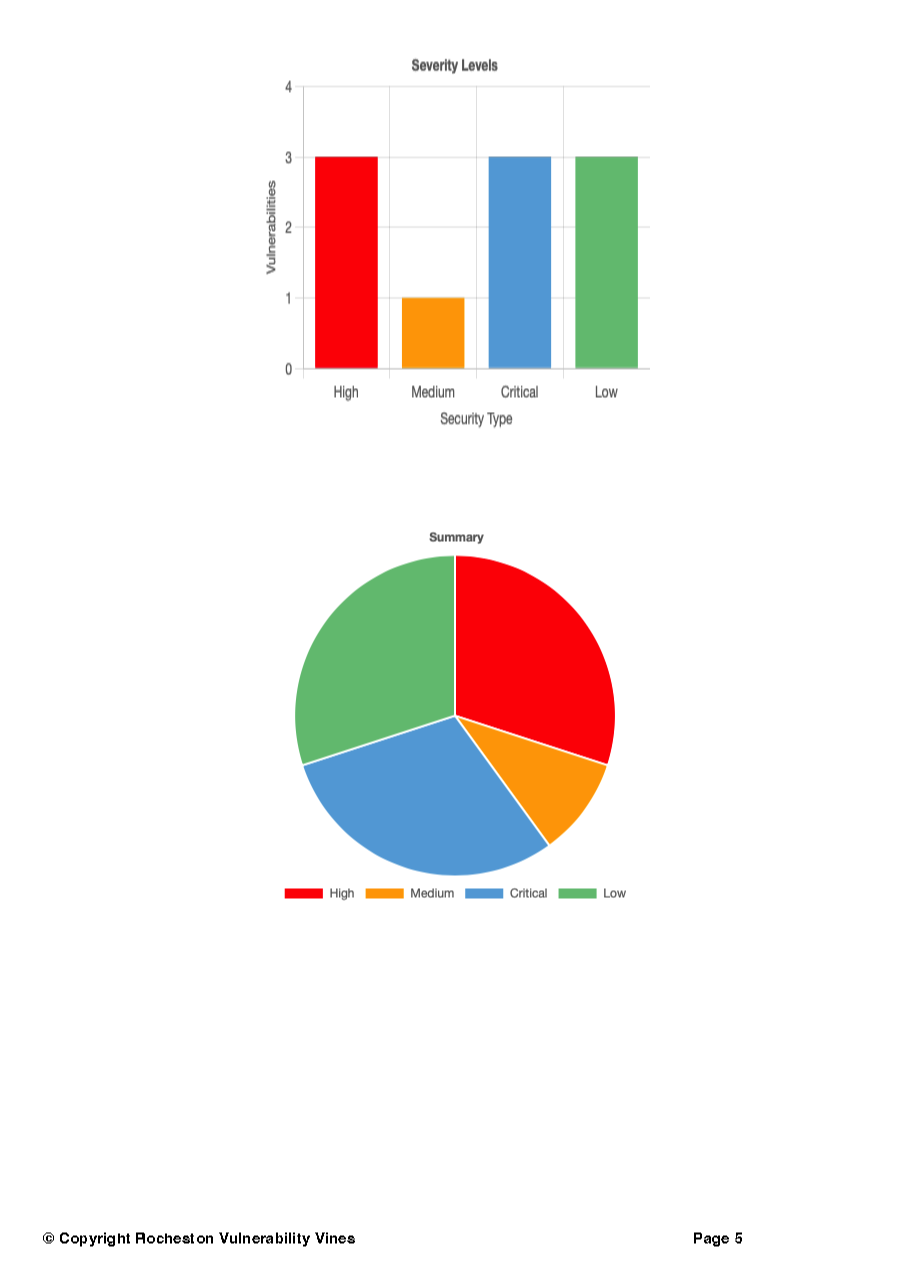
Image Title
