Containers are everywhere, and they are one of the enabling technologies that make DevOps and DevSecOps possible, or at least make them easier and more fun to do.
Scott Young
DevSecOps
DevSecOps operates on a simple principle: every individual taking part in the software development lifecycle is accountable for security, bringing operations and development together with security functionality. It intends to integrate security in every part of the development process. It is about automating core security tasks by integrating security controls and processes earlier on in the DevOps workflow. The Significance of DevSecOps
Application deployment in the cloud has improved both scale and speed, and the shift to DevOps and Agile methodologies makes big bang app launches an issue of the past. Specifically, DevOps: integrating IT ops and development under a single categorization has resulted in more regular feature updates, and enhanced app stability.Compliance and security scanning utilities have not kept up with the rate of evolution, as they weren’t coded to evaluate code at the rate that DevSecOps needs. This has reinforced the opinion that security is the largest obstacle to swift application development. And on a broader level, an obstacle to information technology innovation.
The purpose and intent of DevSecOps is to build on the mindset that ‘everyone is responsible for security’ with the goal of safely distributing security decisions at speed and scale to those who hold the highest level of context without sacrificing the safety required.
For agile, high performance businesses, DevSecOps is an integral component. App security was mostly second thought, and viewed as a barrier to staying on top. Given the dependence on applications to sustain operations, cracking security is thought of as a high-risk strategy. Distributed or permanent denial-of-service could easily catch someone unawares. For instance, look at the consequences of failing to update the Apache Struts framework as experienced by Equifax. Rocheston Certified DevSecOps Engineer (RCDE) is intended to change this.
Power of Automation
From the beginning automation reduces the chances of human error. Human error causes downtimes and attacks. This reduces the need for security architects to manually setup security consoles. Innovation with Security
Security functionalities such as identity and access management (IAM), vulnerability scanning, and fire-walling can be enabled programmatically through the DevOps lifecycle, giving security teams the freedom and leeway to establish policies. Security can build things which are innovative, in addition to being secure.DevSecOps is the Future
Research predicts that DevSecOps, which is mildly different from SecDevOps will be embedded into 80% of rapid development teams by the year 2021.Everyone is Responsible
DevSecOps is proactive and positive, in the sense that it puts the onus on everybody with regards to security responsibilities. Tools with Enhanced Security
This has resulted in the creation of tools and techniques that are intended to provide enhanced security at several stages of the DevSecOps cycle. Others, have adopted a more aggressive viewpoint. Understanding security is how DevSecOps works.
Who Will Employ An RCDE
As vulnerabilities increase in frequency, scope, and magnitude, efficiency becomes key. Businesses need to do more with less. DevSecOps has demonstrated potential to be an integral part of business strategy. Security and compliance are increasingly required as 'services' within industry, and DevSecOps has immediate relevance to any sector where this is the case.
- Businesses with Continuous Delivery toolchain architectures
- Compliance units
- Information Technology Sector
- Project Management Teams in Business
- Quality Assurance Units
- Site reliability units
- Software engineering companies
- Testing teams
Why Choose RCDE
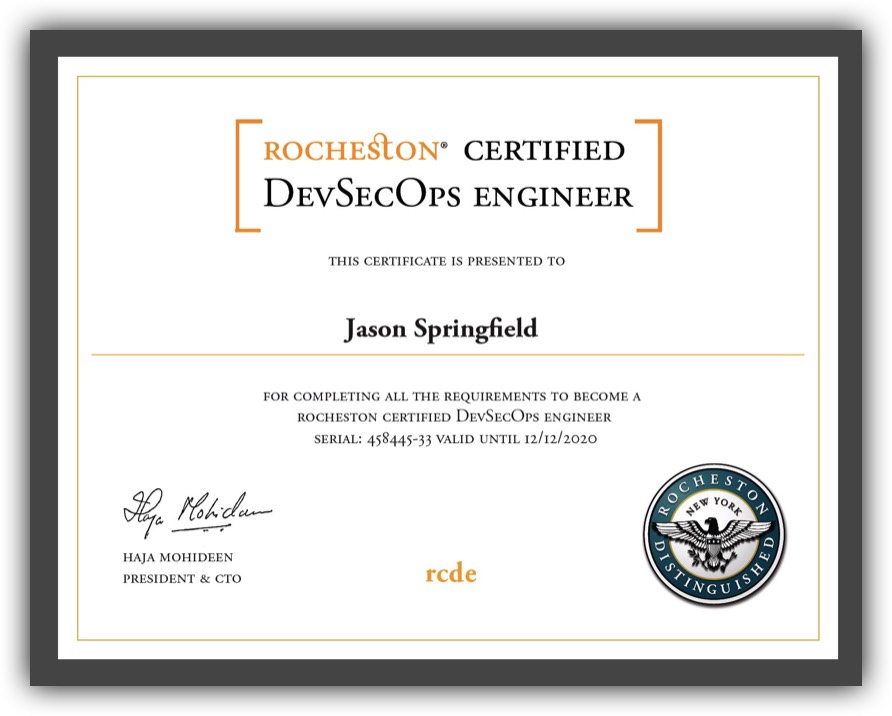
The RCDE (Rocheston Certified DevSecOps Engineer) is designed to provide insight into the nascent field of DevSecOps. DevSecOps, in very simple terms, is DevOps injected with security. Students will be instructed on the benefits, theories, purposes, and vocabulary of DevSecOps.