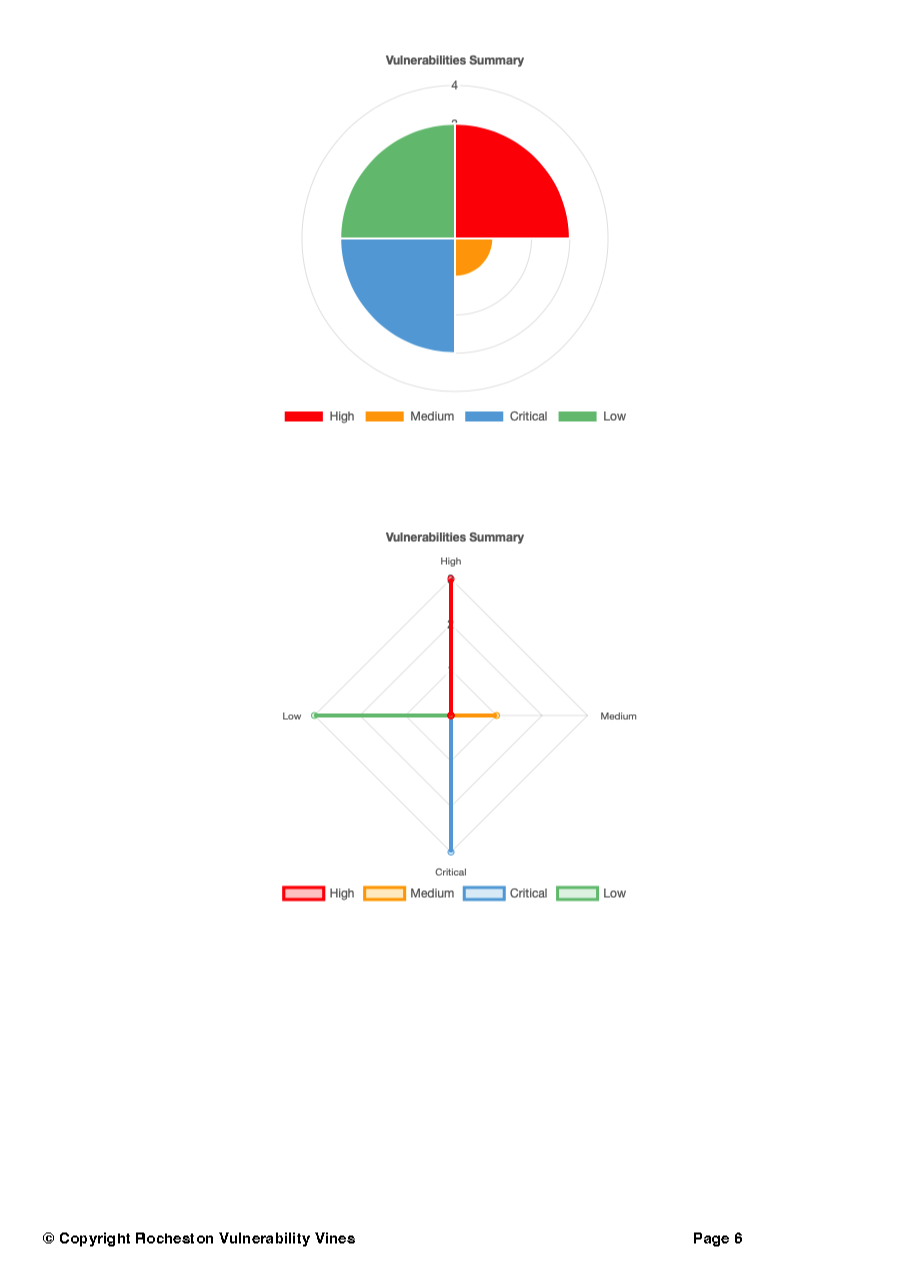
Image Title
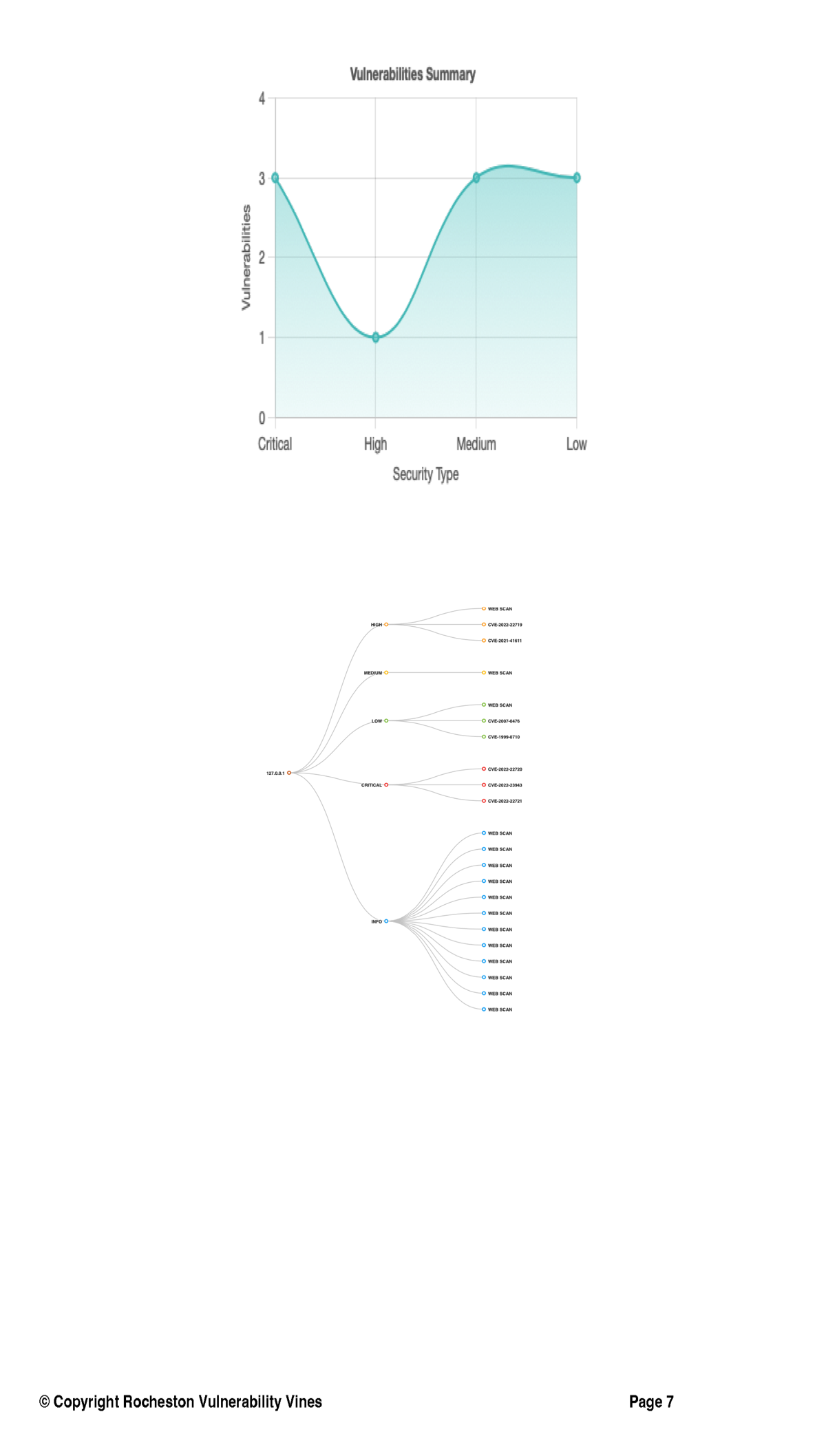
Image Title