RCDE is developed with simple, yet in-depth content, that is accessible and informative. The course teaches ways in which security is combined with DevOps — it also teaches how data and security science can be leveraged to protect a business and its clients.
Need for RCDE
Businesses are interacting with the cloud in new ways. Apps built using the existing DevOps methodology are migrating to the cloud. As IT migrates to the cloud, this enables scalability and flexibility of on-demand resources. These complex applications need enhanced security, as they are prone to experiencing a plethora of issues — these range from misconfigured servers to bad code.
DevOps protocol needs to look more than just ops and IT teams. IT security should play a fundamental role in the app lifecycle. Security as a collaborative feature is one of the primary goals of DevSecOps. Organizations are required to integrate security from the start of the business cycle, and understand the processes that require automation to enhance speed and agility.
Integration Of Security Into Devops
Security integration into DevOps needs new mentalities, processes, and utilities. Risk administration and security leaders are required to adhere to the collaborative, agile nature of DevOps. This is needed for smoothness in the developmental process, rendering security silent and seamless. This is more complicated than it sounds.
DevOps is concerned with services being more aligned to agile approaches. When infrastructure is treated as code, the element of security is rarely paid attention to. There are two schools of thought, one subscribes to DevOps, and the other subscribes to the DevSecOps process. These schools need to be aligned to make sure that security is integrated into the decisions and lifecycle of all aspects of the process.
Insight is needed on the current lifecycle and process. What are the pitfalls with regards to adding security? Are there champions that understand how it works? Are they equipped to act and help bring in change? After the foundation has been figured out, it’s about taking action.
This collaboration requires to be properly evaluated. When writing code in the dev factory, is vulnerability checking done during the local build process? Is this done within the CI/CD process using Jenkins? Or is there a security element checking for code security during each build process?
One of the main challenges currently faced is the fact that businesses don’t care about security for security’s sake. They invest in security as a way to reduce risk. Most organizations have clear procedures and protocol to handle and manage risks. Security policies are derived from this. These policies, essentially need to be baked into DevSecOps.
What will be the future for an RCDE?
- Better Results - This is the result of combined development, security/ops teams, reduction of feedback loops and incidents, and enhanced security through sharing of responsibilities. The turn around times to patch vulnerabilities is a big indicator of how effective your application security program is.
- Efficiency - With vulnerabilities discovered during static analysis, average companies take 113 days. DevSecOps companies accomplish this in a mere 51 days. For non DevSecOps companies, a 10-day rectification TAT was 15% —for DevSecOps companies, this percentage skyrocketed to 53%.
- Skilled Developers - There is a dearth of security practitioners with knowledge in DevOps. A wide range of solutions, and alarge mindshare is absent, specifically in smaller startups.
- Secure Environment - DevOps cases evolve due to infrastructure, policies, and business requirements. Specialists are confident that these challenges can be surpassed, that they will eventually drive secure applications, and lesser vulnerabilities.
- Increased Demand - A CAGR of 33.7% is predicted during the forecast period 2017—2023. Rising security breaches, increased awareness, need for SDLC improvement, and increasing developmental activities have led to the demand for DevOps.
- New Technologies Support DevSecOps - AI, automation, and cloud technologies, are expected to support the DevSecOps market. The market is analyzed by regions, deployment type, and enterprise type.
- Increased Need for Security - Companies with mature practices are rapidly adopting automated security in multiple DevOps phases. They are 338% likelier to integrate automated security over organizations that lack DevOps.
- Industry Recognizes Application Security Tools - This is more than twice the response rate of those without a DevOps practice, demonstrating an obvious shift to containerization when DevOps has been used.
- Dynamic Application Analysis Is Critical - Deep dynamic vulnerability scans identify vulnerabilities which may be missed by other scanners that evaluate only packages. This discovers runtime vulnerabilities, such as SQL Injections in web applications or vulnerabilities in services not installed via packages.
Course Structure
The RCDE is a five-day interactive program taught by qualified engineers from all around the globe. It is set to be conducted in locations the world over. The sessions will be conducted in top-of-the-line star hotels. Our facilities are luxurious, cutting edge, and state-of-the-art.
Course Contents
- RCDE is a five day training module
- The timings are 9:30AM to 6:00PM
- A web portal will be provided to students
- The seminars are set to be conducted by SMEs and engineers
- Top-of-the-line environment and infrastructure
- Proctored qualification examination to be written on the last day on the VUE platform
Simply put, things always had to be in a production-ready state: if you wrote it, you darn well had to be there to get it running.
Mike Miller
Cost
- Course fee - USD 1299
- Exam fee - USD 799
- Exam retake fee - USD 400
Rocheston Certified DevSecOps Engineer
This certificate will open many doors for you. DevSecOps Engineers are the most sought after professionals in the tech industry today. Rocheston can help you in your amazing journey as an Artificial Intelligence expert with access to its exhaustive course materials, interactive sessions and innovative training solutions. Organizations are focussing on various business applications of AI on the enterprise level and that is exactly where Rocheston would want you to fit in!