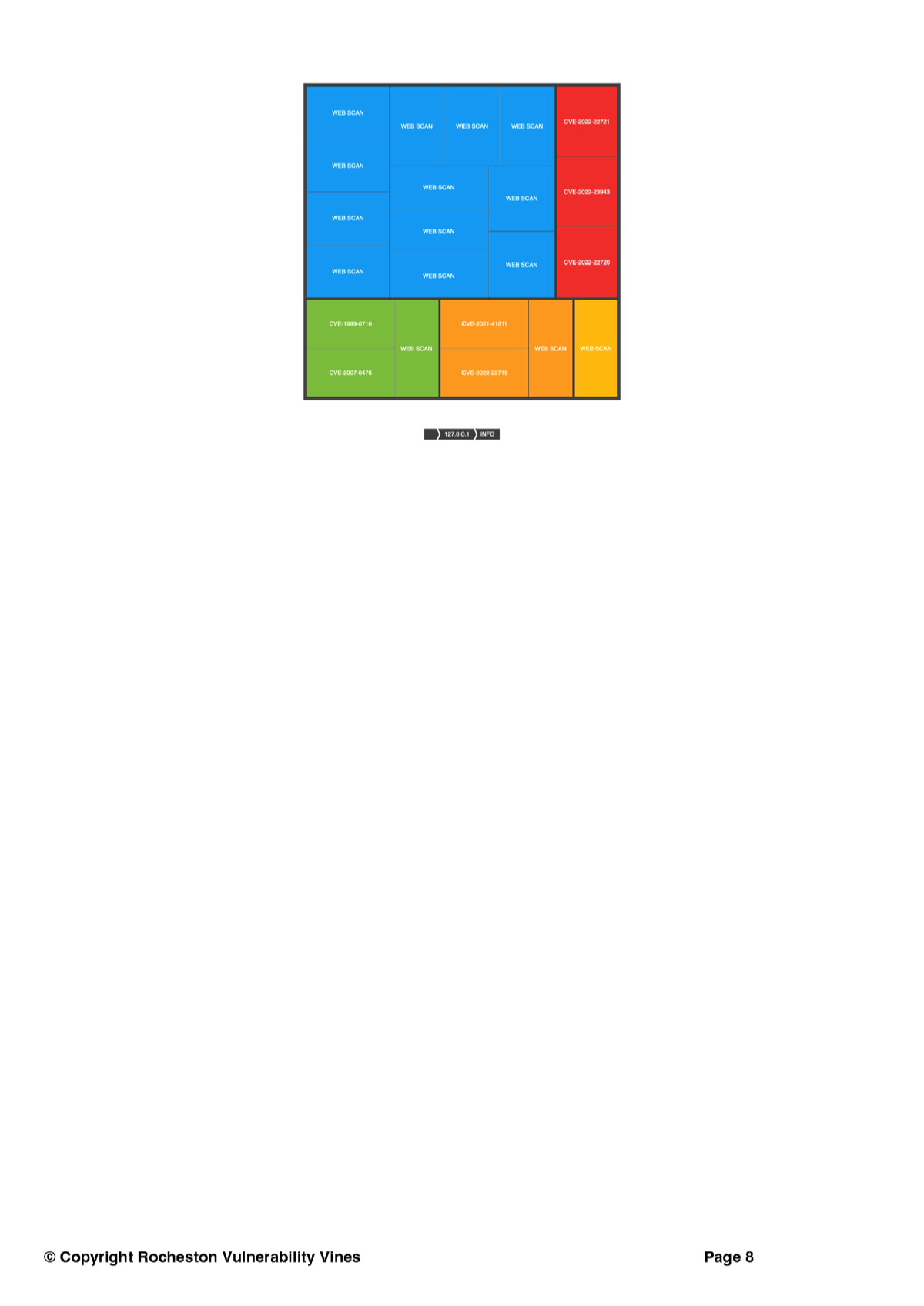
Image Title


Copyright 2023 Rocheston